OSINT Signals Pop Quiz
This presentation demonstrates the application of Open Source Intelligence (OSINT) techniques to identify and interpret non-verbal signals in public imagery. It explores how visual cues, such as clothing, accessories, and physical positioning, can reveal organizational affiliations, personal status, and emotional states. The talk provides a practical framework for categorizing these signals into overt, organizational, secret, and covert levels to enhance reconnaissance efforts. The session concludes with an interactive quiz to test the audience's ability to extract actionable intelligence from various real-world scenarios.
Beyond the Screen: Decoding Human Signals in OSINT Reconnaissance
TLDR: Most OSINT practitioners focus on technical metadata, but physical signals in public imagery often provide higher-fidelity intelligence on organizational hierarchy and intent. By categorizing visual cues into overt, organizational, secret, and covert tiers, researchers can map human networks and operational status that digital footprints miss. This approach turns seemingly mundane photos into actionable reconnaissance data for social engineering and physical security assessments.
Reconnaissance is rarely just about scanning subdomains or scraping GitHub for leaked API keys. While we spend our days hunting for misconfigured S3 buckets or OWASP Top 10 vulnerabilities, the most critical intelligence often sits in plain sight, captured in the background of a social media post or a corporate event photo. The real-world risk isn't just a technical exploit; it is the human element that provides the context for those exploits to succeed. If you are not analyzing the physical signals in your target's environment, you are missing half the attack surface.
The Hierarchy of Visual Intelligence
Effective OSINT requires a structured way to process visual data. We can categorize these signals into four distinct tiers based on their visibility and intent. This framework allows a researcher to quickly triage an image and determine if it contains actionable intelligence or just noise.
- Overt: These are public-facing signals, such as branded t-shirts, company flags, or bumper stickers. They confirm presence and basic affiliation but rarely provide deep insight into internal operations.
- Organizational: This tier includes institutional markers like specific color schemes, logos, or group-specific gestures. These signals confirm membership within a specific sub-group or department.
- Secret: These signals are intentionally subtle, such as specific handshakes or the precise placement of insignias. They are designed to be recognized only by those with the appropriate clearance or social standing.
- Covert: These are the most valuable signals. They are non-verbal cues, such as the orientation of a ring or a specific accessory, that communicate status or intent to a pre-vetted audience without alerting the general public.
Decoding the Human Signal
The power of this technique lies in its ability to reveal information that is not explicitly stated. For example, consider the placement of a ring on a finger or a flower in one's hair. In many cultural contexts, these are not fashion choices; they are status indicators. If you are conducting a social engineering engagement, knowing whether a target is "taken" or "single" based on a ring's orientation on the left versus the right hand can drastically change your approach.
Similarly, physical objects like coins placed on a gravestone or specific types of footwear can signal a person's history or their current level of stress. A coin on a grave is a classic signal of a visit, but the denomination of the coin often indicates the nature of the relationship between the visitor and the deceased. These are not just anecdotes; they are data points that, when aggregated, build a profile of the target that is far more accurate than any automated tool could generate.
Practical Application for Pentesters
During a red team engagement, you are often looking for the path of least resistance. If you can identify a target's organizational affiliation or their current emotional state through their public photos, you can tailor your phishing lures or physical access attempts with surgical precision.
Imagine you are targeting a high-value individual. Instead of a generic spear-phishing email, you use the intelligence gained from their social media to reference a specific event they attended, mentioning a detail about the "organizational" signals they were displaying. This builds immediate rapport and trust. You are not just another attacker; you are someone who "belongs" in their world.
The Defensive Reality
Defending against this type of reconnaissance is notoriously difficult because it involves human behavior rather than technical misconfigurations. The primary defense is awareness. Organizations must train their employees to understand that their public-facing imagery is a source of intelligence for adversaries. This includes being mindful of what is visible in the background of photos, the insignias they wear, and the non-verbal signals they project in public spaces.
For those interested in the technical side of reconnaissance, it is worth reviewing the T1592-gather-victim-org-information and T1593-search-open-technical-databases techniques in the MITRE ATT&CK framework. While these focus on digital data, the principles of gathering and analyzing information remain the same. The next time you are performing recon, look past the code and the infrastructure. Look at the people. The most dangerous vulnerabilities are often the ones that don't require a single line of exploit code to trigger.
Start by auditing your own digital presence. Look at your photos from the last year and ask yourself what signals you are broadcasting. If you can decode your own life, you can decode your target's. The next step is to start building your own library of signals. Keep a log of the visual cues you encounter during your engagements and see if you can correlate them with the target's behavior. You will be surprised at how much information is hiding in plain sight.
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
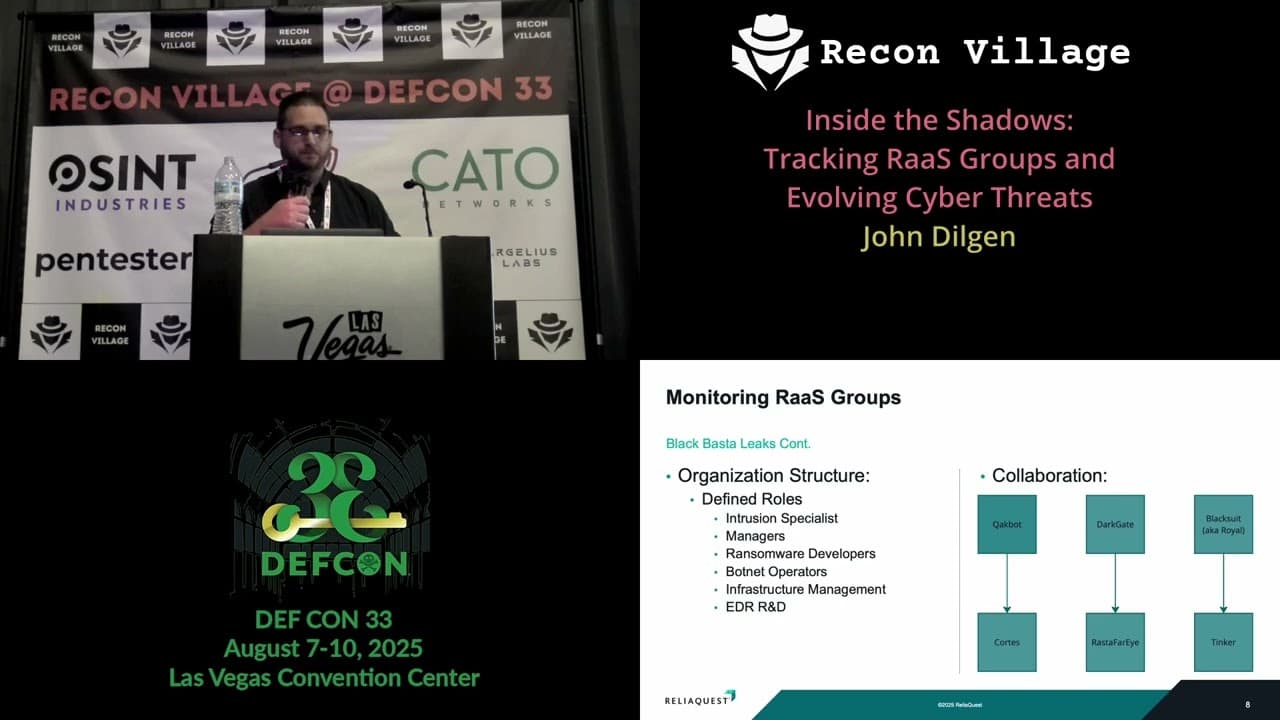
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web

