Attack Surface in Motion: Why Today's Threats Don't Knock First
This talk analyzes the evolution of the cyber threat landscape over the last 20 years, focusing on the shift from manual, targeted attacks to automated, opportunistic exploitation. It highlights the transition from on-premises infrastructure to complex, heterogeneous cloud and IoT environments, which has significantly expanded the attack surface. The speaker emphasizes the rise of initial access brokers (IABs) and the commoditization of infostealer logs as a primary vector for ransomware and other malicious activities. The presentation concludes with a discussion on the role of AI in lowering the barrier to entry for attackers, enabling the rapid creation of exploits and phishing campaigns.
The Death of Perimeter Security: Why Initial Access Brokers Are Winning
TLDR: Modern threat actors have abandoned complex, manual exploitation in favor of buying cheap, pre-harvested credentials from Initial Access Brokers (IABs). By leveraging infostealer logs and misconfigured cloud buckets, attackers bypass traditional perimeter defenses entirely. Pentesters must shift their focus from finding zero-days to auditing identity hygiene and monitoring for leaked session tokens to stay ahead of this trend.
The days of spending weeks crafting a custom exploit chain to bypass a hardened firewall are largely behind us. While the industry remains obsessed with the latest remote code execution vulnerabilities, the reality on the ground is far more mundane and significantly more dangerous. Attackers have realized that breaking into a network is expensive and time-consuming, but buying a valid VPN session or an active SSO token is cheap, fast, and remarkably effective.
The Shift from Exploitation to Acquisition
For years, the standard red team playbook involved scanning for OWASP Top 10 vulnerabilities, finding an unpatched service, and pivoting through the internal network. Today, that approach is often a waste of time. Why bother with a complex SQL injection when you can purchase a full set of corporate credentials for ten dollars on a dark web marketplace?
This commoditization of access is driven by the rise of infostealers. These malware families, which infect endpoints and scrape browser data, have turned every employee machine into a potential entry point. When an infostealer logs a user's session cookies, it effectively bypasses multi-factor authentication. The attacker does not need to know the password; they simply import the stolen session into their own browser and walk through the front door as an authenticated user.
The Anatomy of an IAB Engagement
Initial Access Brokers operate with the efficiency of a supply chain. They do not care about the target's data or the ultimate goal of the intrusion. Their business model is simple: harvest, validate, and sell.
- Collection: The broker deploys infostealers or scans for misconfigured cloud storage to gather data.
- Validation: They verify that the stolen credentials or session tokens are still active.
- Sale: The access is listed on a forum or marketplace, often bundled with information about the target's environment, such as the presence of EDR or specific VPN software.
For a pentester, this changes the scope of an engagement. If you are only testing the external web application, you are missing the point. You need to simulate the IAB workflow. During your next assessment, ask the client for a "assume breach" scenario where you start with a valid, low-privileged session token. You will quickly find that the lack of internal segmentation and the over-reliance on perimeter defenses make lateral movement trivial.
The Role of AI in Lowering the Barrier
The barrier to entry for these attacks has plummeted thanks to the integration of large language models. Attackers are using tools like ChatGPT or Grok to automate the creation of phishing lures, refine their social engineering scripts, and even write scripts to parse through massive datasets of stolen logs.
Previously, an attacker needed a certain level of technical sophistication to manage a botnet or maintain a command-and-control infrastructure. Now, they can offload the heavy lifting to an AI. This allows even low-skill actors to conduct high-volume, targeted campaigns that look indistinguishable from legitimate traffic.
Defending Against the Invisible Intruder
Defending against this is not about buying more expensive security appliances. It is about acknowledging that the perimeter is dead. If you are a defender, your priority must be identity-centric security.
Implement strict session management. If a session token is stolen, it should be invalidated immediately upon any sign of anomalous behavior, such as a change in IP address or user-agent string. Furthermore, enforce Zero Trust principles internally. Even if an attacker gains access to a user's machine, they should not have unfettered access to the entire internal network.
For those of us on the offensive side, we need to stop treating credentials as a secondary finding. They are the primary objective. When you are performing a test, document the ease with which you can move from a stolen session to domain dominance. That is the story that will get the attention of the CISO. The threats are not knocking on the door anymore; they are already inside, using the keys they bought on the dark web. Stop looking for the knock and start watching the internal traffic.
Vulnerability Classes
Target Technologies
Attack Techniques
All Tags
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
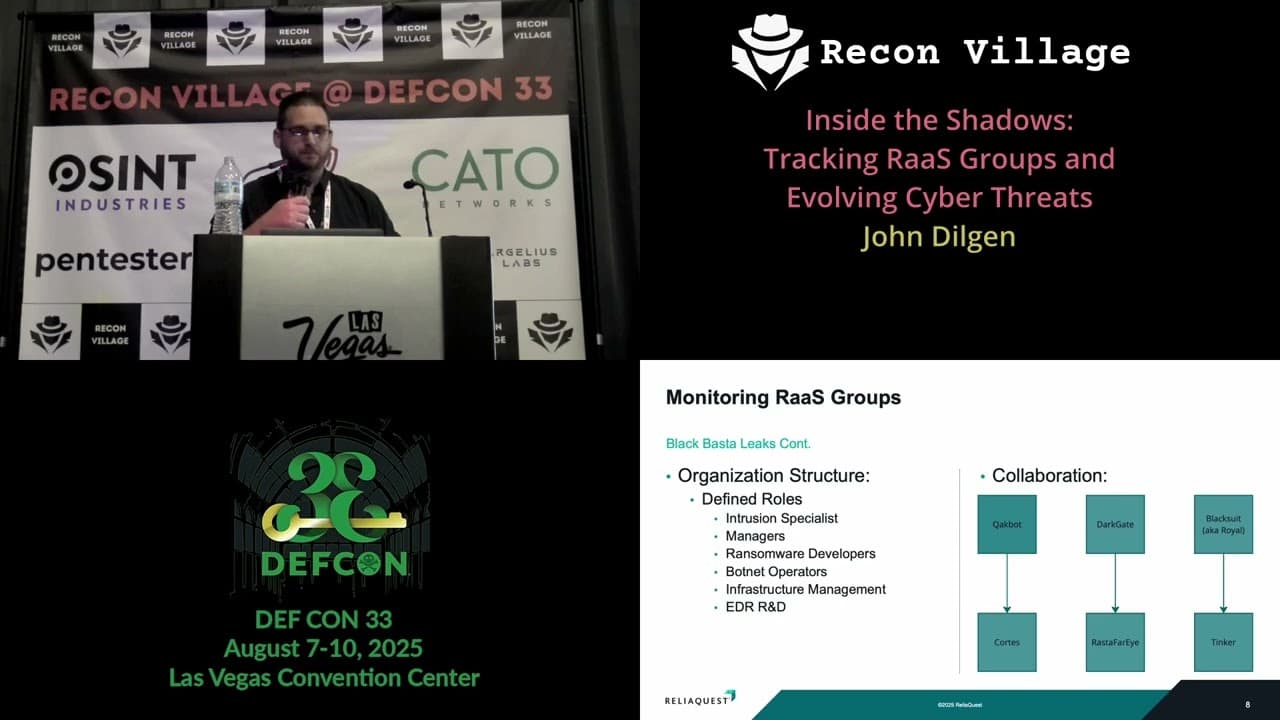
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Kill List: Hacking an Assassination Site on the Dark Web

Unmasking the Snitch Puck: The Creepy IoT Surveillance Tech in the School Bathroom

