Building an Auto-Remediation Platform for the Cloud
This talk demonstrates the design and implementation of a centralized, event-driven auto-remediation platform for cloud environments. The system leverages webhooks and event buses to ingest security findings from various Cloud Security Posture Management (CSPM) tools and automatically trigger remediation workflows. The approach emphasizes using existing CSPM evaluation logic rather than custom-built detection, combined with just-in-time (JIT) training for developers to reduce future misconfigurations.
Stop Chasing CSPM Alerts and Start Automating Remediation
TLDR: Most security teams are drowning in a sea of low-priority CSPM alerts that never get fixed. This talk outlines a practical, event-driven architecture that uses Amazon EventBridge and AWS Lambda to automatically remediate common cloud misconfigurations. By shifting from manual ticket-based workflows to automated, developer-focused remediation, you can drastically reduce your attack surface while simultaneously training your engineering team.
Cloud security is a volume problem. If you are running a mature environment, your Cloud Security Posture Management (CSPM) tools are likely generating hundreds of alerts every week. Most of these are low-hanging fruit: unencrypted S3 buckets, overprivileged IAM roles, or security groups with overly permissive ingress rules. When you treat these as manual tasks for a security analyst to triage, you lose. You create a backlog that grows faster than your team can clear it, and you leave the door open for attackers to exploit these known misconfigurations while your team is busy clicking "ignore" on false positives.
The Architecture of Automated Response
The core issue with most CSPM workflows is that they are reactive and siloed. You get an alert, you open a ticket, a developer ignores the ticket, and the misconfiguration persists. The solution is to move the remediation logic out of the CSPM tool and into a centralized, event-driven pipeline.
By using Amazon EventBridge, you can ingest findings from multiple sources—AWS Config, CloudTrail, or third-party CSPM providers—and route them to a unified remediation bus. This decouples the detection logic from the response logic. You no longer care which tool found the issue; you only care that an event hit your bus.
When an event arrives, your pipeline should follow a simple, three-step logic:
- Check the Exception List: Before doing anything, verify if the resource is explicitly allowed to be in that state. This is your first line of code. If it is not on the exception list, proceed.
- Respond: Execute the remediation. This could be as simple as updating a resource policy or as drastic as terminating a non-compliant instance.
- Train: This is the most critical step. Identify the user who created the resource via CloudTrail and send them a notification.
Why You Should Never Write Your Own Evaluation Logic
A common trap for security engineers is trying to build a custom detection engine. Do not do this. Identifying risk is a commodity. Your CSPM tools are already doing the heavy lifting of parsing cloud APIs and comparing them against security standards. If you try to replicate that logic, you will spend your entire career maintaining regex patterns and API calls.
Instead, treat your CSPM tools as simple event emitters. If a tool flags an unencrypted RDS instance, let the tool do the evaluation. Your remediation service just needs to receive the event, verify the exception list, and trigger the fix.
For the remediation itself, keep the code minimal. A typical remediation Lambda function should be under 100 lines of code. Here is a conceptual example of how you might structure a response to an unencrypted storage finding:
import boto3
def lambda_handler(event, context):
resource_id = event['detail']['resource_id']
client = boto3.client('rds')
# Remediation logic: Enable encryption
client.modify_db_instance(
DBInstanceIdentifier=resource_id,
StorageEncrypted=True,
ApplyImmediately=True
)
# Notify the user and log to the bus
send_notification(event['user_identity'])
return {"status": "remediated"}
The Power of Just-in-Time Training
The biggest win in this architecture is the "Train" step. Most developers do not want to write insecure code; they just want to ship features. When they receive an automated email that says, "Your S3 bucket was created without encryption, so we enabled it for you," they learn.
If you include a Jinja2 template in that email that shows them the exact Infrastructure as Code (IaC) snippet they should have used, you are providing value. You are turning a security alert into a teaching moment. Over time, this reduces the number of new misconfigurations hitting your environment because your developers are learning the secure patterns as they work.
Operationalizing the Pipeline
When you build this, you must account for operational risk. You are essentially building a "kill switch" for your infrastructure. If your remediation logic is flawed, you could accidentally delete production databases.
