Warflying in a Cessna Part II: Upping Our Game
This presentation demonstrates the practical application of warflying to collect wireless access point data from a small aircraft. The speakers analyze the impact of aircraft fuselage and antenna orientation on signal reception performance compared to traditional ground-based wardriving. The talk provides a comparative analysis of different antenna configurations and their effectiveness in capturing Wi-Fi beacon packets from altitude. The research highlights the feasibility of using mobile devices and specialized hardware like the WiFi Coconut for aerial signal reconnaissance.
Aerial Reconnaissance: Why Your Wi-Fi Footprint Is Visible From 1,500 Feet
TLDR: This research demonstrates that standard Wi-Fi beacon frames are easily captured from low-altitude aircraft, effectively turning the sky into a massive wardriving platform. By comparing antenna configurations and signal reception through aircraft fuselages, the presenters proved that mobile devices running Kismet can map urban wireless infrastructure with surprising density. Pentesters should recognize that physical security perimeters for wireless networks are effectively non-existent, as aerial signal collection bypasses traditional ground-level obstacles.
Wireless security often focuses on the immediate vicinity of a building or the reach of a high-gain antenna in a parking lot. We rarely consider that our access points are broadcasting their presence to anything with a line of sight, including small aircraft flying at 1,500 feet. The recent research into "warflying" confirms that the physical barrier of a building or a fence does nothing to stop the systematic mapping of your wireless environment from the air.
The Mechanics of Aerial Signal Collection
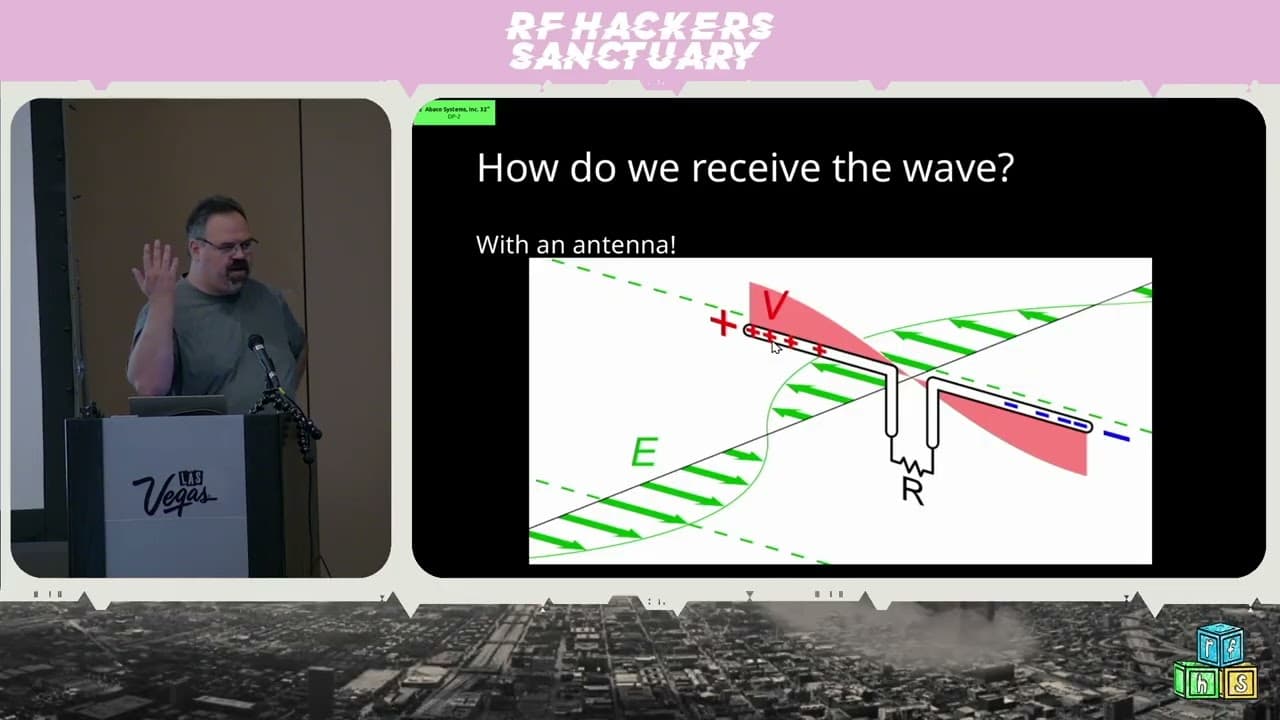
At the core of this research is the realization that Wi-Fi access points are chatty. They broadcast beacon packets roughly every 102.4 milliseconds to announce their presence. If you have a radio tuned to the correct channel, you can capture these packets. The challenge at altitude is not just signal strength, but the physics of the aircraft itself.
