Next Level SOC Automation
This talk demonstrates how to build custom Google Chrome extensions to automate security operations center (SOC) workflows. The speaker shows how to inject custom buttons into web pages and create context menu items to perform automated tasks like vulnerability lookups and external service pivoting. This technique allows analysts to reduce manual effort and standardize processes by directly interacting with the browser's Document Object Model (DOM) and APIs. The presentation includes a practical walkthrough of the manifest.json configuration and JavaScript code required to implement these features.
Automating Your SOC Workflow with Custom Chrome Extensions
TLDR: Security operations center analysts often waste hours on repetitive tasks like manual lookups and context switching between disparate tools. By building custom Chrome extensions, you can inject functionality directly into the browser DOM to automate these workflows and standardize incident response. This post breaks down how to use the Chrome Extension API to inject buttons and context menu items that streamline your daily security operations.
Security analysts spend a massive portion of their day trapped in a cycle of manual, repetitive tasks. You open a ticket, copy an IP or hash, navigate to a threat intelligence portal, paste the indicator, and wait for the results. Then you repeat the process for the next tool. This context switching is not just a productivity killer; it is a primary driver of analyst burnout and a major source of human error. If you are a researcher or a pentester, you likely have your own set of "quick links" or bookmarks, but those are static and disconnected from the page you are actually viewing.
The most effective way to solve this is to stop treating your browser as a passive viewer and start treating it as a programmable interface. By building custom Chrome extensions, you can bridge the gap between your detection platforms and your intelligence sources. You do not need to be a full-stack developer to pull this off. The browser is just a collection of HTML, CSS, and JavaScript, and the Chrome Extensions API gives you the keys to manipulate that environment in real-time.
Injecting Functionality into the DOM
The core of this technique involves using content scripts to interact with the Document Object Model (DOM) of the pages you visit. When you are looking at a project page on PyPI, for example, you might want to know if that package has known vulnerabilities. Instead of manually searching, you can write a script that detects the project name in the URL, crafts a search query, and injects a "Check Vulnerabilities" button directly into the page header.
To do this, you need a manifest.json file that defines your extension's permissions and scripts. For a modern Manifest V3 extension, you will need to declare the tabs and contextMenus permissions if you plan on interacting with browser tabs or right-click menus.
"permissions": [
"contextMenus",
"tabs"
],
"host_permissions": [
"<all_urls>"
]
Once your manifest is set, your content script can use document.querySelector to find the exact element where you want to inject your button. The key is to wait for the page to load the specific element you are targeting. A simple waitForElement function—often sourced from community repositories like Stack Overflow—ensures your script does not try to inject a button into a non-existent container.
Pivoting with Context Menus
While buttons are great for specific pages, context menus are the real workhorse for a general-purpose security tool. By right-clicking on a selected string—like an IP address, a file hash, or a domain—you can trigger an action that pivots directly to a tool like VirusTotal.
The logic here is straightforward. You register a listener in your background service worker that triggers when the user selects text and clicks your custom menu item.
chrome.contextMenus.onClicked.addListener((info, tab) => {
if (info.menuItemId === "vt") {
let searchUrl = "https://www.virustotal.com/gui/search/" + info.selectionText;
chrome.tabs.create({ url: searchUrl, index: tab.index + 1 });
}
});
This approach is significantly more efficient than copying and pasting. It keeps you in the flow of your investigation. If you are working on a red team engagement or a bug bounty, you can easily adapt this to pivot to internal tools, generate Jira tickets, or pass parameters into your Splunk dashboards. The goal is to reduce the "time to insight" for every indicator you encounter.
Why This Matters for Your Workflow
The real power of this approach is standardization. In a SOC, you want every analyst to follow the same process. If you have a specific way of triaging an alert, you can bake that process into an extension. When a new analyst joins the team, they do not need to learn a dozen different manual workflows; they just install the extension and follow the buttons.
This is also a massive win for knowledge transfer. Instead of maintaining a wiki page of "how to investigate X," you provide a tool that automates the investigation. It forces a consistent, repeatable process that is less prone to the "I forgot to check that" syndrome.
