So What the Heck Is This Radio Stuff Anyway?
This talk provides a foundational overview of radio frequency (RF) concepts, including the electromagnetic spectrum, frequency allocation, and signal propagation. It explains the mechanics of antennas, feedlines, and filters, and how they are used to transmit and receive data. The presentation also covers the basics of modulation techniques like AM, FM, and digital modulation, as well as the principles of software-defined radio (SDR) and the Nyquist sampling theorem. The session serves as an introductory guide for security researchers interested in hardware hacking and RF analysis.
Stop Treating Radio Frequency Like Magic: A Practical Guide for Pentesters
TLDR: Radio frequency analysis is often treated as a black box, but it is just another layer of the OSI model that you can probe and exploit. This guide breaks down the fundamentals of RF signals, antenna theory, and software-defined radio (SDR) to help you move beyond basic packet sniffing. Understanding how to manipulate the physical layer is essential for any researcher looking to bridge the gap between digital exploits and hardware-level control.
Most security researchers treat the physical layer as someone else's problem. We spend our days hunting for logic flaws in APIs or memory corruption in binaries, but we rarely stop to consider that the data we are analyzing often travels through the air as a series of electromagnetic oscillations. If you are testing IoT devices, industrial control systems, or even modern automotive keyless entry, you are already working in the RF domain. Ignoring the radio side of the equation is like trying to debug a web application while ignoring the HTTP headers.
The Physics of the Air Gap
Radio frequency is simply a portion of the electromagnetic spectrum, measured in cycles per second, or Hertz. When you transmit data, you are essentially wiggling electrons in an antenna at a specific frequency. That oscillation creates an electromagnetic wave that propagates through space.
For a pentester, the most important takeaway is that these waves are non-ionizing. They do not alter DNA or cause the kind of biological damage that high-energy radiation does. They only do one thing: they heat things up. If you are worried about 5G signals causing health issues, you are ignoring the basic physics of non-ionizing radiation. Your focus should be on the signal itself, not the phantom health risks.
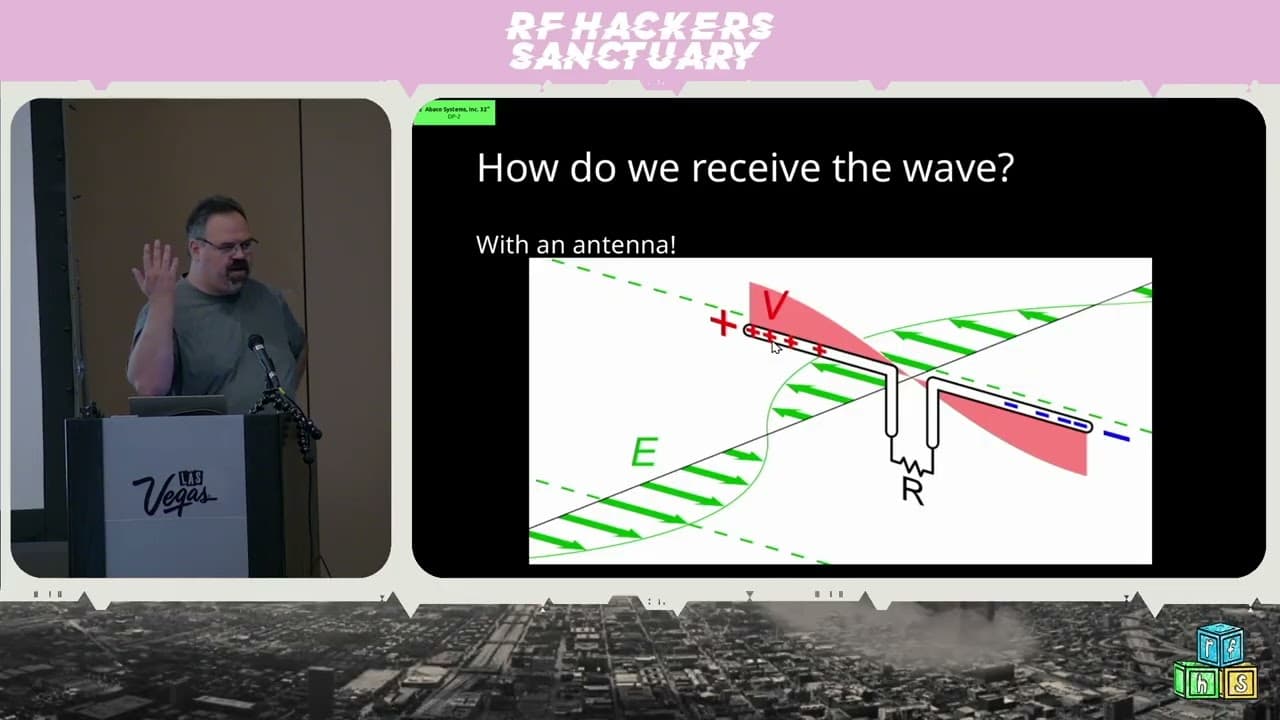
Understanding Antennas and Feedlines
Antennas are not just metal sticks; they are resonant circuits designed to capture or radiate energy at specific frequencies. A dipole antenna, for instance, is tuned to a specific length based on the wavelength of the signal you want to capture. If your antenna is the wrong length, you are essentially trying to listen to a conversation through a wall with a stethoscope that is not pressed against the surface.
