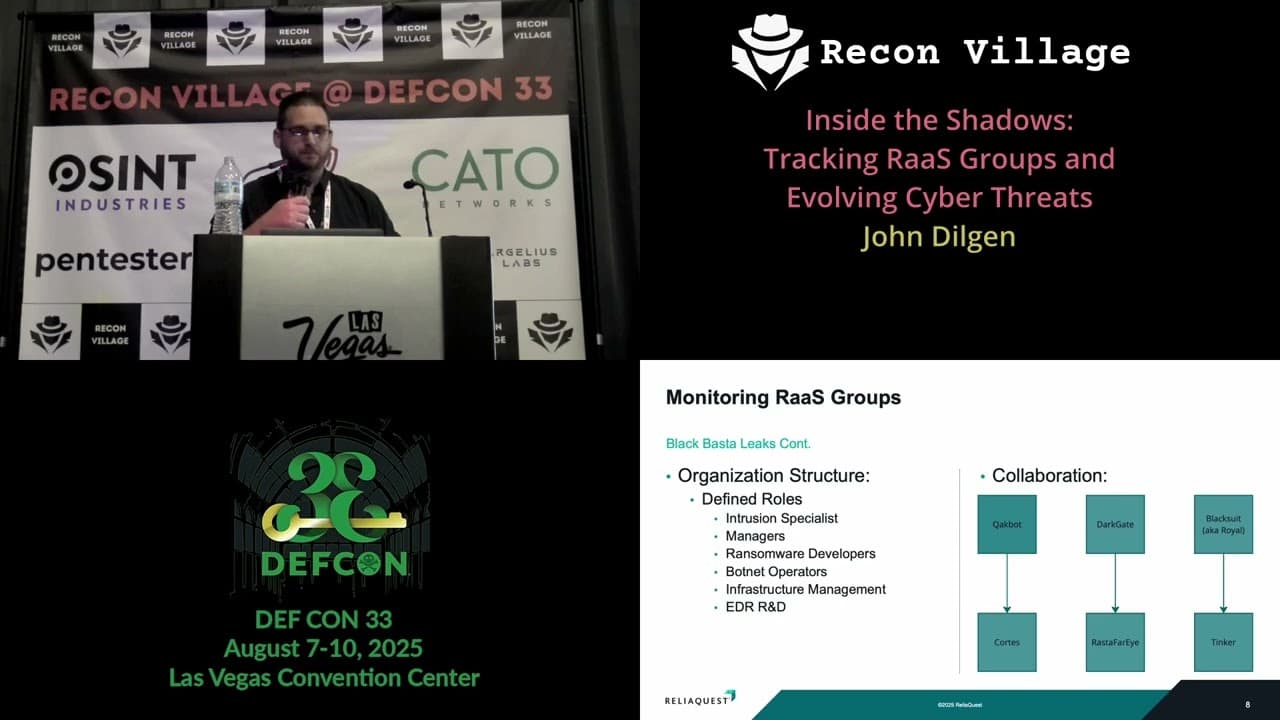
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
This talk analyzes the operational structure, recruitment tactics, and evolving attack methodologies of Ransomware-as-a-Service (RaaS) groups like Black Basta, LockBit, and DragonForce. It details how these threat actors leverage initial access brokers, email spam bombs, and social engineering to compromise organizations and deploy ransomware. The presentation provides actionable intelligence for blue teams to detect and mitigate these threats by monitoring specific indicators of compromise and implementing robust helpdesk verification procedures. It also highlights the use of automated workflows and the shifting landscape of RaaS collaboration.
How RaaS Groups Are Weaponizing Helpdesk Social Engineering
TLDR: Ransomware-as-a-Service (RaaS) groups like Black Basta and DragonForce are increasingly bypassing traditional perimeter defenses by weaponizing helpdesk social engineering. By impersonating employees and exploiting weak identity verification, these actors gain initial access and escalate privileges through automated workflows. Pentesters should prioritize testing helpdesk verification procedures and monitoring for anomalous Microsoft Teams activity to identify these high-impact entry points.
