Meshtastic Under the Microscope: From Chirps to Chat
This talk demonstrates the reverse engineering of the LoRa-based Meshtastic protocol to understand its physical layer modulation and application-layer packet structure. The speaker analyzes the Chirp Spread Spectrum (CSS) modulation used by LoRa and the Protobuf-based message format employed by Meshtastic. The presentation provides a practical guide for intercepting, decoding, and crafting custom packets using Software Defined Radio (SDR) and custom Python scripts. The session concludes with a live demonstration of packet injection and decoding using Wireshark.
Reverse Engineering the Meshtastic Protocol: From RF Chirps to Custom Packet Injection
TLDR: Meshtastic provides off-grid, long-range communication, but its reliance on LoRa modulation and a custom Protobuf-based application layer creates a false sense of security for many users. By leveraging Gqrx and Inspectrum, researchers can easily visualize and decode these transmissions to reveal cleartext metadata and message content. This post breaks down how to intercept, analyze, and inject custom packets into a Meshtastic network using an HackRF and basic Python scripting.
Security researchers often overlook the physical layer of IoT devices, assuming that if a protocol is "off-grid" or uses proprietary radio hardware, it is inherently difficult to intercept. Meshtastic, a popular open-source project for long-range, off-grid messaging, relies on LoRa modulation to achieve its impressive range. While the application layer uses AES-256 encryption, the underlying radio implementation is surprisingly accessible to anyone with a cheap Software Defined Radio (SDR) and a bit of patience. If you are testing an environment where Meshtastic is used for critical communication, you cannot treat the radio link as a black box.
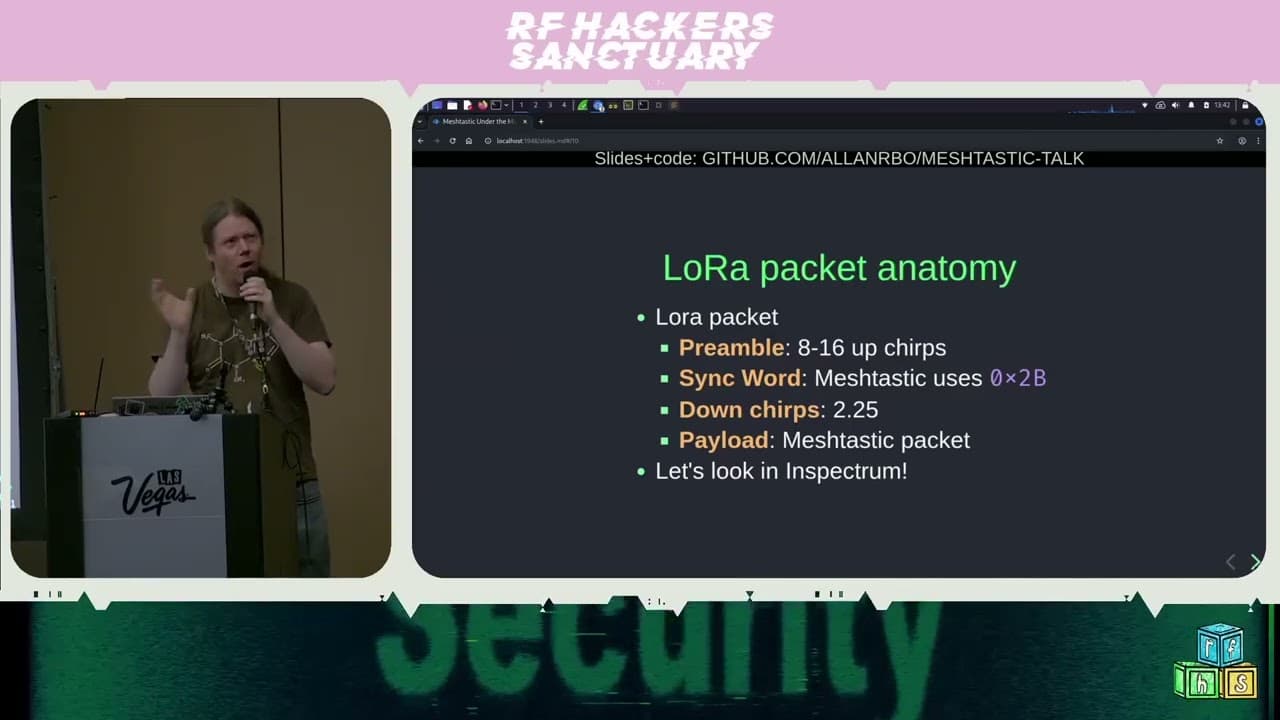
Decoding the Physical Layer
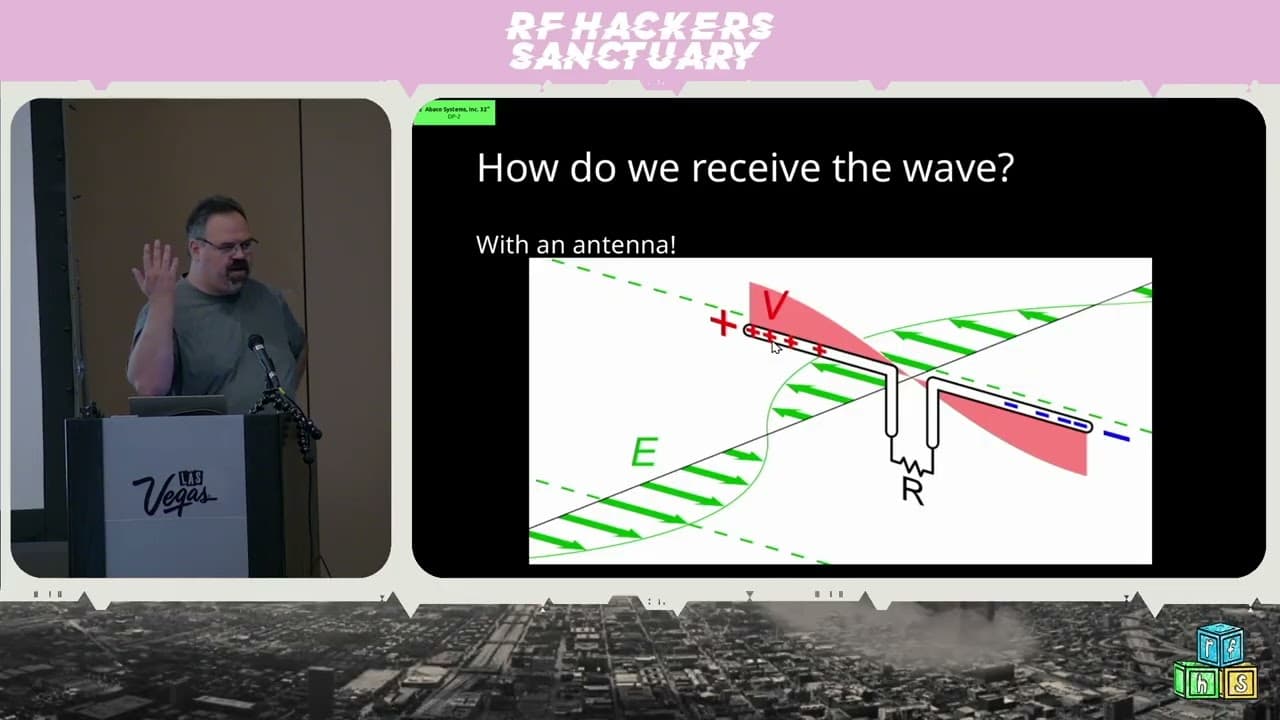
LoRa uses Chirp Spread Spectrum (CSS) modulation. Instead of traditional frequency-shift keying where a bit is represented by a static frequency, LoRa uses "chirps"—signals that sweep across a frequency band over time. To a standard waterfall display, these look like diagonal lines.
