Stop Committing Your Secrets - Git Hooks To The Rescue
This talk demonstrates the use of Git hooks to prevent the accidental commitment of sensitive credentials, such as API keys and passwords, into source code repositories. It highlights the risks of hardcoded secrets in DevOps workflows and how they lead to significant data breaches in major organizations. The speaker provides a practical guide on implementing pre-commit and pre-receive hooks to automate the detection of these secrets before they are pushed to remote repositories. The presentation also compares several open-source tools for secret scanning and enforcement within the development lifecycle.
Why Your Git Hooks Are the Only Thing Standing Between Your Secrets and a Public Repo
TLDR: Hardcoded secrets in source code remain a top-tier vector for initial access, as evidenced by high-profile breaches at companies like Uber and Toyota. This post explores how to use Git hooks to automate secret detection at the pre-commit stage, effectively killing the risk before it leaves the developer's machine. By moving security checks to the local environment, you stop the bleeding before it hits the remote server.
Developers are not malicious, but they are often in a hurry. When a service needs an API key to function, the path of least resistance is to drop that key directly into a config file or a script and keep moving. We have all done it. The problem is that once that file is committed and pushed to a remote repository, the secret is effectively public. Even if you delete the file in a subsequent commit, the secret remains in the Git history forever.
The industry has spent years trying to solve this with post-push scanners, but that is reactive. By the time a scanner flags a leaked credential, an automated bot has likely already scraped it. The only way to win this game is to prevent the commit from happening in the first place.
The Mechanics of Local Enforcement
Git hooks are the most underutilized tool in the developer's security arsenal. Located in the .git/hooks directory of every repository, these scripts execute automatically in response to specific Git events. For a security researcher or a developer, the pre-commit hook is the holy grail. It runs after you type git commit but before the commit object is actually created. If the script exits with a non-zero status, the commit is aborted.
You can write these in any language, but shell scripts are the standard. The logic is straightforward: scan the staged files for patterns that look like secrets, and if you find a match, kill the process.
#!/bin/sh
# Simple pre-commit hook to block AWS keys
if git diff --cached | grep -qE 'AKIA[0-9A-Z]{16}'; then
echo "Error: AWS Access Key detected. Commit aborted."
exit 1
fi
This is a primitive example, but it illustrates the point. By placing this in your local .git/hooks/pre-commit file, you create a hard barrier. The developer gets immediate feedback, the secret never enters the local history, and it certainly never reaches the remote server.
Moving Beyond Regex
While a simple grep works for static patterns, it fails against the complexity of modern development. You need to account for false positives, different encoding schemes, and the sheer volume of secret types. This is where dedicated tools shine.
TruffleHog is the industry standard for this. It goes beyond simple regex by verifying the entropy of strings and, in many cases, checking if the discovered secret is actually active. Integrating it into a pre-commit workflow is trivial. Once you have the pre-commit framework installed, you simply add a configuration file to your repo.
repos:
- repo: https://github.com/trufflesecurity/trufflehog
rev: main
hooks:
- id: trufflehog
args: [--only-verified, --fail]
When a developer tries to commit, TruffleHog scans the staged changes. If it finds a valid, high-entropy secret, the commit fails. The developer is forced to move the secret to a secure store like HashiCorp Vault or Azure Key Vault before they can proceed.
The Pentester’s Perspective
If you are performing a red team engagement or a penetration test, your first step after gaining access to a developer's workstation or a CI/CD pipeline should be to check for these hooks. If they are missing, you have a massive opportunity.
Conversely, if you are building a security program, you cannot rely on developers to manually install these hooks. You need to enforce them at the organizational level. This is where tools like ggshield become powerful. It allows you to install hooks globally across all repositories on a machine, ensuring that even if a developer forgets to configure a specific project, the guardrails are still in place.
Why This Matters for OWASP A07:2021
We often talk about authentication failures in the context of broken login forms or weak password policies. However, the accidental exposure of credentials is a massive, often overlooked component of this category. When a developer commits a production API key to a public repo, they have effectively bypassed all authentication controls for that service.
