Showing 25 results

42:25
Science & Technologyresearch-presentationhybridattack-surface

22:01
DEF CON 33 Recon Village - A Playbook for Integration Servers - Ryan Bonner, Guðmundur Karlsson
DEFCONConference
2 months ago
Science & Technologyresearch-presentationhybridwebmethods

20:47
DEF CON 33 Recon Village - Mapping the Shadow War From Estonia to Ukraine - Evgueni Erchov
DEFCONConference
2 months ago
Science & Technologyresearch-presentationhybridrussia
32:30
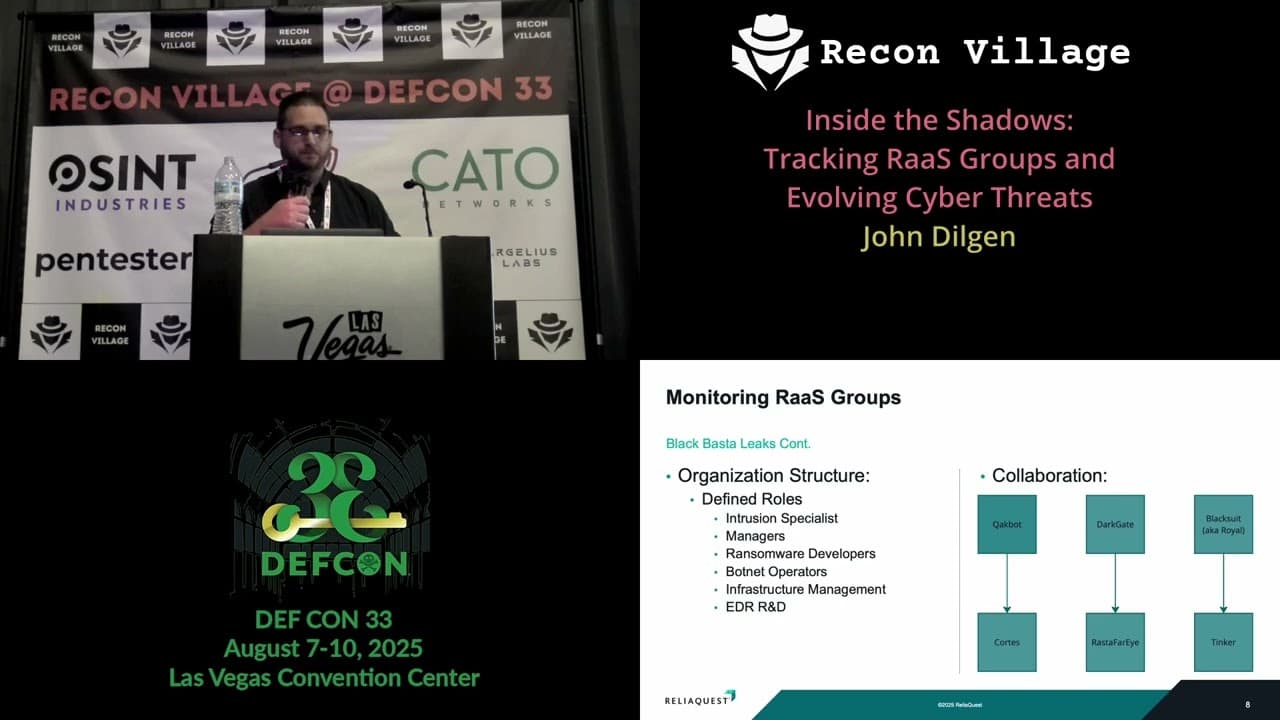
DEF CON 33 Recon Village - Inside the Shadows Tracking RaaS Groups, Cyber Threats - John Dilgen
DEFCONConference
2 months ago
Science & Technologyresearch-presentationhybridransomware-as-a-service

20:12
DEF CON 33 Recon Village - Robin The Archaeologist of the Dark Web - Apurv Singh Gautam
DEFCONConference
2 months ago
Science & Technologyresearch-presentationhybriddark-web

39:53
DEF CON 33 Recon Village - OSINT & Modern Recon Uncover Global VPN Infrastructure - Vladimir Tokarev
DEFCONConference
2 months ago
Science & Technologyresearch-presentationtechnical-deep-divewindows

1:01:42
Travel & Eventsresearch-presentationhybridransomware

47:04
Travel & Eventsresearch-presentationtechnical-deep-divebgp

32:46
The Drone Supply Chain's Grand Siege: From Initial Breaches to Long-Term Espionage
Black Hat
5 months ago
Travel & Eventsresearch-presentationhybridearth-ammit

37:19
Travel & Eventsresearch-presentationhybridandroid

39:12
Travel & Eventsresearch-presentationhybridwechat

22:15
One Bug to Rule Them All: Stably Exploiting a Preauth RCE Vulnerability on Windows Server 2025
Black Hat
5 months ago
Travel & Eventsresearch-presentationtechnical-deep-divewindows-server-2025

45:07
Remote Exploitation of Nissan Leaf: Controlling Critical Body Elements from the Internet
Black Hat
5 months ago
Travel & Eventsresearch-presentationtechnical-deep-diveautomotive

24:13
Travel & Eventsresearch-presentationhybridblack-hat
