BSides Salt Lake City Closing Ceremony
This video is a closing ceremony for the BSides Salt Lake City conference. It includes announcements regarding contest winners, sponsor acknowledgments, and logistical information for attendees. The content is non-technical and does not contain any security research, vulnerability analysis, or offensive security demonstrations.
Why Community-Driven Security Events Are Your Best Source for Zero-Day Intel
TLDR: Security conferences like BSides are often dismissed as networking fluff, but they serve as the primary venue for researchers to drop novel, unpatched findings before they hit the mainstream. By focusing on the local, community-driven tracks rather than just the keynote stages, you gain access to raw, actionable research that hasn't been sanitized by corporate PR. This post breaks down why you should be paying attention to the "closing ceremony" and local track data to find your next bug bounty target or red team vector.
Security researchers often fall into the trap of thinking that the most valuable intelligence comes from expensive, high-profile industry summits. While those events have their place, the real, gritty, and often unpolished research—the kind that leads to actual CVEs—is frequently found in the smaller, community-run tracks of events like BSides. If you are a bug bounty hunter or a penetration tester, you are missing a massive opportunity if you ignore these local gatherings. The value isn't in the vendor booths or the swag; it is in the specific, niche technical discussions that happen in the hallways and the smaller breakout rooms.
The Signal in the Noise
When you attend a conference, the temptation is to sit in the main hall and listen to high-level talks about "threat landscapes." That is a waste of your time. The real signal is found in the technical tracks where researchers present their latest findings on specific target technologies. These researchers are often the same people filing reports on HackerOne or Bugcrowd. When they present, they are often showing you exactly how they bypassed a specific control or found a logic flaw in a common framework.
For example, when a researcher presents a new way to exploit a common OWASP Top 10 vulnerability, they are essentially giving you a roadmap for your next engagement. You don't need to reinvent the wheel. You need to take the technique they demonstrated, understand the underlying mechanics, and apply it to your own targets. The key is to look for the "how" rather than the "what." If a speaker shows a bypass for a specific WAF or a novel way to chain SSRF, that is your payload.
Why Local Tracks Beat Keynotes
The technical depth of a local BSides talk is almost always higher than a keynote. A keynote speaker is usually there to sell a vision or a product. A local track speaker is there to show off their research. They want to prove that they found something interesting. This is where you find the "niche" bugs that haven't been widely publicized yet.
Consider the last time you saw a talk on Cross-Site Request Forgery (CSRF) that actually showed a bypass for a modern, token-based implementation. It probably wasn't a keynote. It was likely a 30-minute talk in a room with fifty people. That is where the gold is. You can find the slides and the PoC code on the official BSides GitHub repositories or the speaker's personal page. If you aren't digging through these, you are working harder, not smarter.
Turning Research into Results
If you want to be effective, you need to treat these talks as a source of raw data. Don't just watch the talk. Download the slides, look at the code snippets, and try to reproduce the finding in a lab environment. If a speaker mentions a specific CVE, go to the NVD and read the technical analysis. Understand why the patch failed or why the vulnerability was possible in the first place.
When you are on an engagement, you should be looking for the same patterns. If a researcher found a way to exploit a deserialization vulnerability in a specific Java library, you should be scanning your target's dependencies for that same library. It is not about being a genius; it is about being a good researcher who knows where to look for the latest information.
The Defensive Reality
Defenders often struggle because they are reactive. They wait for a patch to be released or for a vendor to issue an advisory. By the time that happens, the exploit is already in the wild. If you are a defender, you should be attending these same talks. You need to know what the researchers are finding before the attackers do. If you see a talk about a new way to bypass authentication in a common SSO provider, you should be checking your own configuration immediately. You don't need to wait for a vendor to tell you that you are vulnerable.
What to Do Next
Stop looking for the "next big thing" in the headlines. Start looking for it in the local conference schedules. Find the talks that are technical, specific, and focused on the technologies you encounter every day. If you see a talk that covers a technology you use, watch it. If you see a talk that covers a technique you don't understand, learn it. The best security researchers are the ones who are constantly learning and applying that knowledge to their work.
The next time you see a call for papers for a local security event, don't just look at the titles. Look at the abstracts. Look at the technical level. And if you see something that looks interesting, go. You might just find the bug that defines your career. Don't wait for someone else to tell you what is important. Go find it yourself. The information is out there, and it is waiting for someone with the curiosity to dig it up.
Up Next From This Conference
Similar Talks
Making and Breaking NSA's Codebreaker Challenge
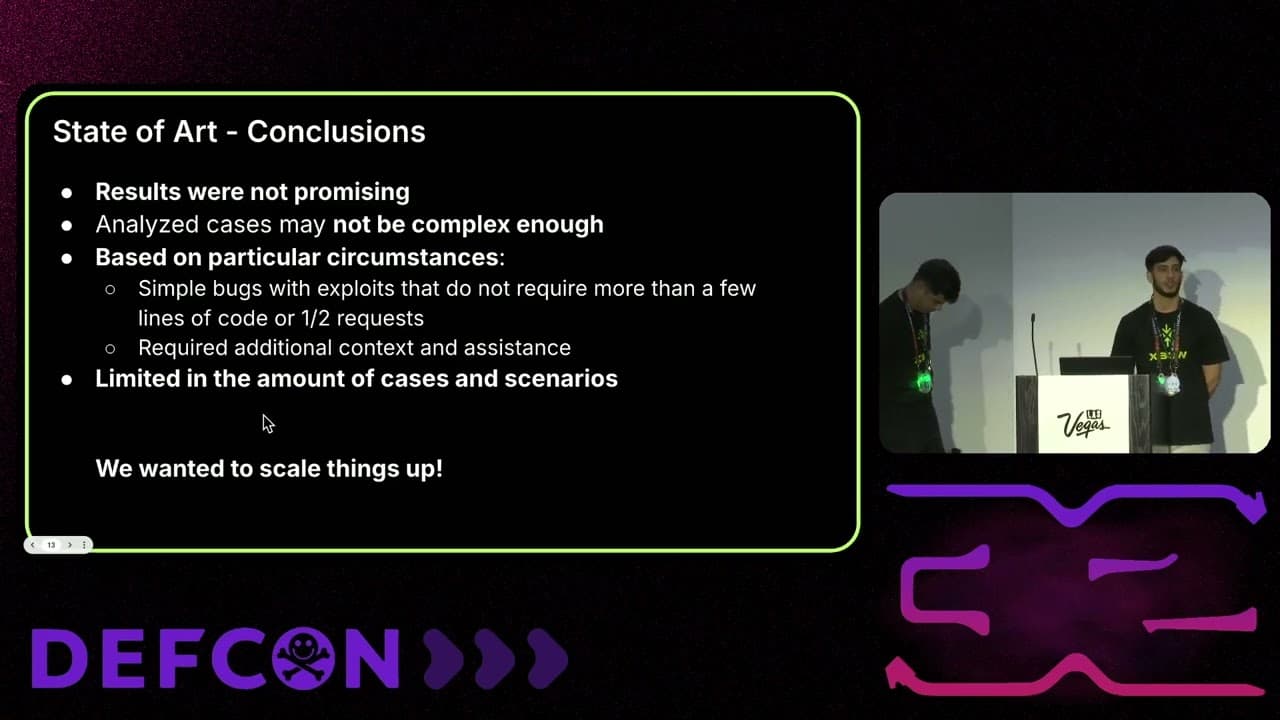
Leveraging AI for Smarter Bug Bounties




