BSides Salt Lake City Conference Opening
This video is a conference opening and logistics presentation for the BSides Salt Lake City event. It outlines the event's core principles of building connections, fostering community, and supporting career development within the cybersecurity industry. The speaker details various event activities, including networking sessions, home labs, lock picking, circuit assembly, and multiple contests.
Building Community and Technical Skills at BSides Salt Lake City
TLDR: The BSides Salt Lake City conference prioritizes hands-on technical growth through dedicated spaces for hardware hacking, lock picking, and competitive CTF challenges. By fostering a collaborative environment, the event helps security professionals bridge the gap between theoretical knowledge and practical application. Attendees can engage with peers to sharpen their skills in circuit assembly, IoT security, and offensive research techniques.
Security conferences often devolve into vendor pitches and high-level strategy sessions that offer little value to those of us actually turning wrenches on targets. When you spend your days hunting for SQL injection or chaining together complex exploit paths, you need a venue that respects your time and provides tangible opportunities to level up. The opening session at BSides Salt Lake City serves as a reminder that the most effective way to advance in this field is through direct, peer-to-peer knowledge transfer and hands-on experimentation.
The Value of Hands-On Labs
Theoretical understanding of a vulnerability is rarely enough to weaponize it effectively during a red team engagement. You need to understand the underlying hardware and software constraints. The organizers at BSides SLC have carved out specific physical spaces for attendees to move beyond the screen and into the hardware layer.
The Home Labs and Lock Pick area is a prime example of this philosophy. For a pentester, physical security is often the overlooked entry point into a facility. Understanding how to manipulate mechanical locks or interface with IoT devices at the circuit level provides a massive advantage when you are on-site. If you are unfamiliar with the basics of lock manipulation, spending an hour with a set of picks is more educational than reading a dozen whitepapers on the subject.
Similarly, the Circuit Assembly area provides a rare opportunity to work with hardware components like the Raspberry Pi Pico. For those of us who spend our time in the web application layer, hardware hacking can seem intimidating. However, the ability to solder a circuit or debug a custom firmware implementation is a force multiplier. It allows you to build custom tools for your engagements, such as specialized implants or data exfiltration devices that bypass standard network-based detection.
Gamification as a Learning Tool
Capture the Flag (CTF) competitions are frequently criticized for being disconnected from real-world scenarios, but when designed well, they are the best way to test your methodology under pressure. The CTF at BSides SLC is explicitly designed to mirror the theme of the event, forcing participants to think creatively about how they would approach an "outer space" themed infrastructure.
For a bug bounty hunter, the value here is in the rapid iteration of ideas. You have a target, you have a set of constraints, and you have a limited amount of time to find a path to the flag. This is exactly what a bug bounty program feels like when you are racing against other researchers to find a critical vulnerability before someone else does. If you find yourself stuck in a rut, participating in a well-structured CTF can force you to adopt new techniques or use tools you might otherwise ignore.
Career Development Through Connection
The industry is currently facing a massive skills gap, and the most effective way to bridge it is through mentorship and networking. The Networking and Recruiting event at BSides SLC is not just about handing out resumes. It is about connecting junior researchers with seniors who can provide guidance on how to navigate the complexities of the industry.
When you are looking to move from a junior role to an intermediate or senior position, you need more than just a certification. You need a network of peers who can vouch for your technical capabilities. The use of color-coded wristbands to identify students and those looking for entry-level roles is a simple but effective way to facilitate these introductions. It removes the friction of trying to figure out who is hiring and who is looking, allowing for more authentic conversations about the actual work involved in a security role.
The Importance of Localized Security Communities
Large, international conferences have their place, but they often lack the intimacy required to build lasting professional relationships. Local events like BSides SLC are where the real work happens. They provide a consistent, recurring venue for researchers in a specific geographic area to meet, share findings, and collaborate on local security challenges.
If you are a researcher, you should be looking for these local hubs. They are the best places to find collaborators for your next research project or to get feedback on a new tool you are developing. The 801Labs group in Salt Lake City, for example, provides a space for ongoing collaboration that extends well beyond the two days of the conference.
