Where Did The Organiser Go? When The Conference Doesn't Run As Planned
This talk is a non-technical, anecdotal presentation regarding the logistical and operational challenges of running security conferences. It discusses common failure points such as venue issues, power failures, and speaker scheduling conflicts that can disrupt event flow. The content is intended for conference organizers and community members rather than penetration testers or security researchers. It contains no technical vulnerability research, exploit demonstrations, or security tools.
The Hidden Infrastructure Risks of Security Conferences
TLDR: Security conferences are high-stakes environments where physical and digital infrastructure often fail under pressure. This post breaks down the operational vulnerabilities that lead to conference-wide outages, from power grid instability to misconfigured access control systems. Understanding these failure modes helps researchers anticipate and mitigate risks when deploying sensitive hardware or research demos in live, high-traffic environments.
Security researchers often treat conference venues as black boxes, assuming the network and power will just work. We focus on the payload, the exploit, and the bypass, ignoring the fragile physical layer that supports our work. When you are presenting a live demo at a major event, you are at the mercy of the venue’s infrastructure. If the power drops or the network segments, your research doesn't just fail; it becomes a liability.
The Fragility of Venue Infrastructure
Conferences are not standard office environments. They are temporary, high-density deployments that push venue utilities to their absolute limits. The most common point of failure is the power distribution system. Most venues are not designed to handle the massive, fluctuating load of hundreds of laptops, high-end workstations, and specialized hardware running simultaneously.
When a venue’s power grid is pushed beyond its rated capacity, voltage drops and surges become inevitable. For a researcher, this is a nightmare. If your hardware is not properly isolated, a simple power fluctuation can fry your gear or, worse, trigger a hard reset during a critical demo. I have seen high-end FPGA boards and custom-built servers bricked because a venue’s power distribution unit (PDU) couldn't handle the load of a nearby vendor booth.
Always assume the power is dirty. If you are bringing hardware, use a high-quality Uninterruptible Power Supply (UPS) or at least a power conditioner. Do not rely on the venue’s provided power strips. They are often daisy-chained in ways that violate basic electrical safety standards and create significant fire hazards.
Network Segmentation and Access Control Failures
Network infrastructure at conferences is equally volatile. We often see flat networks where every device is reachable, or overly aggressive segmentation that breaks legitimate traffic. The real risk, however, is in the physical access control systems that secure these spaces.
Many venues use automated building management systems to control door locks and HVAC. These systems are frequently misconfigured. I have seen scenarios where a building’s automated security policy triggers a full lockdown at a specific time, regardless of whether a session is still in progress. This creates a physical security risk where attendees are trapped in a room or, conversely, where unauthorized access is granted because the system failed to transition to a secure state.
When testing in these environments, look for the OWASP Top 10 vulnerabilities in the management interfaces of these building systems. They are often running outdated firmware with hardcoded credentials or unauthenticated APIs. If you are presenting, verify the physical security of your demo area. If the door locks are controlled by a central system, ask the organizers how they handle emergency overrides.
The Human Element in Operational Security
Operational security is not just about the tech; it is about the people running the show. Conference organizers are often overwhelmed, and communication breakdowns are the norm. When a failure occurs, the response is usually chaotic.
The most effective way to protect your research is to build redundancy into your setup. If you are running a demo, have a local, offline version of your exploit or presentation. Do not rely on cloud-based services or external APIs that require a stable internet connection. If your demo requires a specific network configuration, bring your own router and create a private, isolated network.
Furthermore, be aware of the physical security of your equipment. In a crowded conference hall, it is trivial for someone to walk off with a piece of hardware. Use Kensington locks to secure your devices to the table. If you are leaving your gear unattended, ensure it is encrypted at rest. A stolen laptop is a data breach waiting to happen, and the physical security of the venue is rarely as robust as you might think.
Lessons for the Field
The next time you are preparing for a talk or a red team engagement at a conference, treat the venue as a hostile environment. Map out the power sources, identify the network boundaries, and have a contingency plan for when things go sideways.
If you are interested in the history of conference failures and the lessons learned from them, check out the archives at Administrator.video. It is a goldmine of past talks that highlight the operational realities of our community.
Security is not just about finding the bug; it is about ensuring your work survives the environment in which it is presented. Don't let a faulty power strip or a misconfigured door lock be the reason your research fails. Build for failure, expect the unexpected, and always have a backup plan. The infrastructure is the foundation of everything we do, and it is almost always more fragile than it looks.
Up Next From This Conference

