Discord OSINT: An Empathic Banana and a Data Scraper Walk into a Search Bar
This talk demonstrates the use of Discord's search functionality and public API to perform OSINT on users and servers. It details how data scrapers like 'Spy.pet' and 'Searchcord' harvest massive amounts of public Discord messages, attachments, and user metadata. The speaker highlights the privacy risks of public Discord channels and provides actionable advice for users and server administrators to harden their configurations against such scraping. The presentation concludes with an analysis of the operational security (OPSEC) failures that led to the identification and subsequent takedown of these scraping services.
Scraping Discord: How Public Channels Become Massive OSINT Databases
TLDR: Recent research into Discord scraping services like Spy.pet and Searchcord reveals how public channel data is harvested at scale to build searchable OSINT databases. These platforms exploit Discord's "discoverable" server feature to index billions of messages, attachments, and user metadata without ever joining servers manually. Pentesters and researchers should treat public Discord channels as inherently compromised and audit their own account connections to prevent metadata leakage.
Discord is often treated as a private, ephemeral space for communities, but that assumption is a liability for anyone discussing sensitive technical details or managing infrastructure. The reality is that public, discoverable servers are being indexed by automated scrapers that function like search engines for human conversation. This is not a theoretical risk. We have seen services like Spy.pet and Searchcord aggregate billions of messages, effectively turning public Discord activity into a permanent, searchable record that can be used for doxxing, social engineering, or mapping out an organization's internal communications.
The Mechanics of Large-Scale Discord Scraping
The technical core of these scrapers relies on abusing Discord's native discovery features. Instead of needing to join every server, these scrapers leverage the platform's public API to crawl servers marked as "discoverable." By entering a "preview mode," the scrapers can ingest the entire history of public channels without triggering standard join events or requiring an account to be physically present in the server.
Once the data is ingested, it is indexed into a backend that allows for complex queries. The most dangerous aspect for a researcher is the ability to search by username or keyword across thousands of servers simultaneously. If a developer accidentally pastes an API key, a internal hostname, or a sensitive configuration snippet into a public channel, it is indexed almost instantly.
The scrapers also perform correlation across different platforms. By scraping user profiles, these tools can link a Discord account to other identities if the user has linked their GitHub, Steam, or Spotify accounts in their profile settings. This is a classic OWASP A01:2021-Broken Access Control scenario where the user assumes their profile data is only visible to their immediate community, while in reality, it is being harvested by third-party aggregators.
Operational Security Failures
The takedown of these services provides a masterclass in why OPSEC matters for the attackers themselves. In the case of Spy.pet, the service was identified and eventually shut down because the operator failed to maintain basic anonymity. They used the same cat-themed profile pictures across multiple platforms, which allowed researchers to correlate their activity and eventually dox them.
Furthermore, the operators often relied on Cloudflare for protection, but when the volume of abuse reports became too high, they were forced to migrate to DDoS-Guard. This migration often leaves a trail of infrastructure changes that can be tracked. For a pentester, the lesson here is clear: even if you are building a tool that operates in a gray area, your own digital footprint is the most likely vector for your exposure.
Practical Risks for Pentesters
If you are conducting a red team engagement, you should be checking these databases for your target's footprint. If an employee has been active in a public server related to their company's tech stack, you might find internal project names, email addresses, or even code snippets that were never intended for public consumption.
To protect yourself and your team, you need to audit your Discord presence. Go to your User Settings and check the Connections tab. If you have linked your GitHub or other professional accounts, consider removing them. These links are a goldmine for scrapers trying to build a comprehensive profile of a target.
For server administrators, the most effective defense is to set the server's verification level to the highest possible setting. This requires users to have a verified phone number attached to their account before they can send messages. While this does not stop a scraper from reading public channels, it significantly increases the cost and complexity for an attacker to interact with your community. Additionally, ensure that your server is not listed in the public server discovery directory unless it is absolutely necessary.
Moving Forward
The era of thinking that public Discord channels are "safe" is over. These scrapers are not going away; they are simply evolving to target different platforms and more niche communities. As researchers, we need to be aware that our public-facing communication is being archived by third parties.
Before you post that next snippet of code or discuss a new vulnerability in a public channel, ask yourself if you would be comfortable with that information appearing in a searchable, public database tomorrow. If the answer is no, move the conversation to a private, invite-only server or a more secure communication channel. The data you leave behind in public channels is permanent, and it is being indexed right now.
Vulnerability Classes
Target Technologies
OWASP Categories
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
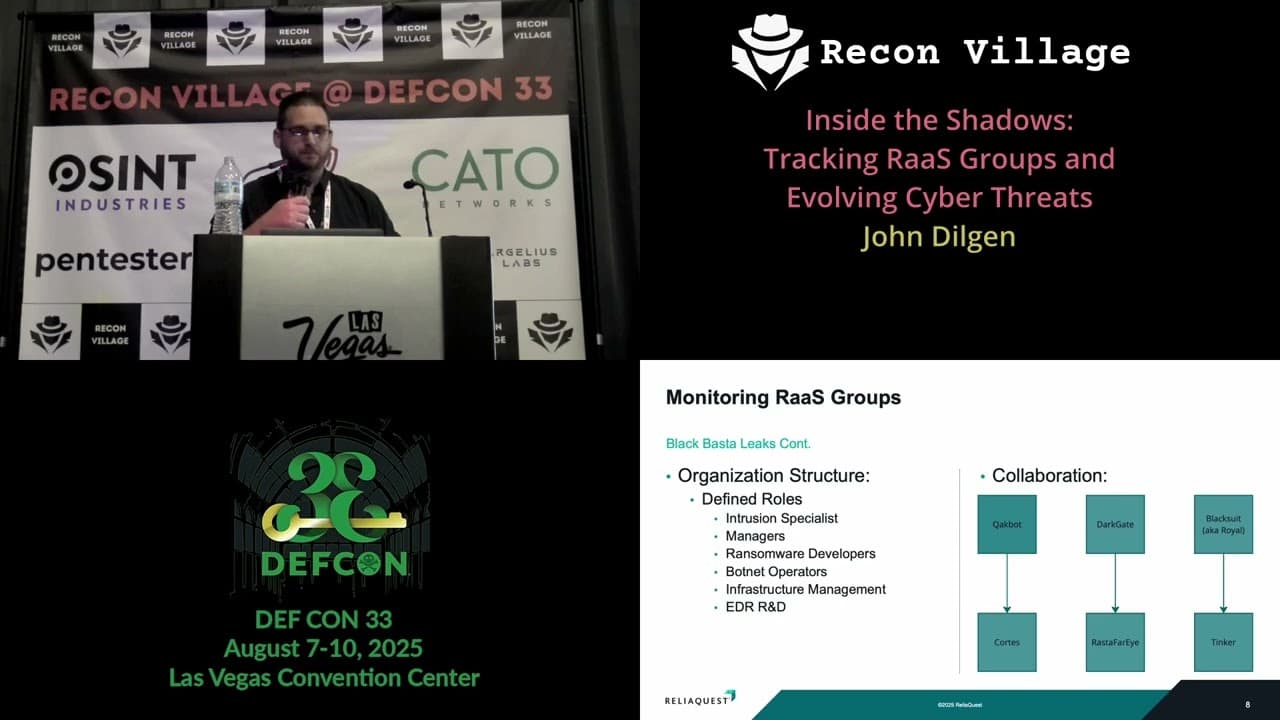
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web