The impact is rarely just a single compromised account. It is often a gateway to the entire cloud infrastructure. As Krebs on Security has documented repeatedly, the speed at which attackers weaponize these leaks is staggering.
Stop relying on your ability to catch leaks after they happen. Start building the friction into the development process. If you make it harder to commit a secret than it is to use a secrets manager, your developers will eventually choose the right path. The goal is to make the secure way the easiest way. If you are not using pre-commit hooks today, you are leaving the front door to your infrastructure wide open.
Vulnerability Classes
Attack Techniques
OWASP Categories
Up Next From This Conference
BSides Salt Lake City Conference Opening
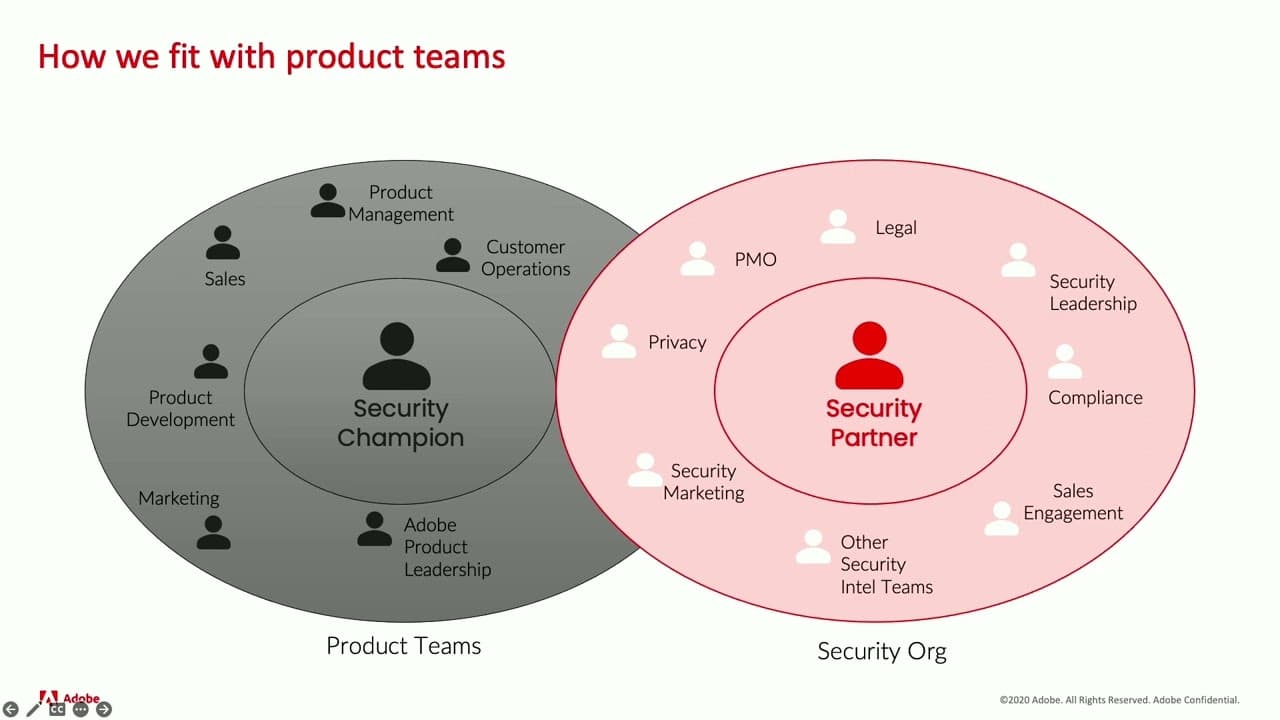
Building Stronger Relationships between Security and Engineering Teams
Why Data Breaches Aren't Like Plane Crashes, but Should Be
Similar Talks

Unmasking the Snitch Puck: The Creepy IoT Surveillance Tech in the School Bathroom

Exploiting Shadow Data in AI Models and Embeddings

