Building Stronger Relationships between Security and Engineering Teams
This talk outlines a strategic framework for improving collaboration between security and product engineering teams within a large enterprise. It introduces the 'Security Partner' and 'Security Champion' roles to bridge communication gaps and integrate security requirements into product roadmaps. The presentation details a risk-based engagement model that uses standardized reporting, dashboards, and feedback loops to prioritize security work. The approach aims to reduce friction and foster a culture of shared responsibility for security outcomes.
Why Your Security Program Is Failing to Fix Vulnerabilities
TLDR: Most security programs fail because they treat engineering teams like adversaries rather than partners. By implementing a structured engagement model with dedicated security partners and empowered security champions, you can move from a broken, ticket-heavy process to a collaborative, risk-based workflow. This shift is essential for reducing friction and ensuring that security requirements are actually integrated into product roadmaps.
Security teams often operate in a vacuum, firing off OWASP Top 10 findings into a Jira abyss and expecting developers to drop everything. When that doesn't happen, the relationship sours, and the security team becomes the "department of no." This dynamic is the primary reason why critical vulnerabilities persist in production environments for months or even years. If you are a researcher or a pentester, you have seen this firsthand: you report a valid, high-impact bug, and it sits in a "backlog" until the end of time. The problem isn't that developers don't care about security; it is that they are overwhelmed by a process that lacks context, prioritization, and empathy.
The Failure of the Ticket-Only Model
The traditional approach to security engagement is fundamentally broken. Security teams identify a vulnerability, file a ticket, and then wait for a fix. This creates a one-way street of communication that ignores the reality of product development. Engineering teams are measured by feature velocity and uptime, not by the number of security tickets they close. When security teams act as ticket-pushers, they lose the ability to influence the product roadmap.
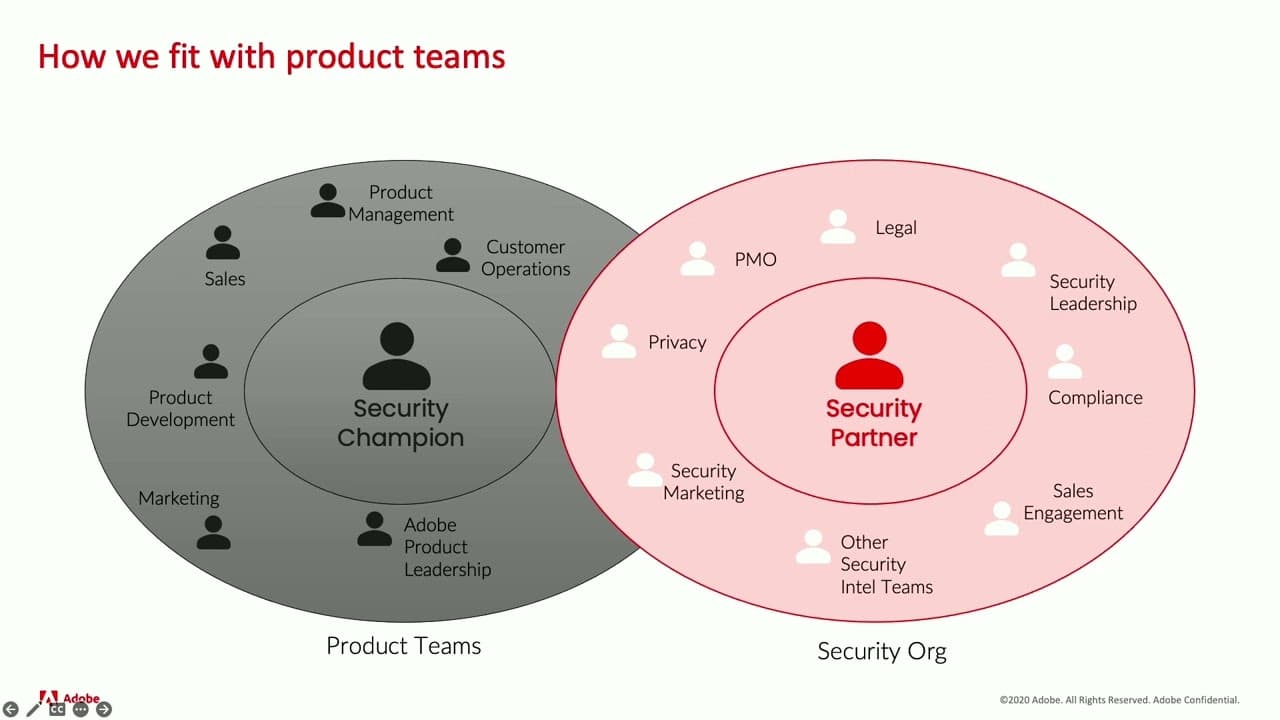
To fix this, you need to move toward a model of active management. This requires two specific roles: the Security Partner and the Security Champion. The Security Partner is a member of the security organization who acts as a subject matter expert for a specific product or service. They are not there to audit; they are there to help. The Security Champion, on the other hand, is an engineer within the product team who has an interest in security. They act as the bridge between the security organization and the engineering team. They are the ones who can explain why a specific CVE matters to their specific codebase and how to prioritize the fix alongside other technical debt.
Building a Risk-Based Engagement Loop
Standardization is the only way to scale this. You cannot have a bespoke, manual process for every team in a large organization. Instead, you need to categorize your products based on their risk profile and visibility. A high-visibility, high-risk product like a core authentication service requires a different level of engagement than an internal tool.
