Why Data Breaches Aren't Like Plane Crashes, but Should Be
This talk analyzes the organizational and procedural failures behind major data breaches, drawing parallels to the aviation industry's rigorous post-incident investigation and safety protocols. It highlights how common security oversights, such as hard-coded credentials and broken access controls, lead to significant compromises. The speaker advocates for a culture of transparency and continuous learning, suggesting that security teams should conduct regular, engaging training sessions based on real-world breach analysis to improve organizational resilience.
Why Your Internal Slack and SaaS Permissions Are the New Perimeter
TLDR: Modern data breaches are rarely about sophisticated zero-day exploits and almost always about basic failures in access control and credential management. By analyzing recent high-profile incidents like the Uber breach, we can see that attackers are bypassing traditional network perimeters by exploiting over-privileged SaaS accounts and hard-coded credentials. Pentesters should shift their focus toward auditing identity and access management (IAM) configurations and internal communication platforms to find the real paths to critical data.
Security professionals often obsess over the latest remote code execution vulnerability or a complex chain of exploits, but the reality of modern offensive operations is far more mundane. When you look at the actual mechanics of recent major data breaches, you rarely find a state-sponsored actor burning a million-dollar exploit. Instead, you find an attacker who simply logged in. The perimeter has shifted from the network edge to the identity layer, and if you are still focusing your testing efforts solely on external-facing web applications, you are missing the most effective attack vectors.
The Anatomy of an Identity-Based Breach
The Uber incident from late 2022 serves as a masterclass in how modern, identity-centric attacks unfold. The attacker did not need to break through a firewall or find a flaw in a custom web application. They started by compromising a contractor’s credentials via a simple phishing campaign, which is a classic T1566: Phishing maneuver. While the target had multi-factor authentication (MFA) enabled, the attacker simply flooded the user with push notifications until they eventually clicked "approve." This is a perfect example of MFA fatigue, a technique that highlights the human element in A07:2021-Identification and Authentication Failures.
Once the attacker gained access to the VPN, they did not need to perform complex lateral movement. They immediately found a network share containing a PowerShell script. This script was not obfuscated or hidden; it contained hard-coded administrative credentials for the company's Privileged Access Management (PAM) system. This is a textbook case of T1552: Unsecured Credentials, specifically looking for credentials stored in configuration files or scripts.
Why Your Developers Are Your Biggest Liability
Hard-coded credentials in scripts, source code, or CI/CD pipelines remain one of the most reliable ways to escalate privileges. During an engagement, you should prioritize searching for these files. If you find a repository or a shared drive, do not just look for sensitive data; look for the keys to the kingdom. A simple grep or a more advanced tool like gitleaks can often uncover secrets that provide access to AWS, GCP, or internal administrative dashboards.
The impact of these findings is massive. In the Uber case, the attacker gained access to:
- Source code repositories
- AWS and GCP administrative consoles
- G-Suite administrative panels
- Internal financial dashboards
- Slack administrative controls
Once the attacker had access to the Slack workspace, they were able to post messages as an administrator, effectively taunting the security team and providing real-time updates on their progress. This level of access is only possible when A01:2021-Broken Access Control is ignored at the organizational level. When you are testing, ask yourself: if I compromise this one user, what SaaS applications can I access, and what are their permission levels?
Shifting Your Testing Strategy
For a pentester or bug bounty hunter, the goal is to map out the identity landscape. Do not just look for SQL injection or XSS. Look for the connections between identities and services. If you are performing an internal assessment, focus on:
- Credential Harvesting: Look for scripts, environment variables, and configuration files that contain hard-coded secrets.
- SaaS Permissions: Audit the permissions of the accounts you compromise. Can they access the company's Jira, Slack, or cloud management consoles?
- Logging and Monitoring: Check if your actions are being logged. If you can perform administrative actions without triggering an alert, you have found a critical A09:2021-Security Logging and Monitoring Failures.
Defenders need to move beyond simple perimeter defense. Implementing robust logging for all SaaS applications and enforcing strict, least-privilege access for every identity is non-negotiable. If a contractor does not need access to the production AWS environment, they should not have it. If a developer does not need to store credentials in a script, they should be using a secrets management service.
