Designing and Debugging Custom Conference Badges
This talk details the hardware design, assembly, and software development process for a custom conference badge based on the Raspberry Pi Pico. The presenters discuss the integration of various I2C-based modules, including an accelerometer, joystick, and LED array, and the use of CircuitPython for rapid prototyping. The session highlights common hardware debugging challenges, such as trace routing errors and power-on initialization issues, and provides practical solutions for field repairs. The talk concludes with a demonstration of custom firmware modifications and the use of the badge's serial REPL for interactive development.
Hardware Debugging: Lessons from a Broken Conference Badge
TLDR: This post breaks down the hardware design and field-repair process for a custom conference badge built on the Raspberry Pi Pico. It highlights how common design oversights, such as incorrect trace routing and power-on initialization failures, can turn a simple project into a debugging nightmare. Pentesters and hardware hackers can learn from these real-world mistakes to improve their own custom tool development and field-testing workflows.
Hardware hacking often feels like a black box until you are staring at a PCB under a microscope, wondering why your trace isn't conducting. Most security researchers focus on software vulnerabilities, but when you build your own tools, the physical layer becomes your primary attack surface. The recent talk on designing and debugging custom conference badges at BSides Salt Lake City 2022 provides a masterclass in the realities of hardware development. It is a reminder that even simple projects, when scaled for a conference, expose the fragility of custom hardware designs.
The Reality of Rapid Prototyping
When you are building custom hardware, the gap between a CAD render and a functional board is often filled with manual labor and last-minute fixes. The badge in question utilized a Raspberry Pi Pico as the core processor, leveraging its dual-core ARM Cortex-M0+ architecture. The design integrated several I2C-based modules, including an accelerometer, a joystick, and an LED array.
The primary lesson here is that prototyping is not just about getting the circuit to work once; it is about ensuring the design is resilient enough to survive the assembly process. The developers used KiCad for the board design but skipped the critical step of creating a final, fully-populated prototype before sending the design to the shop. This led to a critical design flaw: the ground pin for the joystick button was routed incorrectly.
Debugging Physical Layer Failures
When the badges arrived, the team discovered that the joystick button was not functioning as expected. The fix required a "bodge"—a common term for a manual, often messy, hardware modification. They had to cut a trace on the front of the board and solder a jumper wire from an IC pin to the button pad.
This is a scenario every hardware hacker encounters. When you are on an engagement and your custom implant or tool fails, you do not have the luxury of a re-spin. You have to understand the schematic, identify the physical break, and perform a field repair. The team’s approach to this was systematic: they identified the trace, used a scalpel to cut it, and then used a heat gun to reflow the solder for the jumper wire.
The second, more insidious issue was a power-on initialization failure. Some badges would simply refuse to boot. After significant troubleshooting, they realized the flash chip was not initializing correctly because it needed a few extra microseconds of power-on time. The solution was a firmware update that increased the initialization delay. This highlights a critical point for anyone developing custom security hardware: timing is everything. If your firmware assumes a stable power state that the hardware cannot provide, your tool will be unreliable.
Leveraging the REPL for Field Testing
One of the most powerful features of using CircuitPython for this project was the ability to interact with the hardware directly through a serial terminal. By connecting the badge to a computer via USB-C, the device mounts as a standard file system. This allows for rapid code iteration—you simply edit code.py, save it, and the device reboots with the new logic.
For a pentester, this is invaluable. If you are in the field and need to modify the behavior of your tool, you do not need a full development environment. You just need a terminal emulator like PuTTY or the screen command:
screen /dev/tty.usbmodem14101 115200
Once connected to the REPL, you can issue commands to test individual components, such as toggling a GPIO pin to verify an LED connection or reading raw data from an I2C sensor. This level of interactivity turns the hardware into a programmable platform, allowing you to debug and refine your tools in real-time.
The Defensive Perspective
From a defensive standpoint, the lessons here are about supply chain security and hardware integrity. If you are deploying custom hardware in a sensitive environment, you must account for the possibility of design flaws or malicious modifications. A "bodge" wire on a board is a red flag. If you find hardware that has been manually altered, you should treat it as compromised.