A Note on Security
While these extensions are powerful, they are also code running in your browser with access to the pages you visit. Always follow the principle of least privilege. Only request the permissions you absolutely need in your manifest.json. If you are building tools for your team, keep the code clean and review it for potential vulnerabilities, just as you would with any other piece of software.
If you are just getting started, do not let the JavaScript intimidate you. The official Chrome documentation is excellent, and there are thousands of open-source extensions on the Chrome Web Store that you can inspect to see how they handle DOM manipulation. Start small. Build a button that does one thing well, like a simple search pivot. Once you see how much time you save, you will find yourself looking for every other manual task you can automate. Stop clicking, start building, and reclaim the time you spend on the busy work.
Target Technologies
Up Next From This Conference
BSides Salt Lake City Conference Opening
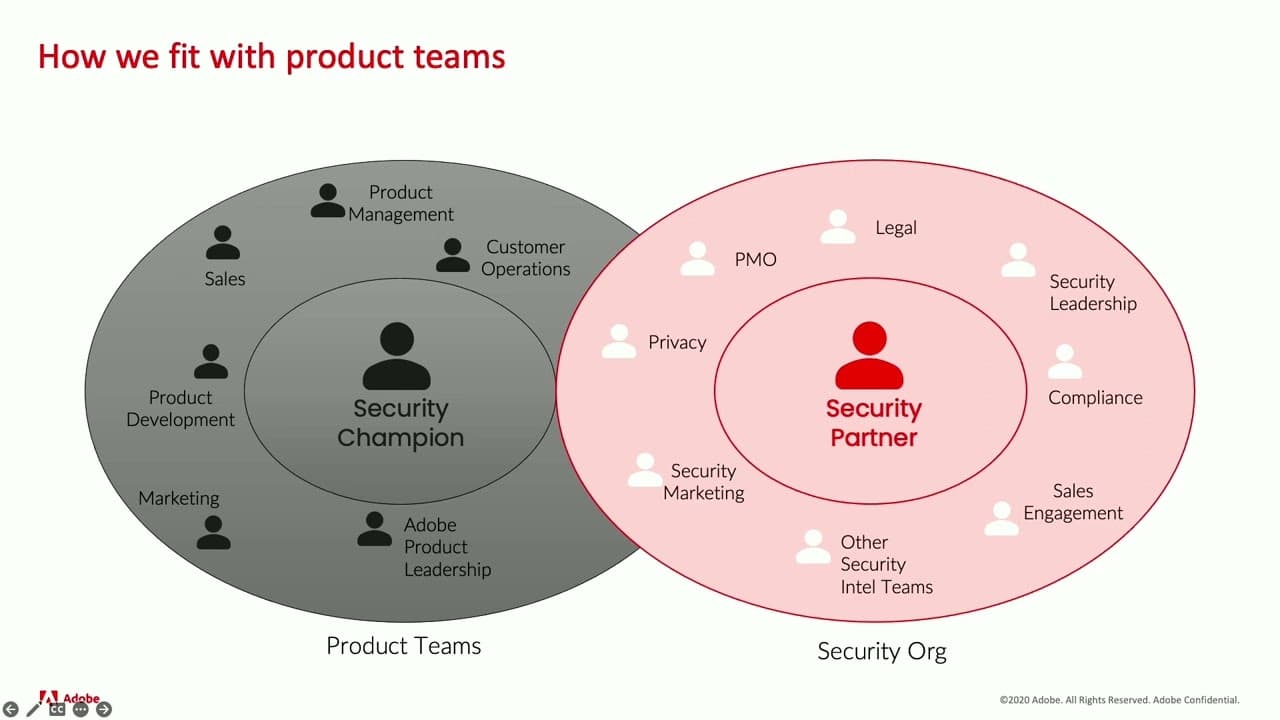
Building Stronger Relationships between Security and Engineering Teams
Why Data Breaches Aren't Like Plane Crashes, but Should Be
Similar Talks

Kill List: Hacking an Assassination Site on the Dark Web

Counter Deception: Defending Yourself in a World Full of Lies

