How Small Businesses Can Prepare for Big Attacks
This talk provides a high-level overview of cybersecurity best practices for small and medium-sized businesses (SMBs) to mitigate common threats like ransomware and phishing. It emphasizes the importance of implementing defense-in-depth strategies, including multi-factor authentication, robust password management, and regular security assessments. The speaker highlights that SMBs are frequent targets for automated attacks and stresses the necessity of having a tested incident response plan to ensure business continuity.
Why Your Small Business Clients Are the Easiest Targets for Ransomware
TLDR: Small and medium-sized businesses (SMBs) are currently the primary targets for automated ransomware campaigns because they lack basic security hygiene and incident response capabilities. Attackers leverage common entry vectors like phishing and exposed legacy services to gain initial access, often finding little resistance. Pentesters and researchers should focus on these low-hanging fruits, as they represent the most significant risk to business continuity for smaller organizations.
Security researchers often fixate on sophisticated zero-day exploits or complex supply chain attacks, but the reality of the current threat landscape is far more mundane. While the industry chases headlines about nation-state actors, the vast majority of successful breaches against small and medium-sized businesses (SMBs) are driven by automated, opportunistic attacks. These campaigns do not require advanced tradecraft. They rely on the fact that many organizations still operate with the security equivalent of an unlocked front door.
The Mechanics of Opportunistic Exploitation
Attackers treat SMBs as a numbers game. When a threat actor scans the internet for vulnerable services, they are not looking for a specific target; they are looking for a specific configuration. A legacy server running an unpatched version of PHP or an exposed Amazon S3 bucket with overly permissive access controls is a beacon for automated exploitation tools.
The attack flow is almost always the same. It starts with T1566-phishing to gain initial access. Once inside, the attacker performs minimal reconnaissance to identify high-value assets. If the environment lacks basic Identity and Access Management controls, the attacker can move laterally with ease. The final objective is rarely data exfiltration for espionage; it is T1486-data-encrypted-for-impact, where the attacker encrypts the entire environment and demands a ransom.
Why Technical Controls Fail
Many SMBs believe they are protected because they have installed off-the-shelf antivirus software. However, modern endpoint protection platforms like CrowdStrike or SentinelOne are only effective if they are properly configured and monitored. A common failure point is the lack of a centralized security operations center (SOC) or a managed service provider (MSP) that actually reviews the alerts.
During a penetration test, you will frequently find that these tools are installed but running in a "monitor-only" mode, or worse, they are completely disabled due to a previous compatibility issue with a legacy application. When you encounter a client with a "set it and forget it" mentality toward their security stack, you are looking at a client that will be compromised within hours of a determined attacker finding their perimeter.
The Human Element and Phishing
Phishing remains the most effective way to bypass technical defenses. Even with advanced email filtering, the human element is the ultimate variable. If an organization does not conduct regular, realistic phishing simulations, they are essentially training their employees to be the perfect delivery mechanism for malware.
When testing these environments, focus on the lack of Multi-Factor Authentication (MFA). If you can compromise a single user account via a simple credential harvesting page, you have effectively bypassed the entire network perimeter. In many cases, the lack of MFA on critical services like email or VPNs is the single biggest vulnerability in the entire organization.
Building a Resilient Defense
Defenders must move beyond the idea that a single tool will solve their problems. A defense-in-depth strategy is not just a buzzword; it is a necessity. This means implementing Least Privilege access, ensuring that every critical system requires MFA, and maintaining immutable, off-site backups.
The most critical component, however, is the incident response plan. Most SMBs do not have one. They assume that if they get hit, they will just "restore from backups." But if those backups are connected to the network, they will be encrypted along with the production data. A tested, offline backup strategy is the only thing standing between a business and total closure.
What Pentesters Should Do Next
When you are engaged to test an SMB, stop looking for the "cool" exploit. Start by looking for the gaps that allow for easy, automated entry. Check for exposed RDP ports, verify if MFA is actually enforced on all cloud services, and test whether the client’s "security team" (often just an overworked IT generalist) can detect a simulated phishing attempt.
If you find a vulnerability, document it clearly in terms of business risk. Explain that an unpatched server is not just a technical debt issue; it is a potential bankruptcy event. Your goal is to force the organization to prioritize security as a core business function rather than an IT afterthought. If you can help them build a culture where reporting a suspicious email is rewarded rather than punished, you have done more for their security than any single patch ever could.
Vulnerability Classes
Tools Used
Target Technologies
OWASP Categories
Up Next From This Conference
BSides Salt Lake City Conference Opening
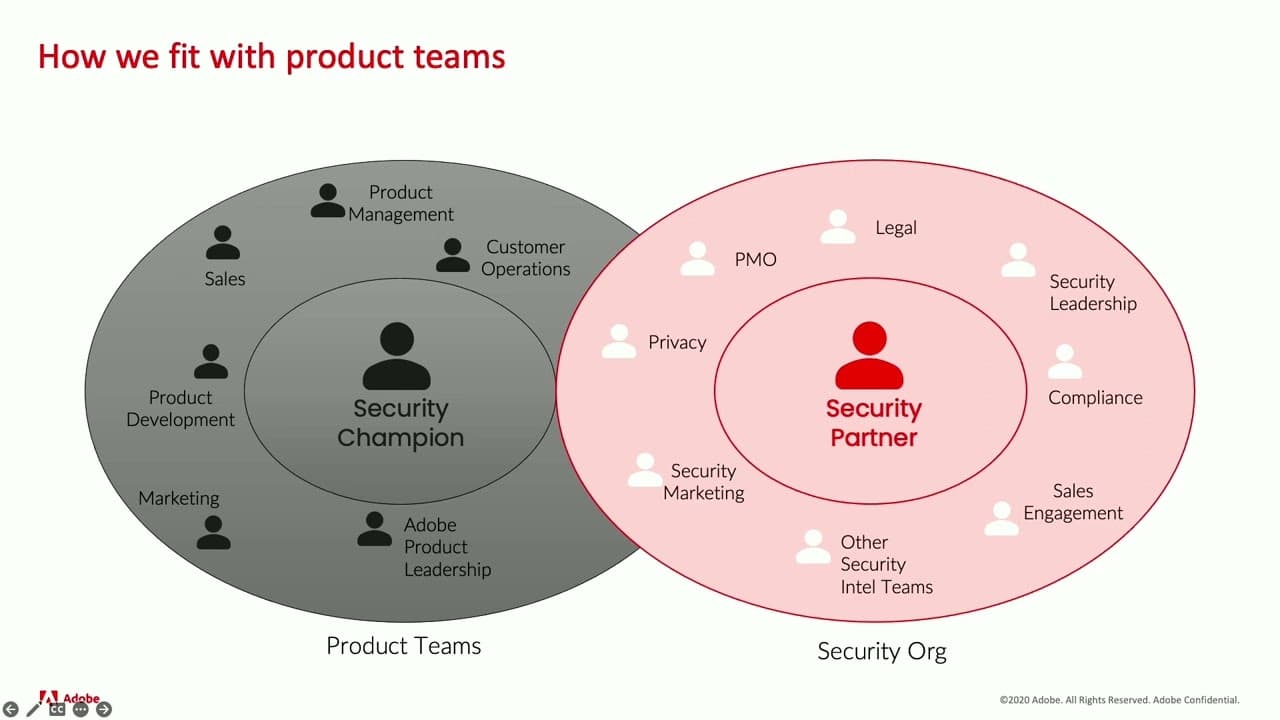
Building Stronger Relationships between Security and Engineering Teams