Showing 7 results
54:33
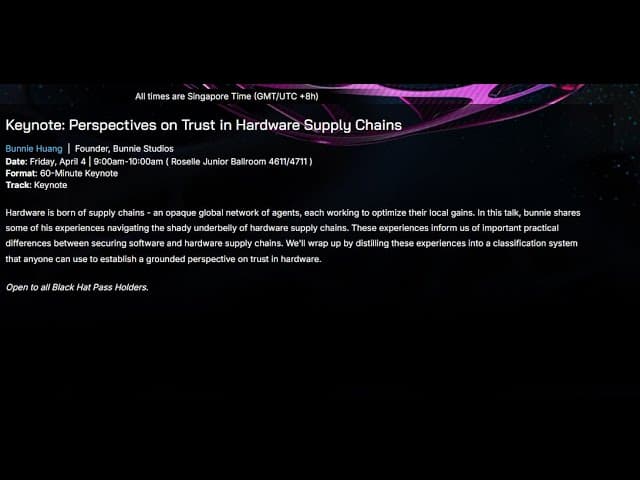
Travel & Eventskeynotehybridhardware-security

45:07
Remote Exploitation of Nissan Leaf: Controlling Critical Body Elements from the Internet
Black Hat
5 months ago
Travel & Eventsresearch-presentationtechnical-deep-diveautomotive

30:13
Unveiling New Attack Vectors in Bluetooth Vulnerability Discovery through Protocol State Machine
Black Hat
6 months ago
Travel & Eventsresearch-presentationhybridbluetooth

43:13
A Closer Look at the Gaps in the Grid: New Vulnerabilities and Exploits Affecting Solar Power
Black Hat
6 months ago
Travel & Eventsresearch-presentationhybridsolar-power

43:23
DEF CON 33 - One Modem to Brick Them All -Vulns in EV Charging Comms - Jan Berens, Marcell Szakaly
DEFCONConference
6 months ago
Science & Technologyresearch-presentationhybridev-charging

29:53
Travel & Eventsresearch-presentationhybridautomotive

36:35
Travel & Eventsresearch-presentationhybriddashcam