From Dare to Discovery: How OSINT and Modern Recon Techniques Uncovered a Global VPN Infrastructure
This talk demonstrates a multi-stage attack chain involving OSINT, SMB enumeration, and kernel-level exploitation to achieve remote code execution and local privilege escalation on VPN infrastructure. The researcher details the exploitation of a stack overflow vulnerability in the TAP driver and the abuse of named pipes to impersonate users and load malicious plugins. The presentation highlights how cloud-based GPU cracking can be leveraged to accelerate the exploitation of weak credentials found during reconnaissance. A full exploit chain is showcased, moving from initial access to system-level compromise.
From OSINT to Kernel: Exploiting Global VPN Infrastructure via Named Pipes
TLDR: This research details a multi-stage attack chain that leverages OSINT to identify vulnerable VPN deployments, followed by SMB enumeration and kernel-level exploitation to achieve remote code execution. By exploiting a stack overflow in the TAP driver and abusing named pipes for user impersonation, an attacker can escalate privileges from a low-privileged user to system-level access. Pentesters should prioritize auditing named pipe permissions and monitoring for suspicious plugin loading behaviors in VPN client configurations.
Security researchers often treat VPN clients as black boxes, assuming the tunnel is secure simply because the traffic is encrypted. This assumption is dangerous. Recent analysis of global VPN infrastructure reveals that the attack surface is not limited to the encrypted tunnel itself, but extends deep into the host operating system through the drivers and services required to maintain that connection. When an attacker can move from a simple OSINT-based reconnaissance phase to kernel-level code execution, the entire premise of "secure remote access" collapses.
Reconnaissance and Initial Access
The research begins with a classic OSINT approach. Using tools like Shodan and ZoomEye, an attacker can identify exposed VPN gateways or internal services that rely on common VPN client software. Once a target is identified, the goal shifts to gaining a foothold. In many enterprise environments, this involves exploiting weak credentials or misconfigured services.
Once inside, the focus turns to the VPN client's local footprint. The researcher identified that many VPN clients, including those using the TAP-Windows6 driver, expose interfaces that can be manipulated. By performing SMB enumeration, an attacker can often identify shared resources or misconfigured named pipes that allow for inter-process communication (IPC). This is where the research gets interesting.
Exploiting the TAP Driver and Named Pipes
The core of this exploit chain relies on a stack overflow vulnerability within the TAP driver. The driver is responsible for handling network packets, and by sending a specially crafted buffer, an attacker can trigger an integer overflow that leads to a stack-based buffer overflow.
// Simplified representation of the vulnerable buffer allocation
// The driver allocates data length plus 24 bytes for the header
// A large value here triggers the overflow
NTSTATUS MiniportSendNetBufferLists(PNDIS_MINIPORT_ADAPTER_CONTEXT Adapter, ...) {
// ...
ULONG dataLength = GetNetBufferLength(NetBuffer);
PVOID buffer = ExAllocatePoolWithTag(NonPagedPool, dataLength + 24, 'paT');
// ...
}
While triggering the overflow is the first step, achieving reliable code execution requires bypassing modern kernel protections. The researcher demonstrated that by abusing named pipes, an attacker can impersonate a higher-privileged user. By creating a malicious named pipe that mimics the expected communication channel of the VPN service, the attacker can intercept requests and inject malicious payloads.
This technique is particularly effective because it leverages the trust relationship between the user-mode VPN service and the kernel-mode driver. When the service attempts to communicate with the driver, it inadvertently interacts with the attacker-controlled pipe, allowing for the loading of malicious plugins or the execution of arbitrary code with system privileges. This is a clear example of Broken Access Control where the IPC mechanism lacks proper authentication.
Accelerating Exploitation with Cloud GPUs
One of the most compelling aspects of this research is the use of cloud-based GPU cracking to accelerate the exploitation phase. Once an attacker has captured NTLM hashes through SMB relay or other credential harvesting techniques, the time-to-crack is the only barrier to full system compromise.
The researcher utilized vast.ai to rent high-performance GPU instances, specifically targeting configurations with multiple NVIDIA RTX 4090 cards. Using Hashcat, they were able to crack complex passwords in minutes rather than days. This demonstrates that the "cost" of cracking credentials has dropped significantly, making it a viable step even for mid-tier attackers. For a pentester, this means that if you can capture a hash, you should assume it will be cracked almost immediately.