Modern ransomware operations have shifted from brute-forcing RDP to sophisticated social engineering campaigns that target the human element of IT support. Threat actors no longer need to burn zero-day exploits when they can simply call a helpdesk, pose as a frantic employee, and convince a technician to reset MFA credentials. This technique, often referred to as vishing, has become a cornerstone of the initial access phase for groups like Black Basta and DragonForce.
The Mechanics of Helpdesk Impersonation
The attack flow observed in recent engagements is remarkably consistent. An attacker identifies a target, often a high-value user like a CFO or a system administrator, using open-source intelligence tools like ZoomInfo or Intelligence X. Once they have enough context, they initiate a call to the organization's helpdesk. The goal is to trigger a password or MFA reset.
If the helpdesk technician fails to follow strict verification protocols, the attacker gains control of a legitimate account. From there, the attacker uses tools like Rclone for data exfiltration or WinSCP to move files across the network. The reliance on legitimate, dual-use tools makes detection difficult, as these binaries are often already present or whitelisted in many enterprise environments.
Technical Indicators and Automated Workflows
Threat actors are not just using manual techniques; they are building automated workflows to scale their operations. We have observed attackers using Microsoft Teams as a primary communication channel for these attacks. By creating accounts with display names like "IT Support" or "Helpdesk," they can initiate chats with unsuspecting employees to deliver malicious payloads.
A common payload delivery involves dropping files that appear to be legitimate updates or configuration scripts. For example, an attacker might send a file named it_update.vbs or AntispamAccount.exe. These files are designed to establish persistence or facilitate further lateral movement. Defenders should monitor for the following indicators in their environment:
# Example detection logic for suspicious file execution
Get-WinEvent -FilterHashTable @{LogName='Microsoft-Windows-Sysmon/Operational'; Id=1} |
Where-Object {$_.Message -match "it_update.vbs|AntispamAccount.exe|AntispamUpdate.exe"}
The use of Shodan to identify exposed services and Intelligence X to correlate leaked credentials allows these groups to tailor their social engineering pitches with alarming accuracy. When a helpdesk technician receives a call from someone who knows the target's recent project history, their internal phone extension, and their manager's name, the likelihood of a successful compromise increases exponentially.
Pentesting the Human Perimeter
During a red team engagement, testing the helpdesk is often the most effective way to demonstrate the fragility of an organization's identity management. If you are tasked with a penetration test, do not limit your scope to technical vulnerabilities. Request permission to perform social engineering against the helpdesk. You will likely find that the "human firewall" is the weakest link in the chain.
When testing, document every step of the verification process. Did the technician ask for a secondary form of ID? Did they send a verification code to a pre-registered device? If they simply reset the password because you sounded convincing, you have found a critical vulnerability that no amount of endpoint protection can fix. This is a classic example of OWASP A07:2021 – Identification and Authentication Failures, where the failure is not in the code, but in the process.
Defensive Hardening
Defending against these attacks requires a shift in how IT support operates. First, implement mandatory, out-of-band verification for all helpdesk requests. If a user calls to reset their password, the helpdesk must call them back on a verified number stored in the HR system. Second, audit all Remote Monitoring and Management (RMM) tools. Attackers love these tools because they provide a legitimate, persistent backdoor into the network. If a tool is not explicitly authorized and managed by the security team, it should be disabled via Group Policy or application control.
Finally, educate your users. They need to know that IT will never ask for their MFA token over the phone or via a chat message. The most effective defense is a culture where employees are empowered to challenge suspicious requests, even if they appear to come from internal support staff.
The evolution of RaaS groups shows that they are constantly refining their tactics to exploit the path of least resistance. By focusing on the intersection of identity management and social engineering, these groups have turned the helpdesk into a high-value target. As researchers and testers, we must continue to expose these gaps and push for more rigorous verification standards. The next time you are on an engagement, look beyond the network perimeter and see if you can walk through the front door by simply picking up the phone.
Vulnerability Classes
Target Technologies
Attack Techniques
OWASP Categories
All Tags
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web

