Running a Software Defined Radio Capture the Flag using challengectl
This talk demonstrates the implementation and operation of a Radio Frequency (RF) Capture the Flag (CTF) competition using the custom 'challengectl' software. It details the technical requirements for creating RF challenges, including legality, solvability, and repeatability, while emphasizing the use of Software Defined Radio (SDR) hardware. The presentation covers the architecture of an SDR-based challenge system, including the use of multiple SDR devices for simultaneous challenge transmission and the integration of various digital modes. The speaker also provides a practical demonstration of using 'challengectl' to manage and transmit RF signals for competition.
Building a Scalable RF Capture the Flag Range with Challengectl
TLDR: Running a high-fidelity Radio Frequency (RF) Capture the Flag (CTF) requires balancing hardware reliability with signal complexity. This post explores the architecture of an SDR-based range using challengectl, a tool designed to automate signal transmission across multiple software-defined radios. By moving from manual replay attacks to automated, scriptable signal generation, researchers can build more complex and repeatable wireless training environments.
Wireless security research often hits a wall when it comes to scale. While a single replay attack against a key fob is straightforward, building a multi-user, multi-challenge RF range that doesn't fall apart under the pressure of a conference floor is a different beast. The challenge lies in the hardware: keeping multiple SDRs synchronized, managing signal interference, and ensuring that every participant gets a clean, consistent signal to decode.
The challengectl framework, as demonstrated at DEF CON, solves this by treating RF signals as code. Instead of relying on static, pre-recorded IQ files that are prone to noise and timing issues, this approach uses Python-based automation to generate signals on the fly. This shift from "capture and replay" to "generate and transmit" is the key to creating a professional-grade wireless CTF.
The Architecture of an SDR-Based Range
At the core of a robust RF range is the ability to manage hardware state. When you are running 15 or 16 different flags simultaneously, you cannot afford to have a single SDR hang or drift off frequency. The system architecture described in the talk relies on a centralized controller that manages a pool of SDRs, such as the HackRF or BladeRF.
The controller script performs three critical functions: it checks device availability, assigns specific challenges to specific radios, and handles the timing of transmissions. By using a database to synchronize these tasks, the system ensures that multiple challenges can be broadcast across the spectrum without collision. This is a massive upgrade over the "one radio, one challenge" model, which quickly becomes unmanageable as the number of participants grows.
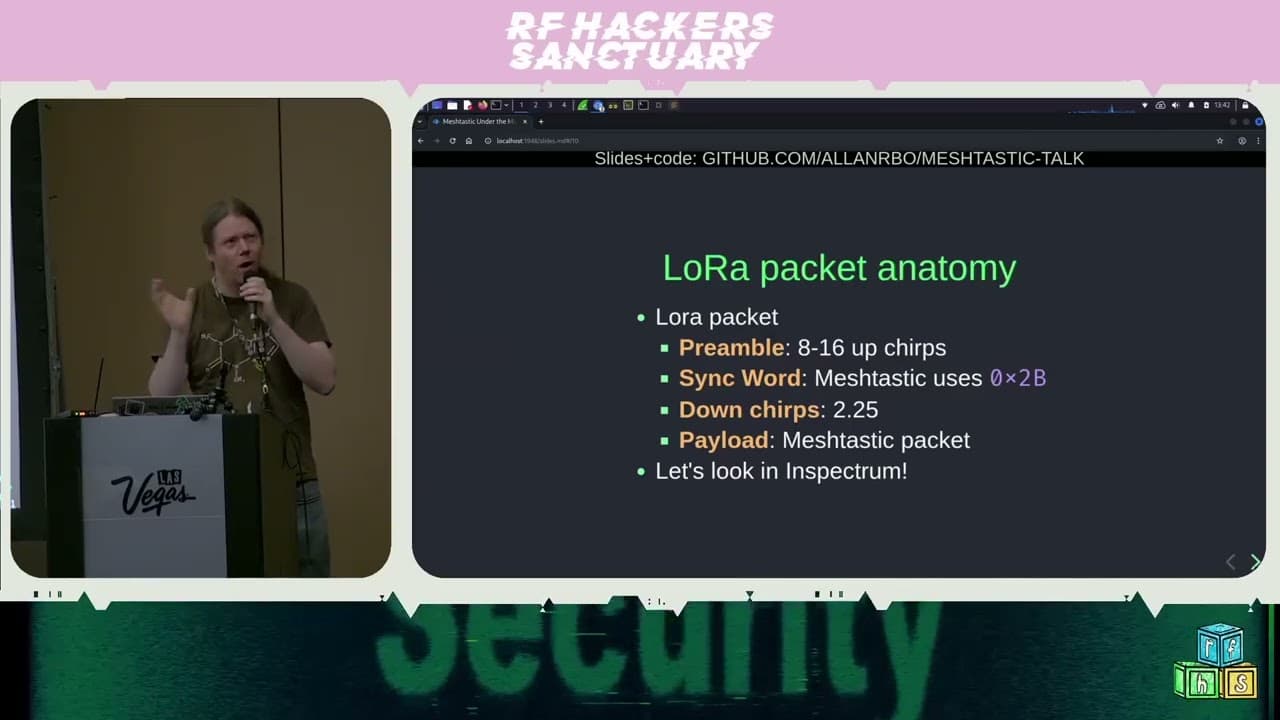
Moving Beyond Simple Replay Attacks
Most entry-level wireless challenges rely on simple replay attacks. While these are great for teaching the basics of OWASP IoT security, they don't reflect the reality of modern, encrypted, or rolling-code systems. To push the technical bar higher, you need to simulate complex digital modes.