By using a tiered support model, you can allocate your limited security resources where they are needed most. Tier 1 teams get bi-weekly syncs with a dedicated security partner, while lower-tier teams might only interact via Slack or email. This transparency is key. When everyone understands why a team is in a specific tier, it removes the perception of favoritism or arbitrary enforcement.
The reporting mechanism must also be standardized. If you are sending different reports to different teams, you are creating noise. A consistent dashboard that shows risk status, open vulnerabilities, and progress against the security roadmap allows for a common language between security and engineering. When you present this data, focus on the business impact. Instead of saying "you have a cross-site scripting vulnerability," say "this vulnerability puts our customer data at risk and could impact our revenue if it leads to a breach."
Shifting from Adversary to Ally
The most effective security programs are those that provide value back to the engineering team. This means offering training, recognizing security champions for their contributions, and being willing to negotiate on timelines. If a team is struggling to meet a deadline, a security partner should be able to help them understand the trade-offs. Can we implement a compensating control now and fix the root cause in the next sprint? That kind of flexibility builds trust.
When you identify "rockstars"—those security champions who consistently go above and beyond—you need to reward them. This doesn't always mean money. Public recognition in front of their peers or a note to their manager about their impact on the company's security posture goes a long way. These individuals are your force multipliers. They are the ones who will catch issues before they ever reach a formal security review.
The Path to Sustainable Security
If you are a pentester or a researcher, your goal is to find bugs. But if you want those bugs to be fixed, you need to understand the environment you are testing in. If you see a client with a broken security culture, don't just dump a massive report on them. Identify the security champions, talk to the developers, and help them understand the "why" behind your findings.
The goal is to build a system where security is a shared responsibility, not a gatekeeping function. If you can help your clients or your own organization move toward this model, you will see a dramatic increase in the rate of remediation. Stop treating engineering teams like they are the problem. Start treating them like the partners they need to be. The next time you are on an engagement, look for the team that has a clear, risk-based roadmap and a dedicated security champion. You will find that they are the ones who actually fix the bugs you report.
Target Technologies
All Tags
Up Next From This Conference
BSides Salt Lake City Conference Opening
Building Stronger Relationships between Security and Engineering Teams
Why Data Breaches Aren't Like Plane Crashes, but Should Be
Similar Talks

The Dark Side of Bug Bounty

Social Engineering A.I. and Subverting H.I.

