TryHackingMy Way From Cyber Sales to Cyber SOC
This talk is a personal career narrative detailing the speaker's transition from a non-technical sales role into a Security Operations Center (SOC) position. It highlights the importance of self-directed learning, community engagement, and leveraging platforms like TryHackMe to build foundational cybersecurity skills. The presentation emphasizes the value of hands-on experience, networking, and understanding the human element in security operations.
Beyond the Sales Pitch: Why Your SOC Needs Offensive Mindsets to Survive
TLDR: Transitioning from sales to a Security Operations Center (SOC) role requires more than just certifications; it demands a shift toward an offensive mindset. By leveraging platforms like TryHackMe and engaging with the research community, analysts can bridge the gap between theoretical alerts and real-world exploitation. This post explores how integrating red team methodologies into daily SOC workflows improves detection engineering and reduces mean time to respond.
Security operations often suffer from a disconnect between the tools on the screen and the reality of an active breach. Most analysts spend their days staring at SIEM dashboards, chasing false positives, and following rigid playbooks that assume a static environment. This approach fails because it treats security as a checklist rather than a dynamic, adversarial game. If you want to move from a reactive analyst to a proactive hunter, you have to stop thinking like a defender and start thinking like the person trying to break in.
The Offensive Shift in Detection Engineering
The most effective SOC analysts I have worked with are those who have spent time in the trenches of a penetration test or a bug bounty program. They understand that an alert for a suspicious PowerShell execution is not just a line in a log; it is a specific stage in a kill chain. When you understand the mechanics of how an attacker bypasses OWASP Top 10 controls, you stop looking for signatures and start looking for intent.
Take, for example, the common reliance on automated vulnerability scanners. While these tools are necessary for compliance, they are often noise-heavy and lack the context of a human-led engagement. A seasoned researcher knows that a high-severity finding from a scanner might be a non-issue in a hardened environment, while a low-severity misconfiguration could be the exact pivot point needed for lateral movement. By running your own Metasploit modules or crafting custom payloads in a lab environment, you learn to identify the subtle artifacts that automated tools miss.
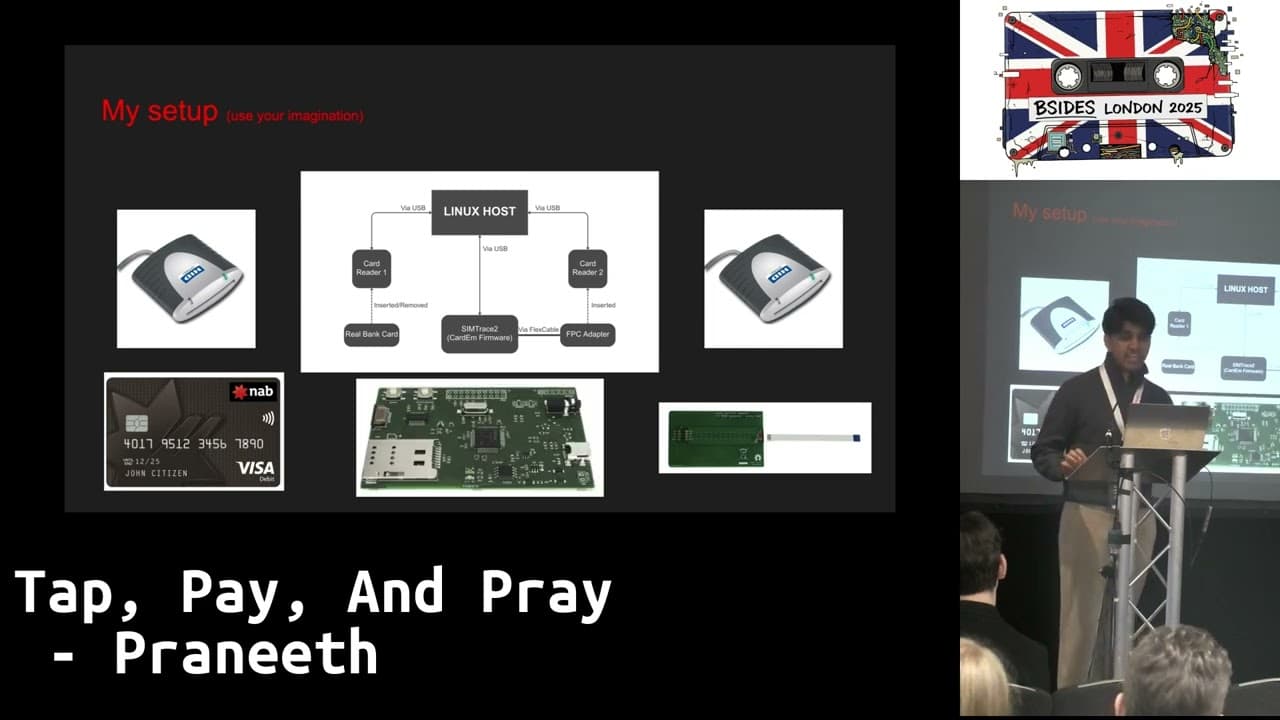
Building a Lab-First Mentality
You do not need a massive budget to build a high-fidelity detection lab. The barrier to entry for learning offensive techniques has never been lower. Platforms like TryHackMe provide structured paths that force you to think through the entire lifecycle of an attack, from initial reconnaissance to privilege escalation.
When you are in the SOC, use these platforms to replicate the alerts you see in production. If you see a weird curl command hitting your web server, don't just block the IP. Recreate that request in your lab using Burp Suite to see exactly what the payload is trying to achieve. Is it testing for directory traversal? Is it attempting to dump environment variables? Once you understand the "why" behind the traffic, you can write a detection rule that is actually resilient to minor variations in the attack vector.
The Human Element in Security Operations
Technical skill is only half the battle. The most dangerous blind spot in any organization is the human element. Attackers are not just exploiting software; they are exploiting the people who manage it. This is why understanding social engineering and the psychology of an attack is just as important as knowing how to parse a PCAP file.
During a red team engagement, the goal is often to find the path of least resistance. Frequently, that path is a human who has been conditioned to trust a specific workflow or communication channel. As a SOC analyst, you should be auditing your own processes for these same vulnerabilities. Are your incident response procedures so predictable that an attacker could use them to mask their own activity? If your team follows the same rigid steps every time an alert fires, you are essentially providing a roadmap for an adversary to stay one step ahead of you.
Bridging the Gap
If you are currently in a non-technical role or just starting your journey into security, do not let the complexity of the field intimidate you. The industry is full of gatekeepers who will tell you that you need a specific degree or a decade of experience to be effective. That is noise. What matters is your ability to learn, your willingness to break things, and your persistence in understanding how they work.
Start by picking one technology you use every day and tearing it apart. If you work with SIEM, learn how to write custom detection logic that goes beyond simple keyword matching. If you work with cloud infrastructure, learn how to use Python to automate the identification of misconfigured S3 buckets or IAM roles.
The goal is to build a "learning to learn" habit. The tools will change, the CVEs will be patched, and the threat landscape will evolve, but the ability to deconstruct an attack and understand its underlying logic is a permanent asset. Stop waiting for the next training module to tell you what to do. Find a target, build a lab, and start testing your own assumptions. The best way to defend a network is to know exactly how you would take it down.
Tools Used
Target Technologies
Up Next From This Conference
Similar Talks

Kill List: Hacking an Assassination Site on the Dark Web

Counter Deception: Defending Yourself in a World Full of Lies