The first step in analyzing this traffic is capturing the raw IQ data. Using Gqrx, you can tune to the common 915 MHz ISM band (or your local equivalent) and record the bursts. Once you have a capture, Inspectrum is the go-to tool for visualization. By zooming in on the chirps, you can see the preamble—a series of repeated up-chirps used by the receiver to synchronize its clock.
The magic happens when you "dechirp" the signal. By multiplying the received signal by the conjugate of an ideal down-chirp, you effectively flatten the frequency sweep into a constant frequency. This transforms the complex CSS signal into something that looks and behaves like standard Frequency Shift Keying (FSK). Once you have this constant frequency, you can perform an N-point Discrete Fourier Transform (DFT) to extract the underlying symbols. In the case of Meshtastic, these symbols represent the data bits being transmitted.
From Symbols to Protobuf
Once you have the symbols, you need to map them back to the application layer. Meshtastic uses Protocol Buffers to serialize its data. This is a massive advantage for a researcher. Because Protobuf is a structured binary format, once you identify the message schema, you can easily parse the captured bytes.
The packet structure is straightforward: a 16-byte header containing the destination, sender, and a channel hash, followed by the encrypted payload. The channel hash is particularly interesting—it is derived from the channel name and the pre-shared key (PSK) using an XOR operation. If you have the PSK, you can decrypt the payload. Even without the PSK, the header is often sent in the clear, allowing you to map the network topology, identify active nodes, and track message frequency without ever breaking the encryption.
Crafting and Injecting Packets
The most dangerous part of this research is how easily you can craft your own packets. Because the protocol is open source, you don't need to reverse engineer the firmware to understand how to build a valid packet. You can simply use the existing Meshtastic source code as a reference.
I built a simple Python script that handles the packet construction, including the Protobuf serialization and the AES-256-CBC encryption. By piping this data to an Arduino equipped with a LoRa radio, you can inject your own messages into the mesh.
# Simplified packet construction logic
data_plain = mesh_pb2.Data()
data_plain.portnum = mesh_pb2.TEXT_MESSAGE_APP
data_plain.payload = "Hello World".encode('utf-8')
# Encrypt the payload using the pre-shared key
data_enc = aes_encrypt(PSK, SENDER, packet_id, data_plain)
# Construct the header
hdr = struct.pack('<IIIBBBB', DEST, SENDER, packet_id, flags, ch, 0, 0)
packet = hdr + data_enc
This bypasses the entire radio stack. You aren't just sniffing; you are participating in the network. During my testing, I found that the protocol lacks robust collision avoidance or carrier sense multiple access (CSMA/CA) mechanisms. If you flood the channel with high-frequency transmissions, you can effectively perform a Denial of Service (DoS) attack on the entire local mesh.
Real-World Implications
For a pentester, this is a goldmine. If you are assessing a facility that uses Meshtastic for security or logistics, you can easily map the entire communication network from a parking lot. You can identify which nodes are talking to each other, the frequency of their communication, and, if you manage to recover the PSK from a single compromised device, read every message sent across the channel.
Defenders need to understand that "off-grid" does not mean "secure." If you are deploying Meshtastic, assume the radio link is compromised. Use unique, strong PSKs for every channel, and never rely on the radio layer for authentication. If the integrity of the messages is critical, implement an additional layer of application-level signing or encryption.
The barrier to entry for RF exploitation has never been lower. Tools like Gqrx and Inspectrum have turned what used to be a specialized skill into a weekend project. If you are building systems on top of these protocols, start by assuming the airwaves are already being watched.
Vulnerability Classes
Target Technologies
Attack Techniques
All Tags
Up Next From This Conference
Similar Talks

Hacking Apple's USB-C Port Controller

Unmasking the Snitch Puck: The Creepy IoT Surveillance Tech in the School Bathroom