The most effective way to improve your team's security posture is to learn from these failures. When a breach happens, do not just read the headlines. Dig into the technical reports, such as the Equifax Congressional Report, which remains one of the most detailed post-mortems in history. Use these stories to educate your developers and stakeholders. When you can show them exactly how a simple, preventable mistake led to a massive compromise, you change the conversation from theoretical risk to concrete reality.
Stop looking for the "cool" exploit and start looking for the "easy" one. The path to the data is almost always paved with poor access controls and exposed credentials. If you can find those paths before an attacker does, you have done your job.
Vulnerability Classes
Attack Techniques
OWASP Categories
All Tags
Up Next From This Conference
BSides Salt Lake City Conference Opening
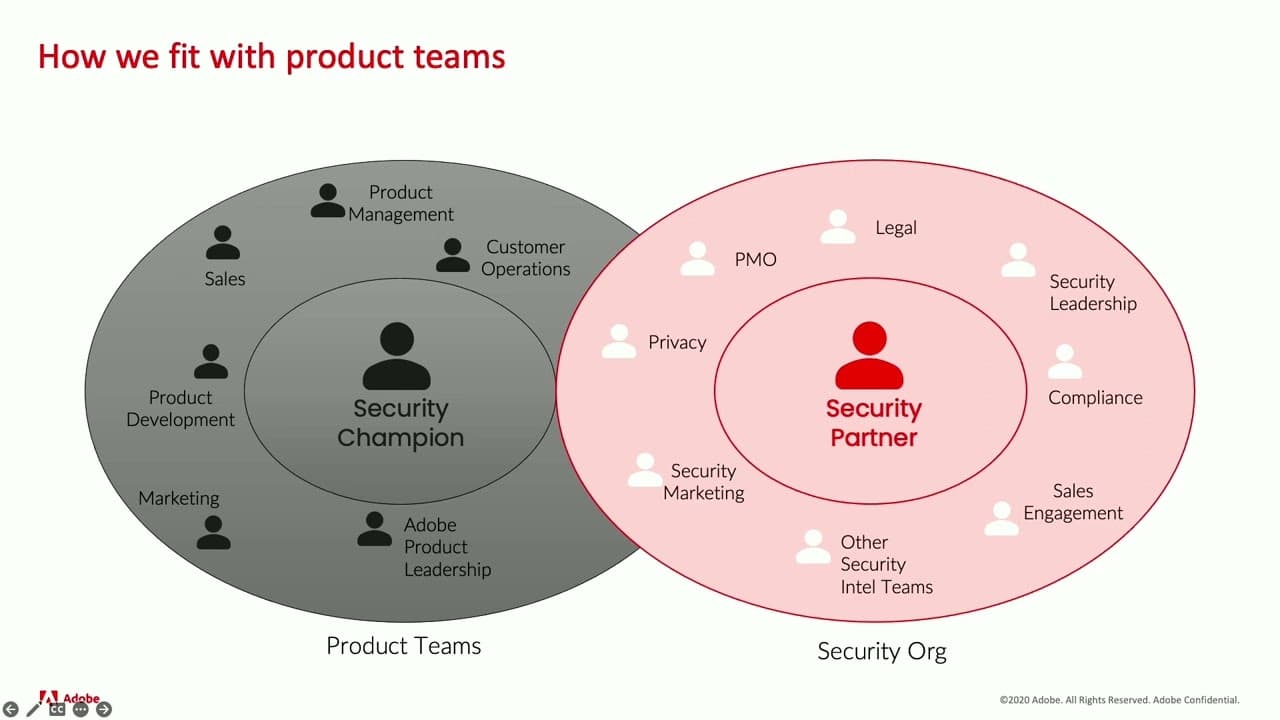
Building Stronger Relationships between Security and Engineering Teams
Why Data Breaches Aren't Like Plane Crashes, but Should Be
Similar Talks

Kill List: Hacking an Assassination Site on the Dark Web

Counter Deception: Defending Yourself in a World Full of Lies

