How to Become One of Them: Deep Cover Operations in Cybercriminal Communities
This talk details the methodology for conducting deep-cover infiltration into cybercriminal communities to gather high-value threat intelligence. It focuses on the human tradecraft required to build credibility, establish personas, and maintain operational security (OPSEC) within closed-source threat actor forums. The presenters emphasize that human intelligence (HUMINT) remains superior to automated scraping for identifying pre-public threats and understanding adversary intent. The session provides a framework for source selection, persona development, and the ethical considerations of managing long-term infiltration operations.
Beyond Scrapers: Why Human Intelligence Still Rules the Dark Web
TLDR: Automated scraping tools are insufficient for identifying pre-public threats because they fail to penetrate the closed-source, invite-only forums where high-value intelligence lives. This talk outlines a framework for deep-cover infiltration, emphasizing persona development, long-term trust building, and the ethical management of human intelligence operations. For security researchers and threat hunters, the takeaway is that human tradecraft remains the only way to gain early warning of adversary intent before it hits public feeds.
Automation has become the default setting for modern threat intelligence. We build scrapers, deploy bots, and feed massive datasets into LLMs, hoping to catch the next big ransomware campaign before it hits our clients. While these tools are excellent at identifying known indicators of compromise, they are fundamentally blind to the most critical phase of an attack: the planning. The most dangerous threat actors do not broadcast their intentions on public channels. They operate in closed-source, invite-only forums where trust is the only currency that matters.
The Limits of Automated Intelligence
If you rely solely on automated tools, you are always playing catch-up. Scrapers are great at finding leaked credentials or identifying common vulnerabilities like those tracked in OWASP Top 10, but they cannot tell you who is currently negotiating a ransomware payout or which specific organization is being targeted for an initial access broker (IAB) sale.
Human intelligence, or HUMINT, fills this gap. It is the practice of embedding yourself within these communities to observe adversary behavior in real-time. This is not about running a script; it is about building a persona that can survive the scrutiny of veteran threat actors. If your persona lacks a plausible backstory, consistent linguistic patterns, or the right technical knowledge, you will be identified and banned before you ever see a private message.
Crafting the Persona
Building a credible persona is a deliberate, time-consuming process. You cannot simply register an account and start asking questions. You must first lurk, observing the community's internal hierarchy, their preferred slang, and the specific technical topics they prioritize.
When you finally begin to engage, your interactions must be low-risk. Start by asking technical questions that align with your persona’s supposed expertise. If you are posing as a developer, ask about specific obfuscation techniques or CVE-2024-21887 exploitation nuances. The goal is to provide value to the community, not to extract it. Once you have established a baseline of credibility, you can begin to move into private channels where the high-value intelligence is actually exchanged.
The Mechanics of Infiltration
Successful infiltration requires a strict adherence to operational security. You must maintain a consistent identity across multiple platforms. If your persona claims to be from a specific region, your activity must align with that region's time zone. A sudden shift in your posting frequency or a change in your linguistic style is a dead giveaway that you are not who you claim to be.
One of the most effective techniques for gathering intelligence is the use of subtle conversation starters. Instead of asking direct questions, which can trigger suspicion, use shared curiosity as a bridge. For example, asking for advice on a specific tool or commenting on a recent, well-known incident allows you to gauge the threat actor's perspective without appearing like an investigator.
# Example of a low-risk engagement pattern
# 1. Observe forum activity for 2-4 weeks
# 2. Post a technical question related to a recent CVE
# 3. Offer a minor, harmless resource to a respected member
# 4. Wait for an invitation to a private channel
Ethical Boundaries and Risk Management
Infiltration is a high-stakes game. You are operating in a legal gray zone, and the risk of exposure is constant. If you are caught, you risk being doxxed or blacklisted from the very communities you need to monitor. More importantly, you must have clear internal policies regarding what is acceptable.
Never participate in illegal activities to maintain your cover. If a threat actor asks you to perform a task that crosses the line, you must have a pre-planned exit strategy. Your organization should have a defined escalation path that dictates exactly when to pull the plug on an operation. The goal is to gather intelligence, not to facilitate the crime.
