BSides Salt Lake City 2025 Opening Ceremony
This video is an opening ceremony for the BSides Salt Lake City 2025 conference. It provides logistical information, including venue maps, track locations, and details on conference activities such as the CTF, lockpicking, and resume review workshops. The talk also highlights sponsors and upcoming cybersecurity events in the Utah region.
Beyond the Badge: Why Community-Driven Research Still Beats Corporate Whitepapers
TLDR: The BSides Salt Lake City 2025 opening ceremony highlights the critical role of community-led events in fostering genuine technical collaboration. By focusing on hands-on workshops like circuit assembly and interactive CTF challenges, the event prioritizes practical skill-building over vendor-driven marketing. For researchers and pentesters, these local gatherings remain the most effective way to pressure-test new techniques and build the professional networks that actually lead to zero-day discoveries.
Security research often feels like a race to see who can publish the most polished, buzzword-heavy whitepaper first. We spend our days buried in automated scanner output, chasing low-hanging fruit, and occasionally getting lucky with a bug bounty. But the real breakthroughs—the ones that actually change how we approach an engagement—rarely come from a vendor’s marketing deck. They come from the hallway track, the late-night soldering sessions, and the raw, unfiltered exchange of ideas that happens at community-driven events like BSides Salt Lake City.
The Value of Hands-On Technical Exchange
The most effective way to sharpen your offensive skills is to stop reading about exploits and start building the hardware or software that makes them possible. This year’s BSides SLC emphasizes this through its focus on interactive environments. When you spend an afternoon at a circuit assembly workshop, you aren't just learning to solder; you are gaining a fundamental understanding of how embedded systems communicate.
Understanding the physical layer is a massive force multiplier for any pentester. If you can identify a debug port on a piece of hardware, you’ve already bypassed the primary authentication layer that most developers assume is impenetrable. The event’s focus on tools like the Flipper Zero and Meshtastic isn't just for show. These tools allow researchers to experiment with radio frequency (RF) protocols and mesh networking in a controlled, collaborative environment. When you see a peer demonstrate a successful replay attack on a sub-GHz signal, the theory behind the vulnerability suddenly becomes a practical, repeatable technique you can apply to your next physical security assessment.
Moving Beyond the Scanner
Automated tools are necessary for scale, but they are blind to logic flaws and complex, multi-stage attack chains. The Capture The Flag (CTF) competition at this year’s event is designed to force participants out of their comfort zones. By moving away from standard web-app vulnerabilities and into custom-built challenges, the organizers are pushing researchers to think like an adversary who has already gained initial access.
For a pentester, the value of a well-constructed CTF is the ability to practice lateral movement and privilege escalation without the constraints of a client’s production environment. If you find yourself stuck on a challenge, you aren't just reading a write-up; you are talking to the person who wrote the challenge. That direct feedback loop is the fastest way to learn. It’s the difference between knowing that a Server-Side Request Forgery (SSRF) exists and understanding how to chain it with a misconfigured cloud metadata service to dump environment variables.
Building Your Professional Network
The most overlooked aspect of these conferences is the career development component. Whether it’s the resume review workshops or the informal conversations with hiring managers, these events provide a unique opportunity to bypass the traditional, broken HR screening process. If you can demonstrate your technical competence by solving a complex challenge or contributing to a community project, you are already ahead of 90% of the applicants who only have a list of certifications on their resume.
The Utah Cybersecurity Society and the broader community behind these events are doing more than just putting on a show. They are creating a pipeline for talent that values curiosity and hands-on experience over corporate pedigree. When you are on an engagement and hit a wall, the ability to reach out to someone you met at a local BSides event—someone you know is a subject matter expert—is often the difference between a successful compromise and a failed assessment.
What to Do Next
If you are a researcher or a pentester, stop treating these events as optional. The next time you see a local BSides, a SaintCon, or a Hacker Camp on the calendar, make the effort to attend. Don't just show up for the talks. Get involved in the workshops, participate in the CTF, and actually talk to the people sitting next to you.
The industry is moving toward more complex, distributed systems, and the only way to keep up is to maintain a network of peers who are actively breaking things. If you have a technique you’ve been working on, submit a talk for the next Call for Papers (CFP). Even if you don't think your research is "ready," the process of preparing a presentation will force you to document your findings and identify the gaps in your own methodology. The community is only as strong as the knowledge we share, so start contributing.
Tools Used
Up Next From This Conference
Similar Talks
Making and Breaking NSA's Codebreaker Challenge
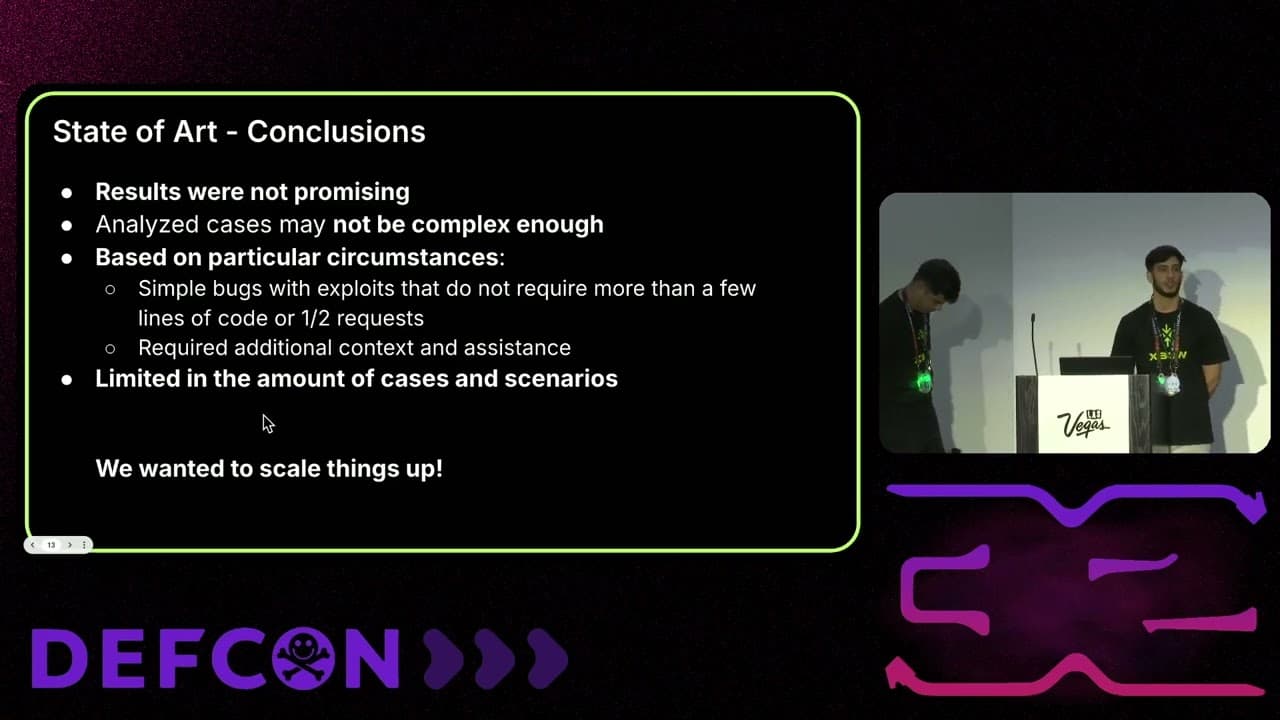
Leveraging AI for Smarter Bug Bounties




