Tap, Pay, And Pray
This talk demonstrates how to perform man-in-the-middle and verification downgrade attacks against EMV-enabled payment terminals. By intercepting and manipulating APDU commands between the card and the terminal, an attacker can bypass PIN verification and force the terminal to accept fraudulent transactions. The research highlights critical flaws in the EMV protocol implementation and the lack of cryptographic binding between the card and terminal during the verification process.
Bypassing EMV PIN Verification via APDU Manipulation
TLDR: Researchers have demonstrated that EMV payment terminals are vulnerable to man-in-the-middle attacks that bypass PIN verification entirely. By using hardware like the SimTrace2 to intercept and modify APDU commands, an attacker can force a terminal to accept a fraudulent transaction without a valid PIN. This research exposes a critical failure in the EMV protocol where the terminal fails to cryptographically bind the verification result to the transaction.
Payment security often feels like a black box, shielded by layers of proprietary specifications and the assumption that if a card is EMV-compliant, it is inherently secure. The reality is far more fragile. When you tap your card at a terminal, you are participating in a complex handshake that relies on the terminal and the card agreeing on the rules of the game. If an attacker can sit in the middle of that conversation, they can rewrite the rules in real-time.
The Mechanics of the Downgrade
The EMV protocol relies on a series of Application Protocol Data Unit (APDU) commands to facilitate communication between the card and the terminal. The process typically involves four primary steps: SELECT, Get Processing Options (GPO), READ RECORD, and GENERATE AC. The vulnerability lies in the fact that the terminal often trusts the card to report its own capabilities and the outcome of the verification process.
During a transaction, the terminal asks the card for its supported features. An attacker can intercept this traffic and manipulate the responses. By modifying the APDU responses, the attacker can trick the terminal into believing that the card does not support online PIN verification or that a weaker, easily bypassed verification method is acceptable. This is a classic Identification and Authentication Failure scenario, where the terminal fails to verify the integrity of the authentication process.
Intercepting the Handshake
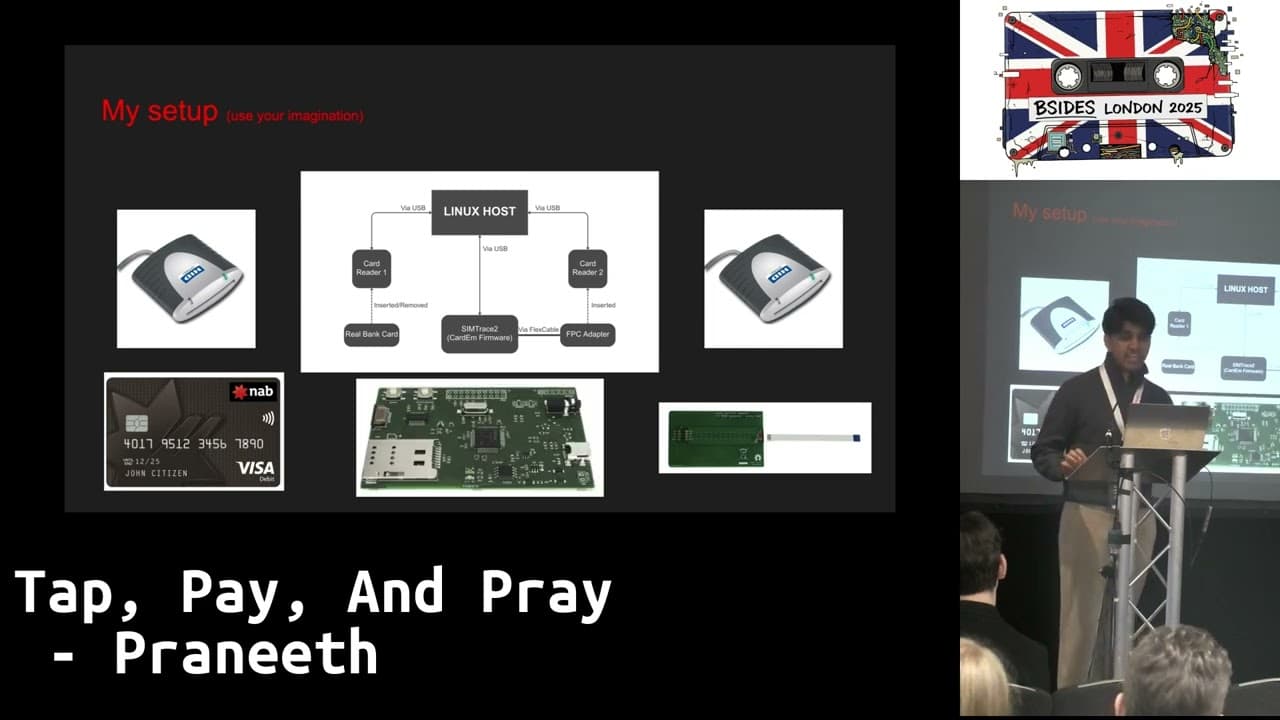
To execute this, you need hardware capable of sniffing and injecting traffic on the ISO/IEC 7816 interface. The SimTrace2 is the standard tool for this, as it allows you to act as a bridge between a real card and a terminal. By flashing the device with custom firmware like CardEmulator, you can emulate a card that responds exactly how you want it to.
The attack flow involves intercepting the VERIFY command. When the terminal sends a request to verify the PIN, the attacker’s script intercepts the failure response and replaces it with a success code.