Why This Matters for Pentesters
For those of us in the field, this methodology is a blueprint for better threat modeling. When you are conducting a red team engagement, you are not just testing a network; you are testing the organization's ability to detect a sophisticated adversary. By understanding how threat actors operate in these private forums, you can better simulate their reconnaissance and initial access phases.
You should be looking for the same things these actors look for: misconfigured services, exposed internal documentation, and weak identity management. The next time you are scoping an engagement, ask yourself what a threat actor in a private forum would already know about your target. If you can answer that, you are already ahead of the curve.
Human tradecraft is not going away. As long as cybercrime remains a human-driven enterprise, the most valuable intelligence will remain hidden behind the barriers of trust. Stop relying on the noise of automated scrapers and start investing in the signal that only human interaction can provide. The next major breach is being planned right now, and the only way to see it is to be in the room where it happens.
Tools Used
Target Technologies
Attack Techniques
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
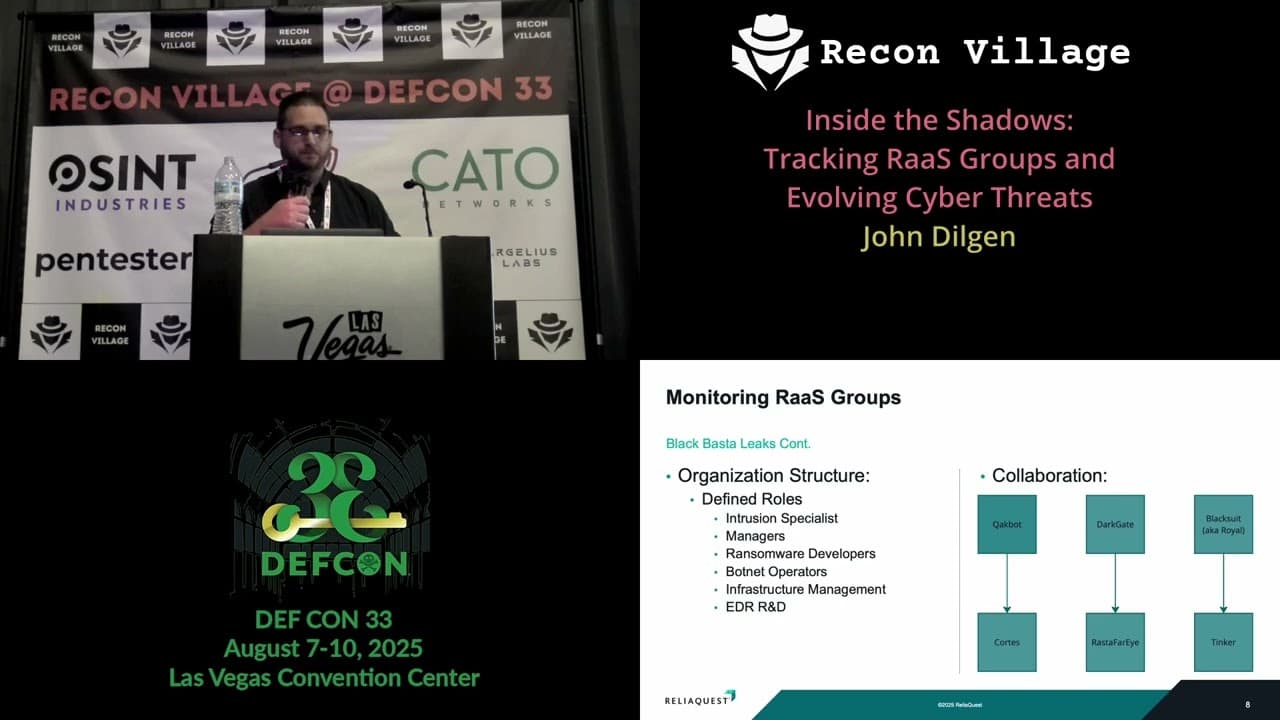
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web

