Ransomware Rebranding
This talk analyzes the tactical phenomenon of ransomware groups rebranding to evade law enforcement and security researchers. It examines the lifecycle of several prominent ransomware strains, including Maze, Sekhmet, Egregor, DarkSide, BlackMatter, and BlackCat, to identify patterns in their operational shifts. The presentation highlights how these groups use rebranding to maintain business continuity, manage public perception, and circumvent international sanctions. The speaker emphasizes the importance of tracking these rebrands to improve threat intelligence, incident response, and the attribution of malicious activity.
Tracking Ransomware Rebrands: Why Your Attribution Data Is Likely Wrong
TLDR: Ransomware groups frequently rebrand to evade law enforcement, bypass sanctions, and reset their public reputation. By analyzing code overlaps, infrastructure reuse, and payment patterns, researchers can often link these new entities to their predecessors. Pentesters and threat hunters must look past the marketing and focus on TTPs to accurately assess the risk of a specific threat actor.
Ransomware is not a static threat. It is a business, and like any business, it pivots when the market conditions become hostile. When law enforcement agencies like the FBI or Europol turn up the heat, or when a group’s brand becomes so toxic that victims refuse to pay, these actors do not simply retire. They rebrand. They change their name, update their ransom notes, and occasionally tweak their malware, but the underlying infrastructure and operational habits often remain identical.
For a researcher or a pentester, failing to recognize a rebrand is a critical error. If you are treating a "new" group as a novel threat, you are ignoring years of intelligence on their TTPs, their preferred initial access vectors, and their negotiation tactics.
The Mechanics of a Rebrand
Rebranding is rarely a clean break. It is an attempt to create an illusion of novelty. A group might change its name from Maze to Egregor, or from DarkSide to BlackMatter, but the core code—the encryption routines, the obfuscation techniques, and the command-and-control (C2) infrastructure—often shows clear lineage.
The most effective way to track these shifts is by focusing on the "DNA" of the operation. This includes:
- Code Similarity: Look for shared functions, identical obfuscation patterns, or reused strings in the binary. Even if the group claims to have written a new payload from scratch, they rarely do.
- Infrastructure Reuse: Check for overlapping IP addresses, domain registration patterns, or hosting providers.
- Payment Portals: The infrastructure used to manage ransom negotiations is expensive and complex to build. Groups often reuse these portals, sometimes even keeping the same backend logic.
For example, the transition from DarkSide to BlackMatter was heavily scrutinized by the research community. While the group publicly denied the connection, the technical evidence—specifically the use of the Salsa20 stream cipher implementation and similar C2 communication protocols—made it clear that the same developers were behind both operations.
Why Attribution Matters for Pentesters
When you are performing a red team engagement or a penetration test, you are not just testing a network against a generic threat. You are testing it against the specific TTPs that are likely to be used by the adversaries targeting that industry. If you are testing a healthcare organization, you need to know if the group targeting them is known for exploiting CVE-2021-44228 or if they prefer spear-phishing with malicious macros.
If you misattribute a threat actor because you fell for their rebrand, your testing will be misaligned. You might focus on patching vulnerabilities that the "new" group doesn't even care about, while leaving the actual attack vectors wide open.
The Danger of Unwitting Complicity
One of the most dangerous aspects of this landscape is how easily researchers and the press can become unwitting accomplices in a rebrand. When a group announces they are "shutting down" and "reorganizing," they are often just trying to clear the air. If the security community takes these announcements at face value and declares the group dead, we are doing the attackers' work for them.
We have seen this repeatedly. A group claims to be closing shop, and a few months later, a "new" group appears with a similar modus operandi. If we don't maintain a rigorous, evidence-based tracking system, we lose the ability to hold these individuals accountable.
Defensive Strategies
Defenders should focus on MITRE ATT&CK mapping rather than just IOCs. IP addresses and domain names are ephemeral; they change the moment a group decides to rebrand. TTPs, however, are much harder to change. A group that relies on specific lateral movement techniques or privilege escalation paths will likely continue to use them, regardless of what they call themselves.