The integration of fldigi and multimon-ng into the challenge pipeline allows for the transmission of diverse protocols like POCSAG paging, APRS, or various amateur radio digital modes. By generating these signals programmatically, you can introduce intentional errors or variations in the signal, forcing participants to actually understand the protocol rather than just blindly replaying a captured packet.
For example, when generating a POCSAG signal, the controller can inject specific data payloads that change based on the participant's progress in the CTF. This dynamic generation is what separates a static, boring range from a truly engaging, interactive environment.
Practical Implementation for Pentesters
If you are building a lab for internal training or a red team exercise, the lessons here are clear. First, standardize your hardware. Using a mix of different SDRs will lead to driver conflicts and inconsistent power output. Stick to a single platform, like the BladeRF 2.0, to ensure that your gain settings and frequency accuracy are predictable across the entire range.
Second, automate your spectrum management. If you are testing a system that uses multiple frequency bands, you need to account for harmonic interference. The GQRX software is an excellent tool for visualizing your spectrum before you go live, allowing you to identify potential collisions between your challenge signals and the ambient noise of the environment.
When you are on an engagement, the ability to quickly stand up a localized RF range can be the difference between a successful assessment and a missed finding. If you are testing an industrial control system or a proprietary wireless sensor network, don't just look for vulnerabilities in the software. Use an SDR to capture the raw traffic, analyze the modulation, and then use a tool like Universal Radio Hacker to identify the underlying protocol structure.
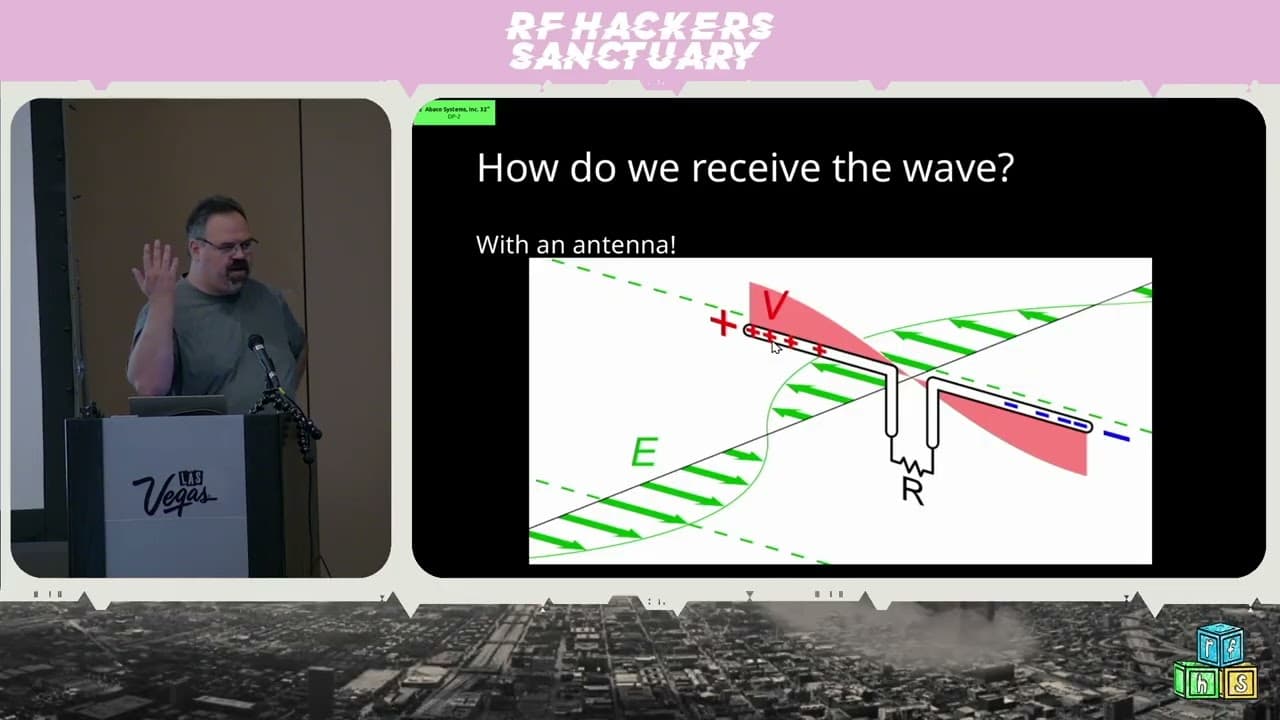
Defensive Considerations
Defenders often overlook the physical layer because it feels like "magic" that is too difficult to secure. However, the same principles that make a good CTF also make a good defense. If your wireless system is vulnerable to a simple replay attack, you are already behind. Implement rolling codes, challenge-response authentication, or at the very least, signal strength verification to prevent basic proximity-based attacks.
The goal of any wireless security program should be to move away from "security by obscurity" at the radio level. If your protocol can be decoded by a $300 SDR and a bit of Python, it is not secure. Treat your RF signals with the same level of scrutiny you apply to your web APIs.
Building a range is the best way to understand the limitations of your own wireless infrastructure. Whether you are using challengectl to teach your team or to test a new device, the shift toward programmatic signal generation is the future of wireless security research. Start small, focus on one protocol at a time, and don't be afraid to break things in the lab before they break in production.