# Example logic for intercepting and modifying APDU responses
if VERIFY_PRE and command[0:4] == "0020":
# Intercept the failed PIN verification
# Replace the error code with a success status word
return binascii.a2b_hex("9000")
In this setup, the terminal sends a 0020 (VERIFY) command. If the PIN is incorrect, the card would normally return an error. By injecting 9000 (the standard success status word), the terminal proceeds as if the user entered the correct PIN. The terminal never forces the card to prove that a valid PIN check actually occurred, because the protocol lacks a cryptographic binding between the verification result and the transaction data.
Real-World Implications for Pentesters
For a penetration tester, this research changes how you approach physical security assessments. If you are tasked with testing the security of a retail environment, you can no longer assume that the payment terminals are hardened against local manipulation. An engagement should include testing the physical access controls around the terminals. If you can gain access to the card reader interface, you can potentially bypass the entire authentication layer.
The impact is significant. Because the liability for fraudulent transactions is often shifted to the merchant or the customer based on whether a PIN was used, these attacks create a scenario where the system is effectively broken, but the financial institutions have no incentive to fix it. They are playing a game of hot potato with the fraud risk.
Defensive Realities
Defending against this requires more than just software patches. It requires a fundamental change in how terminals and cards communicate. Implementing distance-bounding protocols would help verify the physical proximity of the card, making it much harder to use relay devices. Furthermore, ensuring that all APDU commands are protected by a secure channel would prevent the kind of traffic manipulation described here.
However, the industry is slow to move. The current infrastructure is deeply entrenched, and the cost of replacing millions of terminals to support more secure protocols is prohibitive. For now, the best defense is to monitor for anomalous transaction patterns that suggest a high rate of PIN bypasses or unusual terminal behavior.
If you are a researcher, the next step is to investigate the specific implementations of these protocols in different regions. Not all terminals are created equal, and some may have more robust checks than others. The lack of cryptographic binding is a systemic issue, but the ease of exploitation varies wildly depending on the terminal’s firmware and the specific card scheme. Start by looking at the official EMV specifications and comparing them against how common terminals actually handle the VERIFY command. The gap between the specification and the implementation is where the most interesting bugs are found.
Vulnerability Classes
Tools Used
Target Technologies
Attack Techniques
OWASP Categories
Up Next From This Conference
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Unmasking the Snitch Puck: The Creepy IoT Surveillance Tech in the School Bathroom