Opening Remarks

A Technical Evaluation Of Real-World Passkey Security

Digital ID: A Success Story Or Dystopian Nightmare?
Similar Talks

Carding, Sabotage, and Survival: A Darknet Market Veteran Story
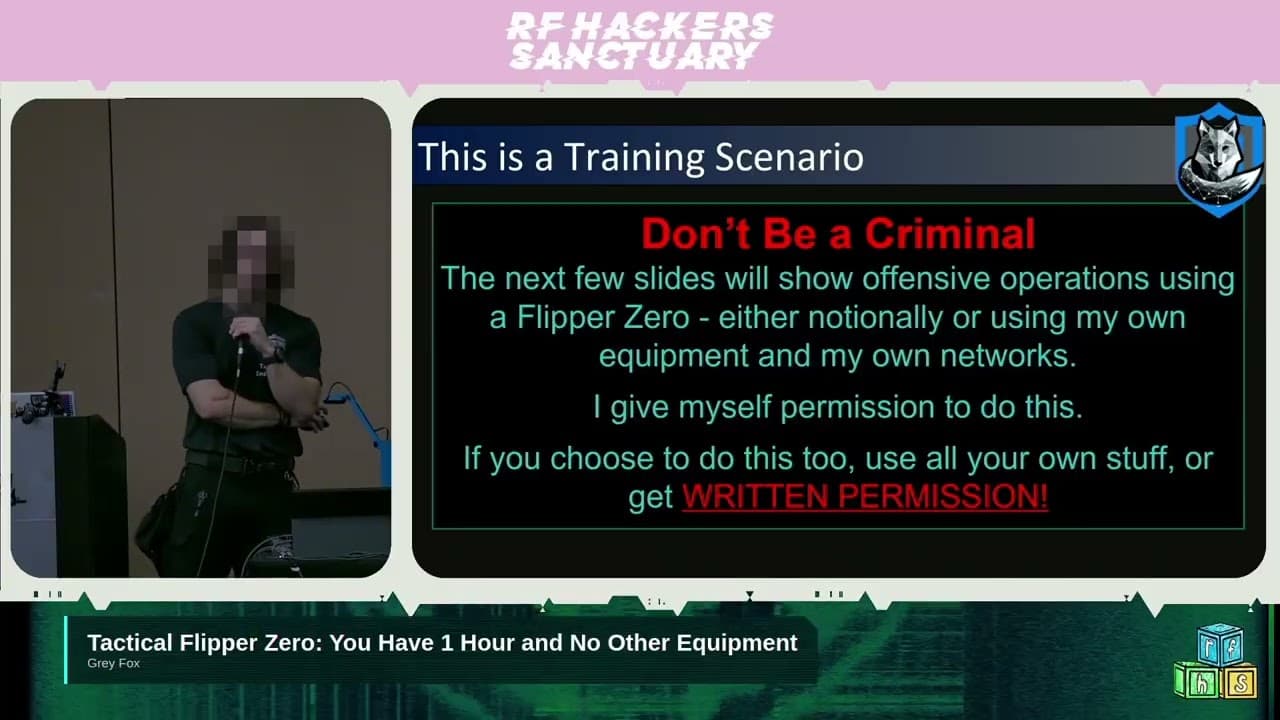
Tactical Flipper Zero

