Mapping the Shadow War: From Estonia to Ukraine
This research presentation analyzes the evolution of Russian state-sponsored cyber operations and their integration with kinetic military actions from 2007 to the present. It details technical methodologies including BGP hijacking for traffic interception, the deployment of data-wiping malware, and the strategic use of the SORM surveillance platform. A key highlight is the demonstration of how satellite communication terminals like Starlink were compromised using malware-laden Android devices planted for discovery by opposing forces.
BGP Hijacking and Satellite Compromise: Lessons from the Shadow War
TLDR: Recent research into state-sponsored cyber operations reveals a sophisticated integration of BGP hijacking and physical supply chain attacks against satellite communication terminals. By compromising Android devices to plant malware, attackers gained control over critical infrastructure, including Starlink and Viasat terminals. Security professionals must treat satellite-based internet as a high-risk transport layer and implement strict endpoint hardening to mitigate these persistent threats.
Modern offensive security often focuses on web application vulnerabilities or cloud misconfigurations, but the most effective state-sponsored campaigns operate at the infrastructure layer. The recent analysis of Russian cyber operations from Estonia to Ukraine highlights a shift from simple DDoS attacks to complex, multi-stage campaigns that bridge the gap between digital and kinetic warfare. For a researcher or pentester, the takeaway is clear: the network is only as secure as the routing protocols and hardware endpoints that support it.
The Mechanics of BGP Hijacking for Interception
BGP hijacking is frequently dismissed as a theoretical risk or a configuration error, but in the context of state-sponsored operations, it is a deliberate tool for traffic interception. By announcing unauthorized routes, attackers force traffic through infrastructure under their control. Once the traffic is rerouted, the goal is not just disruption, but total visibility.
In the Russian operations described, BGP hijacking was used to route traffic through domestic ISPs. This is critical because of the legal framework in Russia, specifically the Yarovaya Law, which mandates that ISPs retain metadata and communication content for six months. Furthermore, the SORM (System for Operative Investigative Activities) platform allows intelligence agencies to intercept this traffic without a court order.
For a pentester, this means that if your traffic traverses a compromised BGP path, you must assume that all unencrypted data is being logged. Even with TLS, the metadata—source, destination, and timing—is exposed. When testing systems that rely on satellite or cross-border transit, always assume the transport layer is hostile.
Supply Chain Attacks on Satellite Terminals
Perhaps the most alarming finding is the method used to compromise satellite terminals like Starlink and Viasat. Rather than attacking the satellite link directly, which is computationally expensive and technically difficult, the attackers targeted the physical supply chain.
The technique involved planting malware-laden Android devices in areas where they would be discovered by opposing forces. Once a soldier or operator picked up the device and connected it to their local network or used it to manage a satellite terminal, the malware executed. This is a classic supply chain attack that bypasses perimeter defenses entirely.
Once the Android device was compromised, the malware moved laterally to the satellite terminal. By gaining control of the terminal, the attackers could effectively jam communications or reroute traffic, rendering the satellite link useless. This demonstrates that even the most secure satellite encryption is irrelevant if the management interface or the connected endpoint is compromised.
Why This Matters for Your Next Engagement
If you are performing a red team engagement or a security assessment, you need to look beyond the application layer. When testing remote sites or field-deployed hardware, consider the following:
- Endpoint Trust: Never assume that a device found in the field is clean. If your client uses satellite terminals for remote connectivity, audit the management interfaces and the devices that have access to them.
- Routing Integrity: Use tools like BGPStream to monitor for suspicious route announcements that might indicate your traffic is being intercepted.
- Biometric and Identity Data: The talk highlighted that biometric data is a high-value target because it cannot be rotated like a password. If your client stores biometric data, ensure it is encrypted at rest and that the hardware capturing it is physically secured.
The evolution of these techniques shows that attackers are learning from every operation. They are moving from simple web defacements to sophisticated, persistent threats that leverage the very infrastructure we rely on for secure communication. As researchers, we need to stop viewing these as isolated incidents and start treating them as a blueprint for how modern, state-level adversaries operate.
The next time you are auditing a network, ask yourself: if the ISP routing this traffic were malicious, what could they see? If the hardware managing this connection were compromised, what could they do? The answers to those questions are where the real vulnerabilities lie. Keep your focus on the infrastructure, because that is where the shadow war is being fought.
Vulnerability Classes
Tools Used
Target Technologies
Attack Techniques
All Tags
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
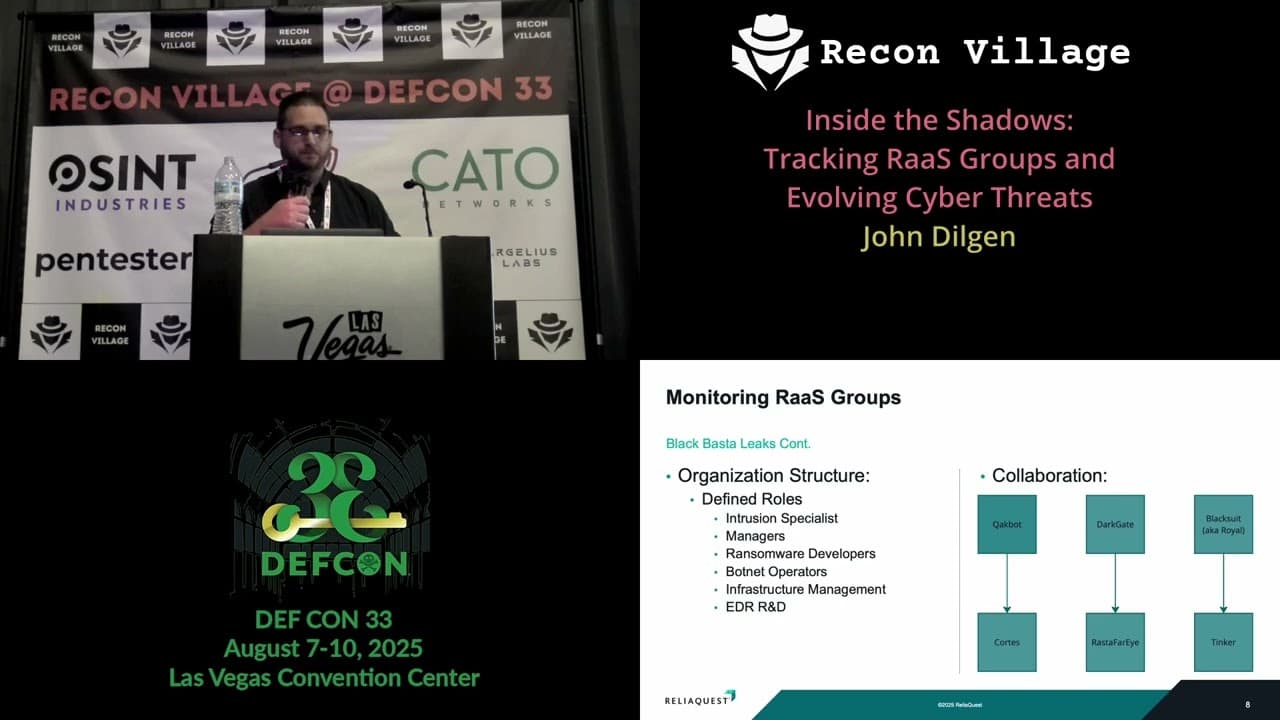
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web