Focus your monitoring on the behaviors that are difficult for an attacker to alter. If you see a new ransomware strain that exhibits the same file-system interaction patterns as a known actor, treat it as a high-confidence match, regardless of the marketing on their new leak site.
What to Do Next
Stop relying on the names provided by the threat actors themselves. When you encounter a new ransomware strain, perform a deep dive into the binary. Look for the shared libraries, the specific API call sequences, and the way the malware interacts with Active Directory.
If you are a researcher, share your findings on code overlaps. If you are a pentester, use this intelligence to build more realistic attack scenarios. The ransomware actors are working together, sharing code, and refining their business models. We need to be just as collaborative in our research and just as disciplined in our analysis. The next time a group claims to be "shutting down," don't look for their exit interview—look for their next iteration.
Vulnerability Classes
Target Technologies
Attack Techniques
All Tags
Up Next From This Conference
BSides Salt Lake City Conference Opening
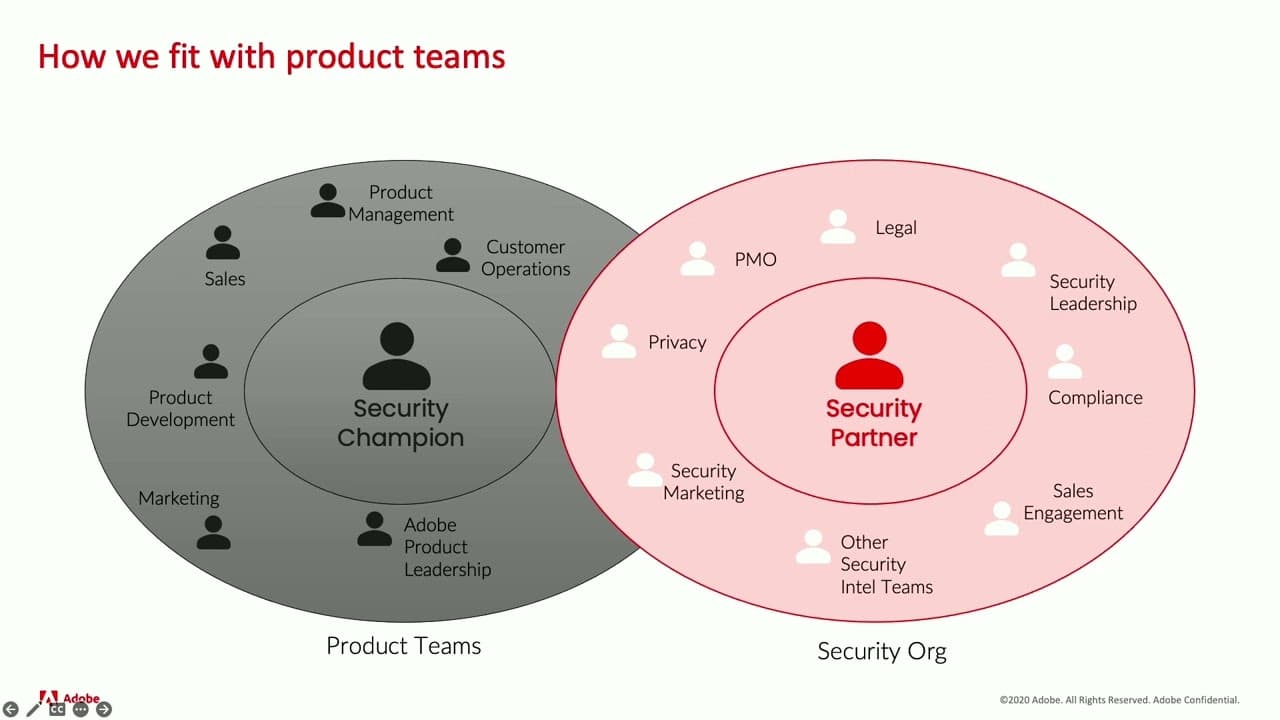
Building Stronger Relationships between Security and Engineering Teams
Why Data Breaches Aren't Like Plane Crashes, but Should Be
Similar Talks

Inside the FBI's Secret Encrypted Phone Company 'Anom'

Kill List: Hacking an Assassination Site on the Dark Web

