Opening Remarks
This video contains the opening remarks for the BSides San Francisco 2025 conference. It provides logistical information regarding the event schedule, venue layout, and community resources. It is a non-technical administrative presentation and does not contain any security research or vulnerability demonstrations.
The Reality of Community-Driven Security Research at BSides
TLDR: Security conferences like BSides San Francisco 2025 serve as critical hubs for peer-to-peer knowledge exchange, moving beyond vendor-led marketing to focus on practical, hands-on research. These events provide the necessary space for researchers to pressure-test new techniques and discuss the evolving threat landscape in an open, collaborative environment. Engaging with these communities is essential for any practitioner looking to stay ahead of emerging attack vectors and refine their offensive methodology.
Security research thrives on the friction between established defenses and the relentless ingenuity of the offensive community. While high-level industry summits often prioritize product announcements and corporate narratives, grassroots events like Security BSides remain the primary venue for the raw, unfiltered exchange of technical knowledge. The value of these gatherings lies not in the keynote presentations, but in the hallway conversations and village workshops where researchers dissect the latest bypasses and exploit chains.
Why Localized Research Matters
The current security climate demands a shift from static, compliance-based testing toward dynamic, threat-informed operations. When a researcher identifies a novel way to chain low-severity bugs into a full remote code execution, they rarely document it in a white paper first. They bring it to a community event. This is where the "noise" is filtered out. If a technique is impractical or relies on an unrealistic set of prerequisites, the community will identify those limitations within minutes of a presentation.
For a pentester or bug bounty hunter, this environment is the most efficient way to calibrate your skills. You are not just learning about a new OWASP Top 10 vulnerability; you are learning how that vulnerability manifests in modern, containerized, or cloud-native architectures. The ability to distinguish between a theoretical proof-of-concept and a weaponizable exploit is what separates a junior researcher from a senior red teamer.
The Evolution of Attack Surfaces
Modern applications are increasingly complex, often relying on a sprawling web of microservices, third-party APIs, and serverless functions. This complexity has fundamentally changed the nature of our work. We are no longer just looking for simple cross-site scripting or SQL injection. We are looking for logic flaws in authentication flows, insecure deserialization in message queues, and misconfigurations in infrastructure-as-code.
Consider the recent surge in supply chain attacks. These are not typically the result of a single, massive vulnerability. They are the result of small, incremental failures in the development lifecycle. When you attend a talk on these topics, you are not just seeing a demo; you are seeing a blueprint for how to audit your own targets. You are learning how to map out an environment, identify the trust boundaries, and determine where the weakest links reside.
Practical Engagement for the Modern Researcher
If you are a bug bounty hunter, your success depends on your ability to find the "uncommon" path. Most automated scanners will find the low-hanging fruit. The high-impact, high-bounty findings come from manual analysis and a deep understanding of how the underlying technology stack is configured. This is why participating in events like BSides is so vital. You need to be in the room when someone explains how they bypassed a specific Web Application Firewall (WAF) or how they leveraged a CVE to gain initial access to a target.
These interactions provide context that you simply cannot get from reading a vulnerability report. You learn about the "gotchas" that the researcher encountered, the specific versions of the software that were vulnerable, and the defensive measures that were in place. This is the kind of information that allows you to build your own custom tooling and refine your reconnaissance process.
Building a Sustainable Security Practice
Defenders are not standing still. They are deploying more sophisticated detection and response capabilities, from EDR solutions to automated threat hunting. As an offensive practitioner, you must constantly evolve your tactics to remain effective. This means moving beyond standard payloads and focusing on living-off-the-land techniques that are harder to detect.
The most effective way to do this is to maintain a tight feedback loop with your peers. When you see a new technique discussed at a conference, your first step should be to attempt to reproduce it in a controlled lab environment. Use tools like Metasploit or Burp Suite to test the boundaries of the vulnerability. Document your findings, identify the limitations, and share your results with your team.
Moving Forward
The next time you are evaluating a conference to attend, look past the vendor booths and the keynote speakers. Look for the events that prioritize technical depth and community engagement. Look for the workshops where you can get your hands on the latest tools and techniques. The security landscape is not going to get any simpler. The only way to stay relevant is to keep learning, keep testing, and keep sharing.
Your next big finding is likely hidden in the details of a system you think you already understand. Challenge your assumptions, test your hypotheses, and never stop digging. The community is here to help you refine your craft, but the heavy lifting is up to you. Start by identifying one area of your methodology that you want to improve, find the relevant research, and start building your own test cases today.
Up Next From This Conference
Similar Talks
Making and Breaking NSA's Codebreaker Challenge
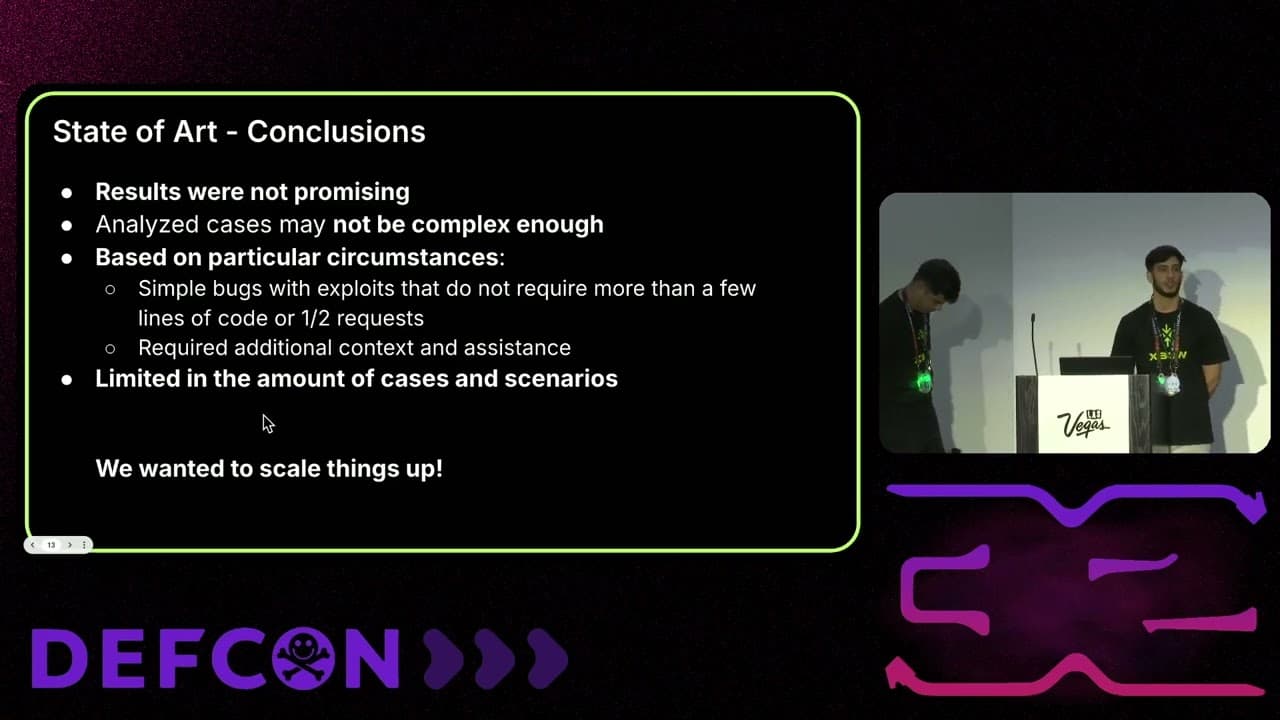
Leveraging AI for Smarter Bug Bounties