Defensive Considerations
Defending against this class of attack requires a multi-layered approach. First, organizations must enforce strict access control lists (ACLs) on all named pipes. By default, many services allow too much access, which is exactly what this exploit relies on. Second, ensure that all VPN client software is patched against known vulnerabilities, such as CVE-2024-21338, which highlights the risks of improper kernel-mode driver handling.
Finally, implement robust monitoring for suspicious process creation. If a VPN client service suddenly spawns a child process that it doesn't normally interact with, or if it attempts to load a DLL from an unusual location, this should trigger an immediate alert. The "Bring Your Own Vulnerable Driver" (BYOVD) technique is becoming increasingly common, and defenders must be vigilant about the drivers loaded in their environment.
This research serves as a stark reminder that the security of a remote access solution is only as strong as the weakest component in its stack. Whether it is a driver vulnerability or an insecure IPC mechanism, the path to system compromise is often shorter than we think. As researchers, we must continue to pull at these threads, because the attackers are certainly doing the same.
Vulnerability Classes
Target Technologies
Attack Techniques
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
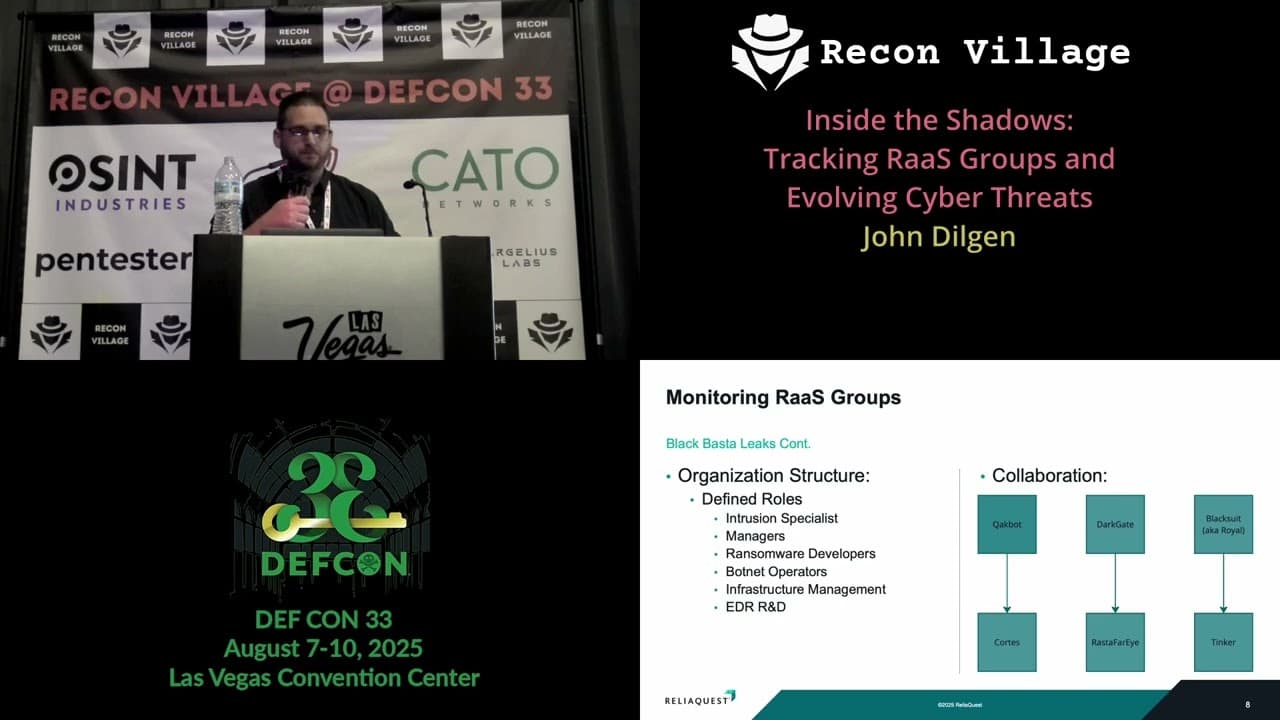
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web

