Tactical Flipper Zero
This talk demonstrates the use of a Flipper Zero for passive and active reconnaissance, signal analysis, and signal replay in a simulated tactical environment. The speaker covers techniques for identifying and tracking high-value individuals (HVI) using Wi-Fi probe requests, NFC card cloning, and sub-GHz key fob signal capture. The presentation emphasizes the importance of operational security and the use of these tools for intelligence gathering rather than direct exploitation. The speaker also provides practical guidance on using stock firmware and external modules to extend the device's capabilities.
Tactical Reconnaissance and Signal Replay with the Flipper Zero
TLDR: This research demonstrates how to use a Flipper Zero for low-cost, high-impact signal reconnaissance and replay in tactical environments. By leveraging Wi-Fi probe requests, NFC cloning, and sub-GHz signal analysis, researchers can build a detailed profile of high-value targets without needing expensive SDR equipment. This approach highlights the critical need for better physical and wireless security controls in environments where signal leakage is often ignored.
Wireless security is often treated as a software problem, but the hardware layer is where the real leakage happens. Most organizations focus on hardening their cloud infrastructure or patching web vulnerabilities while leaving their physical premises wide open to anyone with a sub-GHz radio. The recent demonstration of tactical reconnaissance using a Flipper Zero proves that you do not need a multi-thousand-dollar software-defined radio setup to map out a target's movements or clone their access credentials.
Passive and Active Reconnaissance
The core of this research centers on the transition from passive to active signal collection. In a tactical scenario, you start by listening. Wi-Fi-enabled devices are constantly broadcasting probe requests, effectively shouting their history of connected networks to anyone within range. By using a Wi-Fi Devboard running Marauder firmware, you can capture these probes.
When a device is not actively connected to an access point, it continues to beacon for known networks. This behavior creates a unique fingerprint. If you collect these beacons, you can cross-reference them against databases like WiGLE to determine where that device has been. This is not just theoretical; it is a direct path to building a pattern-of-life profile for a target. If you see a device beaconing for a specific corporate SSID, you have confirmed the target's presence and their likely affiliation.
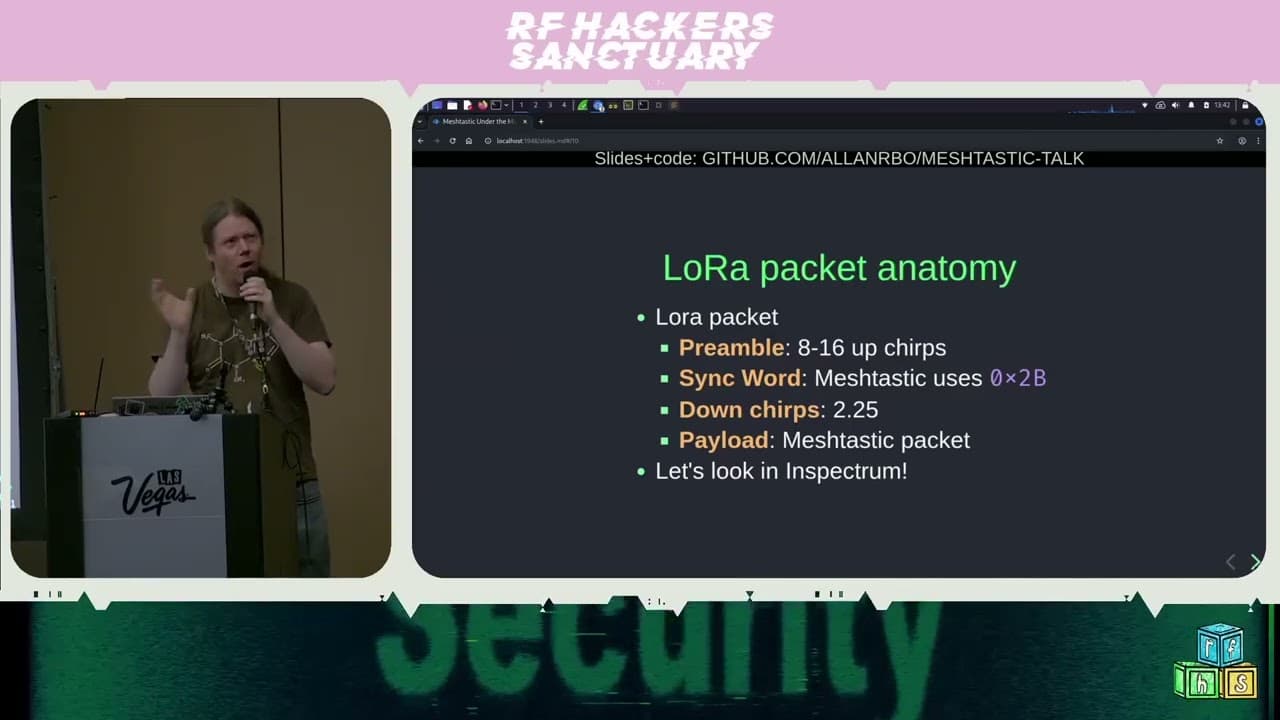
Signal Analysis and Replay
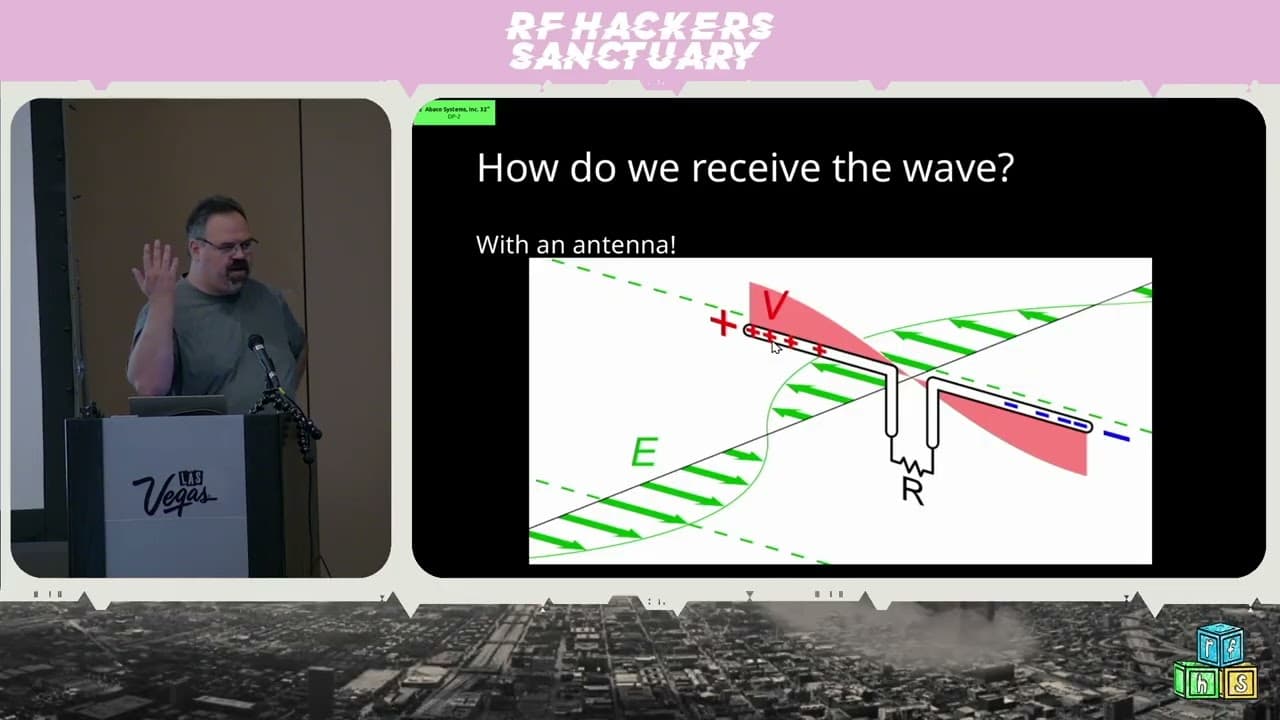
Once you have identified a target, the next step is often credential or access acquisition. The Flipper Zero excels at capturing sub-GHz signals, which are the backbone of most legacy key fobs and garage door openers. The research highlights a critical distinction: you are not always trying to break encryption. Sometimes, you are simply identifying the signal frequency and replaying it.