Furthermore, the initialization issue serves as a reminder that firmware security is not just about the code; it is about the interaction between the code and the physical hardware. A vulnerability that allows an attacker to manipulate the power-on sequence or the bootloader can lead to persistent, low-level access that is nearly impossible to detect with standard software-based security tools.
Hardware hacking is an iterative process. You will make mistakes, you will have to perform field repairs, and you will learn more from a broken board than a working one. The next time you are building a custom tool, do not just focus on the software. Spend the time to understand the physical constraints of your design, and always have a plan for when the hardware inevitably fails. If you are interested in the specific firmware used for this project, the source code is available on GitHub. Dig into it, break it, and see what you can build next.
Vulnerability Classes
Tools Used
Target Technologies
Up Next From This Conference
BSides Salt Lake City Conference Opening
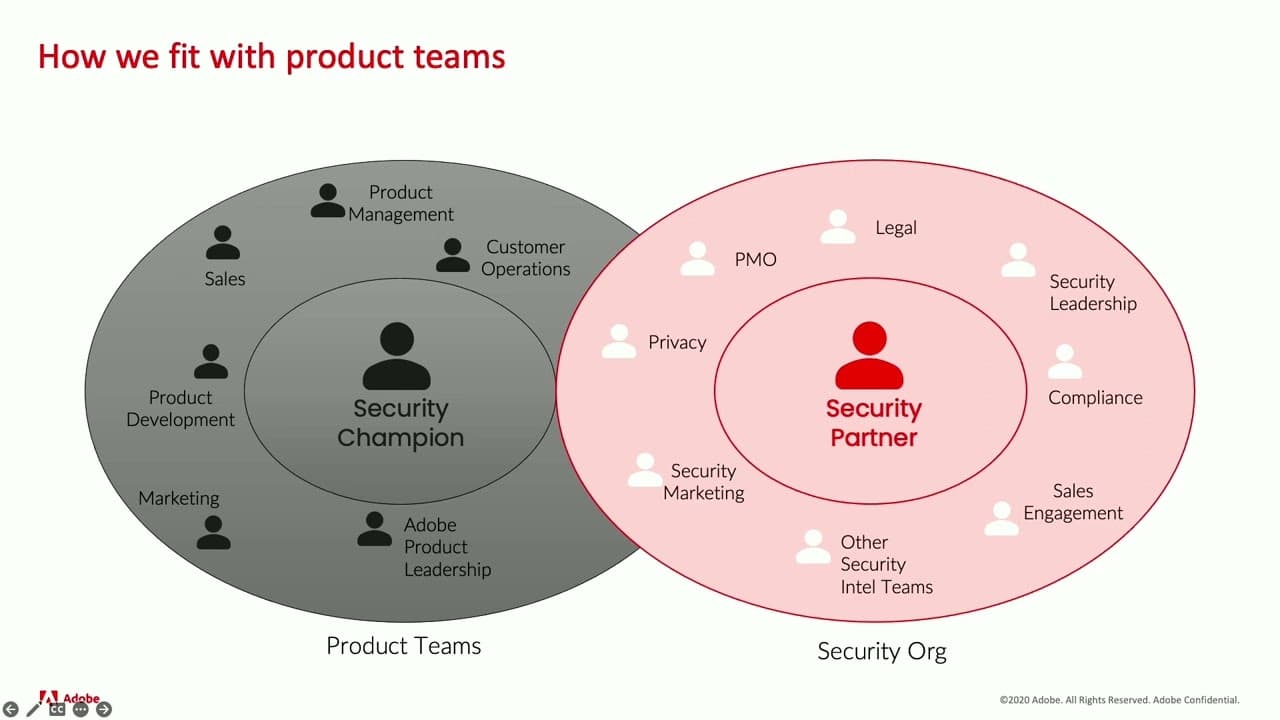
Building Stronger Relationships between Security and Engineering Teams
Why Data Breaches Aren't Like Plane Crashes, but Should Be
Similar Talks

Hacking Apple's USB-C Port Controller

Unmasking the Snitch Puck: The Creepy IoT Surveillance Tech in the School Bathroom

