Plumbing The Plumber: A Playbook For Integration Servers
This talk demonstrates a methodology for identifying and exploiting misconfigured webMethods Integration Servers, a common middleware used in large corporate environments. The researchers show how to use OSINT tools and CT log scanning to find these servers and exploit common flaws like default credentials and unauthenticated access to administrative services. A key finding is the prevalence of misconfigured ACLs in the WmPublic package, allowing attackers to execute OS commands or shut down servers remotely. The speakers released a tool called Integration_Surfer to automate the discovery and testing of these integration hubs.
Exploiting Unauthenticated Administrative Services in webMethods Integration Servers
TLDR: Researchers at DEF CON 2025 revealed that thousands of webMethods Integration Servers are exposed to the internet with default credentials and misconfigured access controls. By targeting the
WmPublicpackage, attackers can achieve remote command execution or perform unauthorized administrative actions. Pentesters should prioritize scanning for these endpoints and testing for default credentials, as this remains a high-impact, low-effort vector in large corporate environments.
Integration servers are the silent, often neglected plumbing of the enterprise. They sit between legacy mainframes and modern cloud applications, moving data that keeps businesses running. When these servers are misconfigured, they become a goldmine for anyone performing external reconnaissance. The recent research presented at DEF CON 2025 highlights a critical reality: thousands of these middleware instances are not only exposed to the public internet but are also running with default configurations that allow for trivial exploitation.
The Mechanics of the Vulnerability
The core issue lies in how these servers handle administrative access. Many deployments of Software AG webMethods rely on the WmPublic package, which provides a suite of services for integration tasks. Crucially, these services are often left accessible without proper authentication.
During the research, it became clear that the default security posture for many of these installations is effectively non-existent. Attackers can use search engines like Shodan, FOFA, Censys, or ZoomEye to identify these servers by querying for specific service signatures. Once a target is identified, the barrier to entry is remarkably low.
The most dangerous aspect of this misconfiguration is the ability to invoke administrative services directly. For instance, the pub.utils:executeOSCommand service is a frequent target. If an attacker can reach this endpoint, they can execute arbitrary commands on the underlying host. This falls squarely under OWASP A03:2021-Injection, as the server fails to validate the source or intent of the request.
Automating Discovery and Exploitation
To streamline the identification of these vulnerable instances, the researchers released Integration_Surfer. This tool automates the process of taking a list of IP addresses or domains, identifying the integration server, and testing for default credentials.
For a pentester, the workflow is straightforward. You identify the target, verify the presence of the WmPublic package, and attempt to access sensitive endpoints. If the server is misconfigured, you might encounter a response that confirms the service is active and reachable. The following command structure is typical for interacting with these services:
# Example of invoking a service via a GET request
curl -u "Administrator:manage" "http://target-server:5555/invoke/pub.utils:executeOSCommand?command=whoami"
The impact of this cannot be overstated. In many cases, the service account running the integration server has elevated privileges on the host operating system. A successful exploit grants the attacker a foothold within the internal network, often bypassing perimeter defenses that focus on more modern, hardened applications.
Real-World Exposure and Risk
During the research, the team identified thousands of exposed servers belonging to major global corporations. The lack of basic security hygiene—such as changing default passwords or restricting access to the administrative interface—is the primary driver of this risk.
When conducting an engagement, you should look for the default port 5555. If you find a webMethods login page, the first step is always to test common default credentials. If those fail, look for unauthenticated access to the invoke directory. Even if you cannot immediately execute commands, the ability to list services or read configuration files often provides enough information to pivot deeper into the environment.
The researchers also demonstrated the use of Gungnir, a tool for monitoring Certificate Transparency (CT) logs. By tracking new certificates issued for specific domains, you can identify new integration servers as they are deployed, often before they are fully hardened. This proactive approach to reconnaissance ensures that you are not just finding the low-hanging fruit, but also the newly planted, vulnerable infrastructure.
Defensive Hardening
Defending against this is a matter of basic configuration management. First, ensure that the administrative interface is never exposed to the public internet. If remote access is required, it must be gated behind a VPN or a robust identity-aware proxy. Second, audit the WmPublic package and disable any services that are not strictly necessary for business operations. Finally, enforce a strict password policy for all service accounts, especially the default Administrator account.
Integration servers are often treated as "set and forget" infrastructure, but their role in the data flow makes them a high-value target. If you are performing an assessment, do not overlook these systems. They are frequently the path of least resistance into the heart of a corporate network. The tools are available, the vulnerabilities are well-documented, and the risk is immediate. It is time to start looking at the plumbing.
Vulnerability Classes
Target Technologies
Attack Techniques
OWASP Categories
All Tags
Up Next From This Conference