The researchers utilized a Cessna 172, a common four-seat aircraft with an aluminum fuselage. Aluminum is an excellent RF shield. When they mounted antennas inside the cabin, they found that the fuselage significantly attenuated signals coming from the opposite side of the plane. This is a critical takeaway for anyone attempting similar reconnaissance: antenna placement is not just about gain; it is about managing the massive RF shadow cast by the aircraft structure.
To overcome this, they experimented with different setups, including a WiFi Coconut, a specialized device featuring 14 individual Wi-Fi radios. By dedicating a radio to each channel in the 2.4 GHz band, they eliminated the latency inherent in channel-hopping, allowing for a much higher density of data collection.
Technical Nuances in Data Capture
When you are moving at 176 feet per second, your window for capturing a specific beacon frame is narrow. The researchers found that while traditional wardriving (driving a car) captures more total access points due to proximity, warflying captures them faster and over a much wider geographic area.
The data collection workflow relied on Kismet for packet processing and WiGLE for mapping. The following command structure represents the typical approach for initializing a capture session on a Linux-based system, assuming the interface is in monitor mode:
# Set interface to monitor mode
sudo airmon-ng start wlan0
# Run Kismet to capture and log packets
kismet -c wlan0mon
The researchers highlighted that the "vibe coding" of their data—using Python scripts to parse the resulting CSV files—allowed them to visualize signal density. By categorizing detections based on the number of times a specific MAC address was seen, they could filter out transient signals and focus on permanent infrastructure. This is the same logic used in OWASP's guidance on wireless security, which emphasizes that identifying the presence of a network is the first step in any targeted attack.
Real-World Implications for Pentesters
If you are conducting a physical security assessment, you need to account for the fact that your client's wireless footprint is not limited to the ground floor. An attacker with a modest budget and a flight plan can map the entire wireless topology of a corporate campus in minutes.
During an engagement, this means that "hidden" SSIDs or networks that are supposedly isolated from the public-facing side of a building are still visible from above. If you are testing a facility, assume that any wireless signal is discoverable. The impact of this is significant: it allows an attacker to perform reconnaissance on the target's hardware vendors, security configurations, and geographic distribution of access points without ever setting foot on the property.
Defensive Realities
Defending against aerial reconnaissance is difficult because you cannot easily hide an RF signal. However, you can minimize the utility of the data collected. Ensure that your access points are not broadcasting unnecessary information in their beacon frames. Disable legacy protocols and ensure that your wireless infrastructure is segmented. If you are in a high-security environment, consider the use of directional antennas that point toward the ground rather than omnidirectional antennas that radiate energy toward the sky.
The most important takeaway is that the "air gap" is a myth when it comes to wireless signals. If your access point is powered on, it is broadcasting. Whether that broadcast is being picked up by a car in the parking lot or a plane overhead is merely a matter of the attacker's perspective. Stop assuming your wireless network is invisible just because it is behind a locked door. Start assuming that every packet you broadcast is public record, and design your security architecture accordingly.
Tools Used
Target Technologies
Attack Techniques
Up Next From This Conference
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web