To find the correct frequency, you need a spectrum analyzer. While the stock Flipper firmware is limited, you can easily load custom applications to visualize the RF environment. When you trigger a key fob, you look for the spike in the spectrum. Once the frequency is isolated, you use the "Read RAW" function to capture the signal.
# Example workflow for sub-GHz capture
1. Navigate to Sub-GHz > Spectrum Analyzer
2. Identify the frequency spike (e.g., 315 MHz or 433.92 MHz)
3. Switch to Sub-GHz > Read RAW
4. Capture the signal and save to the SD card
The power here lies in the simplicity. You do not need to understand the underlying rolling code algorithm to identify the vehicle or the room associated with a specific fob. By replaying the signal, you can trigger the vehicle's lights or horn, confirming that you have successfully mapped the fob to the target. This is a non-destructive way to verify your intelligence before moving to more intrusive steps.
NFC Cloning and Access Control
Physical access is often the final hurdle. Many hotels and secure facilities still rely on MIFARE Classic cards for room access. These cards are notoriously insecure because they use proprietary, weak encryption that has been cracked for years.
The Flipper Zero can read these cards and, if you have the correct keys, decrypt the sectors. If you are on an engagement and find a card left unattended, you can clone it in seconds. The key to success here is having a dictionary of common keys. Once you have the dump, you can emulate the card to open the door. This is a classic example of A07:2021 – Identification and Authentication Failures manifesting in the physical world.
Defensive Realities
Defending against these techniques requires a shift in how we view physical security. If your facility uses legacy RFID cards, you are already compromised. The only real fix is to migrate to modern, encrypted smart cards that support mutual authentication and are resistant to cloning.
For wireless security, the risk is harder to mitigate. Devices will always beacon for known networks unless users are trained to disable auto-join features or use privacy-focused configurations. Defenders should implement network segmentation and ensure that sensitive areas are shielded from external RF signals. If you are a security lead, assume that your perimeter is porous. If a researcher can sit in your lobby and map your employees' devices, a malicious actor can do the same.
Moving Forward
The Flipper Zero is a force multiplier for intelligence gathering. It forces us to acknowledge that the gap between digital and physical security is non-existent. As you move into your next engagement, look at the hardware around you. Are the key fobs using rolling codes? Are the access cards encrypted? If the answer is no, you have a clear path for your next assessment. The tools are cheap, the techniques are well-documented, and the impact is immediate. Stop ignoring the hardware layer and start testing it.
Vulnerability Classes
Tools Used
Target Technologies
Attack Techniques
OWASP Categories
All Tags
Up Next From This Conference
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web