Plumbing The Plumber: A Playbook For Integration Servers

Mapping the Shadow War: From Estonia to Ukraine
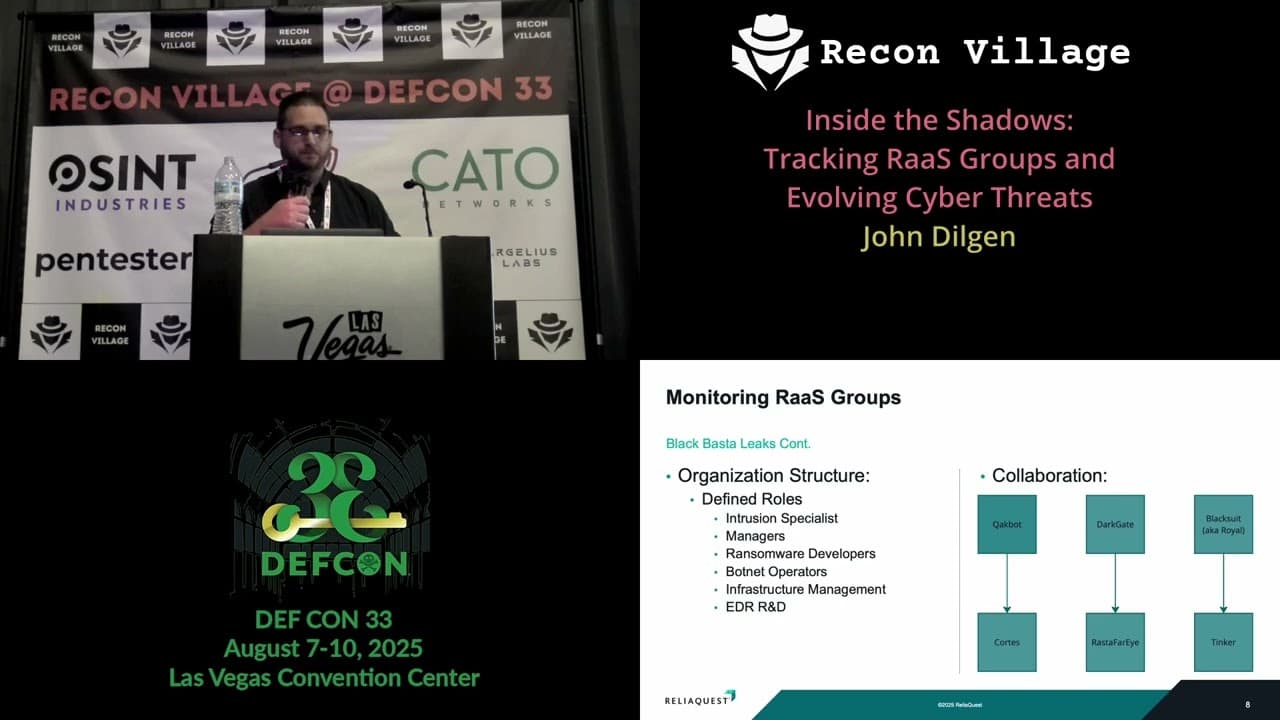
Inside the Shadows: Tracking RaaS Groups and Evolving Cyber Threats
Similar Talks

Kill List: Hacking an Assassination Site on the Dark Web

Unmasking the Snitch Puck: The Creepy IoT Surveillance Tech in the School Bathroom