To mitigate this, implement a centralized circuit breaker. If your system detects a sudden spike in remediation events—perhaps a misconfigured IaC template just deployed 500 non-compliant resources—the system should automatically halt and alert a human. You also need to ensure that your remediation service has the absolute minimum set of permissions required to perform its job. Use IAM policy conditions to restrict the service to only modify specific resource types or tags.
This approach is not about replacing your security team; it is about scaling them. By automating the mundane, you free up your researchers and pentesters to focus on the complex, high-impact vulnerabilities that require human intuition. Stop treating your CSPM as a reporting tool and start treating it as an API for your automated defense platform. The tools are already there, and the logic is already written. You just need to connect the dots.
Vulnerability Classes
Target Technologies
Attack Techniques
All Tags
Up Next From This Conference
BSides Salt Lake City Conference Opening
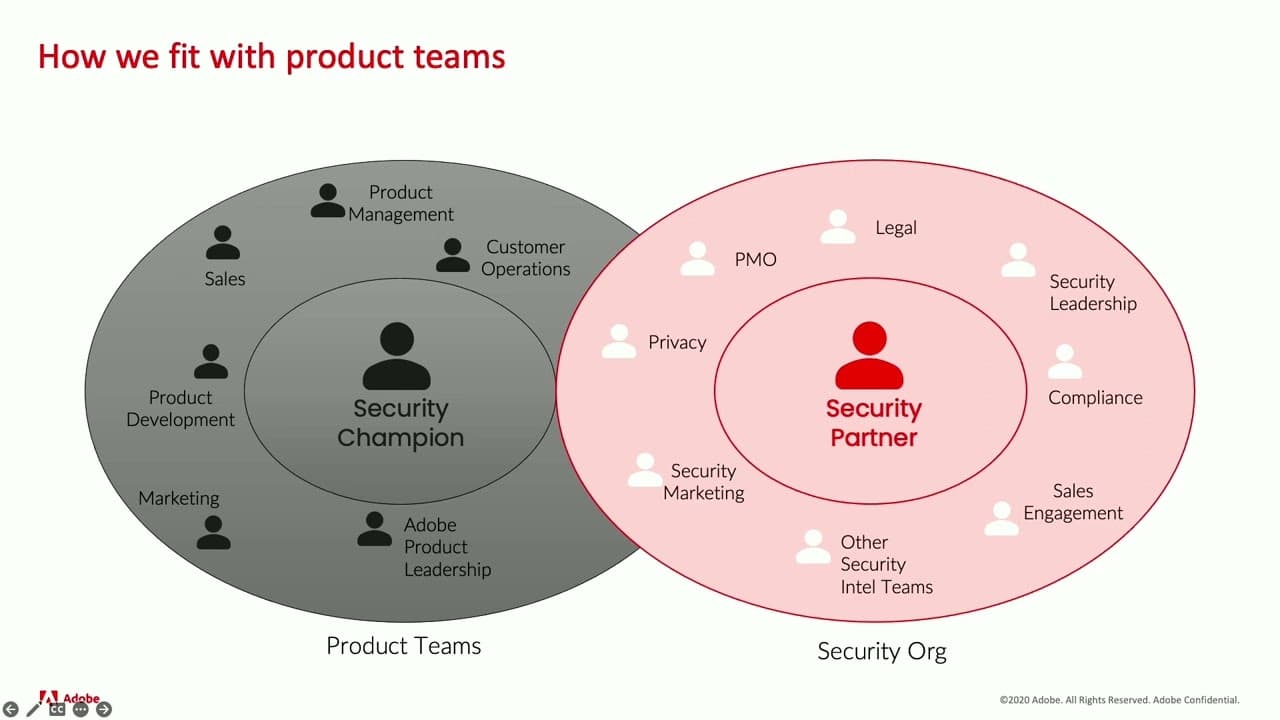
Building Stronger Relationships between Security and Engineering Teams
Why Data Breaches Aren't Like Plane Crashes, but Should Be
Similar Talks

Firewalls Under Fire: China's Ongoing Campaign to Compromise Network Protection Devices

We are currently clean on OPSEC: The Signalgate Saga

