Analyzing Foreign Tech from Online Retailers
This talk demonstrates an OSINT-based methodology for investigating the supply chain and security posture of low-cost, foreign-manufactured smart devices purchased from online retailers. The speaker performs a hardware teardown and software analysis of a smart watch to identify data collection practices and potential privacy risks. The presentation highlights the lack of encryption in data transmission and the prevalence of white-labeled hardware across multiple brands. The analysis emphasizes the importance of supply chain security and due diligence when integrating third-party IoT devices into secure environments.
The Hidden Risks of White-Labeled IoT: A Deep Dive into Cheap Smartwatch Security
TLDR: This research exposes the alarming lack of security in low-cost, white-labeled smartwatches sold on major online retailers. By performing a hardware teardown and software analysis, the researcher demonstrates how these devices transmit sensitive user data in clear text to foreign infrastructure. Pentesters and security researchers should treat these devices as untrusted endpoints and prioritize network-level isolation when testing environments where they are present.
Security researchers often focus on high-profile enterprise targets, but the most pervasive threats to user privacy are currently sitting on wrists across the globe. The recent research presented at DEF CON 33 on foreign-manufactured smartwatches highlights a critical blind spot in our collective understanding of the Internet of Things (IoT) supply chain. When you purchase a thirty-dollar smartwatch from an online marketplace, you are not just buying a piece of hardware. You are effectively installing a persistent, unauthenticated data-collection node into your personal network.
The Anatomy of a Supply Chain Failure
The core issue identified in this research is the prevalence of white-labeled hardware. A single manufacturer in China produces a base device, which is then rebranded by hundreds of different companies. These companies often have no actual engineering or security oversight. They simply slap a new logo on the box, create a generic mobile application, and push the product to market.
During the teardown, the researcher identified a Realtek chipset as the primary controller. While the hardware itself is standard, the implementation is where the security falls apart. The device communicates with a mobile application via Bluetooth, which then acts as a bridge to the internet. The research confirmed that the application transmits data—including health metrics, sleep patterns, and potentially sensitive user identifiers—in clear text. This is a classic violation of OWASP Mobile Application Security Verification Standard (MASVS) regarding data storage and transmission.
Technical Analysis: From Teardown to Traffic
To analyze the software, the researcher utilized MobSF (Mobile Security Framework), an essential tool for any researcher performing static and dynamic analysis on mobile applications. By extracting the APK, the researcher was able to map the application's permissions and identify the hardcoded endpoints where data was being exfiltrated.
The attack flow is straightforward:
- Reconnaissance: Identify the device's FCC ID to pull public documentation from the FCC Equipment Authorization Search. This often reveals the true manufacturer and the internal circuit board layout.
- Static Analysis: Use APKTool to decompile the application. Look for hardcoded API keys, clear-text communication protocols, and excessive permission requests.
- Dynamic Analysis: Use a proxy like Burp Suite to intercept the traffic between the mobile app and the backend infrastructure. In this case, the lack of TLS/SSL pinning or even basic encryption made the data stream completely transparent.
The following command is a standard starting point for decompressing an APK to begin your own analysis:
apktool d target_app.apk
Once the files are extracted, you can navigate to the AndroidManifest.xml to see exactly what the app is allowed to do. In the case of these smartwatches, the apps requested permissions for location, microphone access, and contact lists, which are entirely unnecessary for the device's advertised functionality.
Real-World Implications for Pentesters
For those of us working on red team engagements or physical security assessments, these devices represent a significant, often overlooked, attack surface. If you are conducting a physical penetration test, look for these devices in the office. They are frequently used by employees who are unaware of the privacy risks. Once connected to the office Wi-Fi via the user's phone, these devices can act as a bridge into the internal network.
The impact of exploitation is not limited to the user's health data. Because these devices are often managed by poorly secured, foreign-hosted cloud infrastructure, they can be used to pivot into other systems or to exfiltrate data from the user's mobile device. The lack of encryption means that any attacker on the same network can easily sniff the traffic and reconstruct the user's activity.