Moving Forward
The next time you are evaluating which conferences to attend, look past the keynote speakers and the vendor floor. Ask yourself what you can actually do there. Can you pick a lock? Can you solder a circuit? Can you sit down with a peer and walk through a complex exploit chain? If the answer is no, you are likely wasting your time.
Focus your energy on events that prioritize the technical, hands-on aspects of the craft. The goal is to leave the conference with a new technique in your arsenal or a new contact who can help you solve a problem you have been struggling with for months. Keep building, keep breaking, and keep sharing your findings with the community. That is how we stay ahead of the curve.
Up Next From This Conference
BSides Salt Lake City Conference Opening
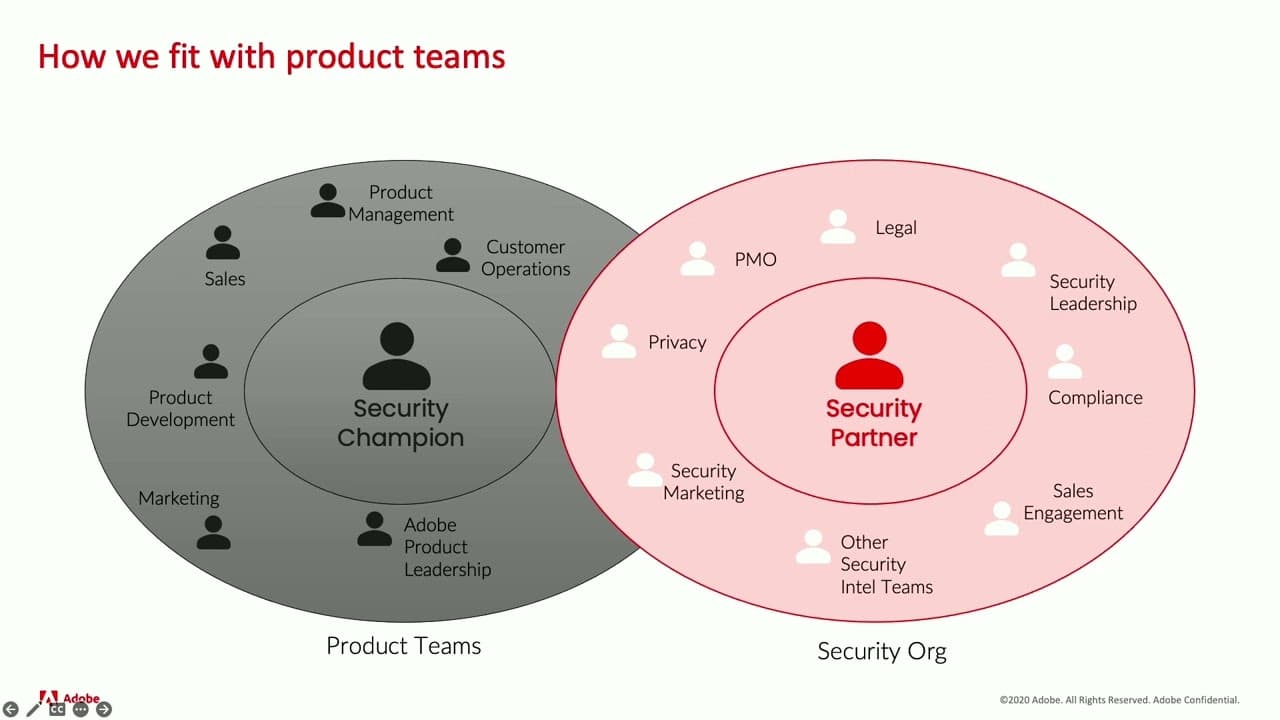
Building Stronger Relationships between Security and Engineering Teams
Why Data Breaches Aren't Like Plane Crashes, but Should Be
Similar Talks

Unmasking the Snitch Puck: The Creepy IoT Surveillance Tech in the School Bathroom

Anyone Can Hack IoT: A Beginner's Guide to Hacking Your First IoT Device