When you connect your antenna to your radio, you use a feedline. Coaxial cable is the standard here, consisting of a center conductor and an outer shield. The signal travels along the center conductor, while the shield provides a return path and protects the signal from external interference. If you are seeing massive signal loss or unexpected noise during your captures, check your connectors and cable quality. A cheap, poorly shielded cable is a common point of failure that can ruin an entire engagement.
Software-Defined Radio: The Digital Bridge
Software-defined radio (SDR) is the tool that makes RF hacking accessible. Instead of building custom hardware for every frequency, an SDR digitizes the RF spectrum as close to the antenna as possible. It takes the analog signal, passes it through an analog-to-digital converter (ADC), and hands the raw data to a digital signal processor (DSP) for analysis.
The Nyquist-Shannon sampling theorem is the golden rule here. You must sample your signal at a rate at least twice the frequency of the highest component you want to capture. If you fail to do this, you encounter aliasing, where high-frequency signals fold back into your lower-frequency capture, creating ghost signals that do not exist. If you are using a tool like GNU Radio to process your captures, understanding your sample rate is the difference between a clean signal and a mess of noise.
Modulation and Data Encoding
Modulation is the process of encoding your digital data onto an analog carrier wave. Whether it is Amplitude Modulation (AM), Frequency Modulation (FM), or more complex schemes like Quadrature Amplitude Modulation (QAM), the goal is the same: to represent bits as changes in the carrier wave.
In QAM, for example, you are manipulating both the amplitude and the phase of the signal. By plotting these values on an X-Y graph, you create a constellation diagram. Each point in that constellation represents a specific bit pattern. The more points you pack into that diagram, the more data you can send, but the more susceptible your signal becomes to noise. If you are analyzing a proprietary protocol, look for these patterns in your IQ data. If you see a clear constellation, you have already won half the battle.
Where to Start Your Research
If you want to get serious about RF, you need to get your hands dirty. Start by getting your Amateur Radio license. It is not just about talking to people on the radio; it is about learning the regulations and the physics that govern the spectrum. For hardware, look into the HackRF One or similar SDR platforms. These tools allow you to transmit and receive across a wide range of frequencies, giving you the ability to test how devices respond to different signal inputs.
Stop assuming the air is a secure medium. Every time you see a wireless protocol, ask yourself how it handles signal integrity and authentication. If you can capture the signal, you can often replay it, modify it, or use it to trigger unintended behavior in the target device. The next time you are on an engagement, look at the antennas on the roof or the wireless modules on the PCB. That is where the real fun begins.
Target Technologies
All Tags
Up Next From This Conference
Similar Talks

Unmasking the Snitch Puck: The Creepy IoT Surveillance Tech in the School Bathroom

Anyone Can Hack IoT: A Beginner's Guide to Hacking Your First IoT Device