A Note for Defenders
Defending against this is difficult because the devices themselves are often "black boxes" that cannot be patched or secured. The most effective strategy is network segmentation. If your organization allows employees to bring IoT devices into the workplace, ensure they are restricted to a guest network that has no access to internal resources. Furthermore, implement strict egress filtering to prevent these devices from communicating with known malicious or suspicious IP ranges.
The reality is that we are living in an era where the hardware we trust is often the hardware we know the least about. As researchers, our responsibility is to continue pulling these devices apart and exposing the reality behind the marketing. If you find a device that seems too cheap to be true, it is almost certainly a security liability. Start by checking the FCC ID and running the companion app through a static analysis framework. You will rarely be disappointed by what you find.
Vulnerability Classes
Target Technologies
OWASP Categories
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
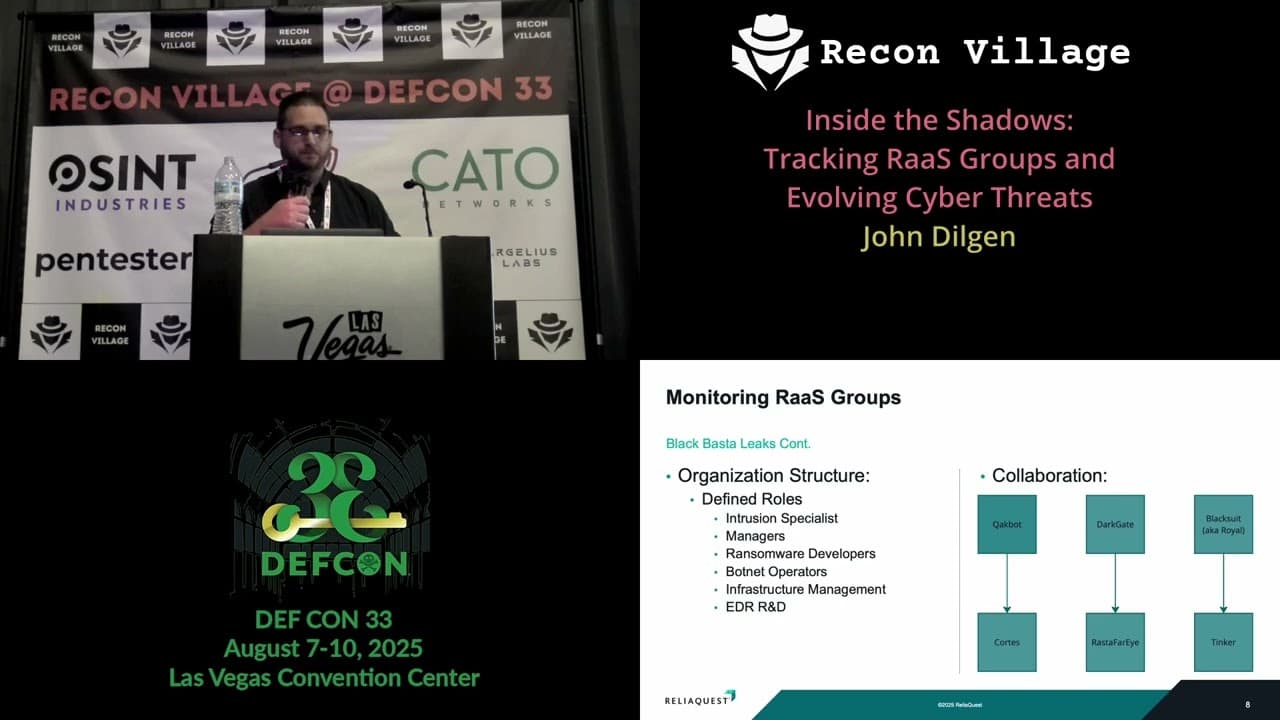
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web

