BSidesSLC Closing Ceremony
This video is a non-technical closing ceremony for the BSidesSLC conference. It covers event logistics, sponsor acknowledgments, and the distribution of prizes for various contests held during the event. No technical vulnerabilities, tools, or offensive security research are presented.
Why Community-Driven Security Events Are Your Best R&D Lab
TLDR: Security conferences like BSides are often dismissed as networking fluff, but they are actually the most effective environments for stress-testing new hardware and collaborative research. The recent BSidesSLC closing ceremony highlighted how custom electronic badges and Capture The Flag (CTF) competitions serve as real-world proving grounds for hardware hacking and team-based exploitation. Pentesters who ignore these community-led challenges miss out on the chance to refine their skills in a low-stakes, high-innovation environment.
Professional security research often feels like a solitary grind. You spend weeks staring at Burp Suite, hunting for Insecure Deserialization or trying to bypass a WAF. When you finally hit a wall, you turn to documentation or stale forums. But the most significant breakthroughs in offensive security rarely happen in isolation. They happen when you put a piece of hardware in the hands of a dozen people who are incentivized to break it.
The closing ceremony at BSidesSLC 2022 served as a reminder that the most valuable "research" often happens on the conference floor, not in the keynote hall. While the event was a wrap-up, the focus on custom e-badge modifications and team-based CTF performance provides a blueprint for how we should be approaching our own internal red team development.
The Badge as a Hardware Sandbox
Custom conference badges have evolved from simple blinky-lights into legitimate embedded systems. At BSidesSLC, the organizers pushed a design that wasn't just a souvenir; it was a platform. When you see a badge that allows for component-level modification—where you can physically break off parts and still maintain functionality—you are looking at a hardware sandbox.
For a pentester, this is the perfect environment to practice side-channel analysis or fault injection without the risk of bricking a production device. If you can successfully modify a badge to run a custom slideshow or execute arbitrary code, you have just practiced the same fundamental skills required to compromise an IoT gateway or a proprietary industrial controller.
The Razer BlackShark V2 Pro headsets awarded for these modifications aren't just prizes; they represent the intersection of consumer hardware and the need for low-latency, secure communication. When you are testing hardware, you need to understand how these devices handle firmware updates and peripheral communication. If you aren't spending time at these events looking at how others are dumping firmware or probing JTAG headers, you are missing the easiest way to level up your hardware exploitation game.
CTF Teams and the Power of Parallelization
The most telling moment of the ceremony was the acknowledgment of the UtahSec team’s performance in the CTF. They didn't just win; they doubled the score of the runner-up. This wasn't because they were smarter than everyone else. It was because they treated the CTF like a real-world engagement: they parallelized their efforts.
In a professional engagement, you rarely have the luxury of time. You have a scope, a deadline, and a client who wants results yesterday. If you are working a web app assessment, you should be using tools like OWASP ZAP to automate the low-hanging fruit while your team focuses on complex logic flaws. The UtahSec team’s success proves that when you divide a target into logical segments—network, application, hardware, and social engineering—you can achieve coverage that a single researcher simply cannot match.
If you are a solo bug bounty hunter, you are at a disadvantage. The most successful researchers are those who build small, trusted teams. They share payloads, they compare notes on CVE-2022-22965 (Spring4Shell) detection, and they build custom scripts to automate the boring parts of the recon phase. The BSides environment is where you find those people.
Moving Beyond the Theory
Too many researchers get stuck in the "tutorial trap." They read a write-up, they run the provided script against a lab, and they call it a day. That is not research; that is following instructions. Real research is taking a technique you saw at a conference, finding a similar implementation in a production environment, and figuring out why the vendor’s patch failed.
When you see a talk about a new exploitation technique, don't just bookmark the slides. Ask yourself: how does this apply to the tech stack I am currently testing? If the talk is about a new way to bypass Cross-Site Scripting (XSS) filters, go to your current target and see if the same logic applies.
The next time you attend a local BSides or a similar community event, skip the vendor booths. Go to the CTF room. Find the people who are struggling with a hardware challenge and offer to help. You will learn more about the reality of exploitation in two hours of collaborative troubleshooting than you will in two weeks of reading white papers. The goal is to build a network of peers who can help you solve the problems that aren't documented in any manual. That is how you stay ahead of the curve, and that is how you turn a simple conference into a career-defining experience.
Up Next From This Conference
BSides Salt Lake City Conference Opening
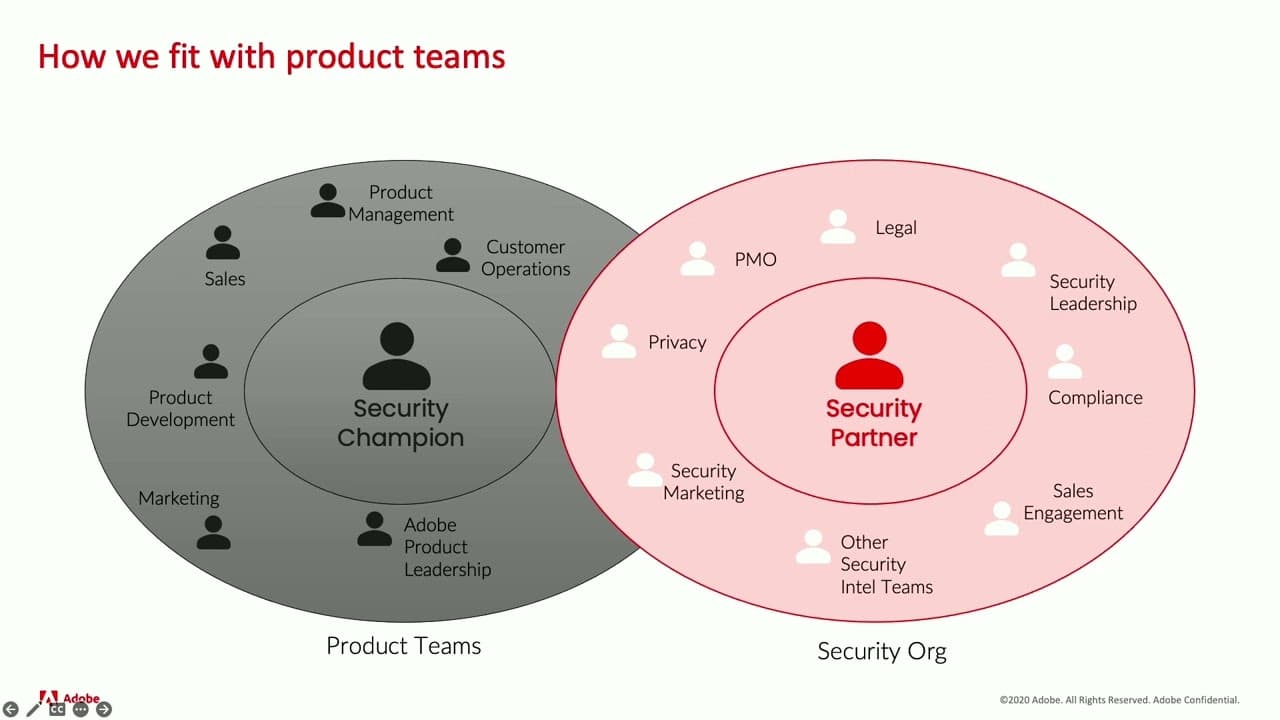
Building Stronger Relationships between Security and Engineering Teams
Why Data Breaches Aren't Like Plane Crashes, but Should Be
Similar Talks
Making and Breaking NSA's Codebreaker Challenge
Leveraging AI for Smarter Bug Bounties

